Question: CODE MUST BE WRITTEN IN PYTHON 3! We are going to code a very basic implementation of the Key Generation algorithm for RSA. The input
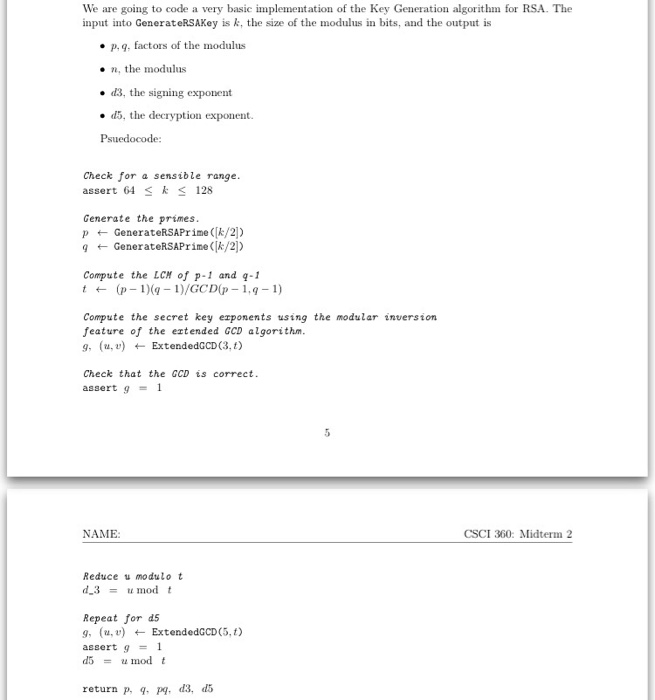
We are going to code a very basic implementation of the Key Generation algorithm for RSA. The input into GenerateRSAKey is k, the size of the modulus in bits, and the output is p, q, factors of the modulus n, the modulus d3, the signing exponent d5, the decryption exponent. Psuedocode: Check for a sensible range. assert 64 lessthanorequalto k lessthanorequalto 128 Generate the primes. P leftarrow GenerateRSAPrime ([k/2]) q leftarrow GenerateRSAPrime([k/2]) Compute the LCM of p-1 and q - 1 t leftarrow (p - 1) (q - 1)/GCD(p-1, q-1) Compute the secret key exponents using the modular inversion feature of the extended GCD algorithm. g, (u, v) leftarrow ExtendedGCD(3, t) Check that the GCD is correct. assert g = 1 Reduce u modulo t d_3 = u mod t Repeat for dS g, (u, v) leftarrow ExtendedGCD(5, t) assert g = 1 d5 = u mod t return p, q, pq, d3, d5 We are going to code a very basic implementation of the Key Generation algorithm for RSA. The input into GenerateRSAKey is k, the size of the modulus in bits, and the output is p, q, factors of the modulus n, the modulus d3, the signing exponent d5, the decryption exponent. Psuedocode: Check for a sensible range. assert 64 lessthanorequalto k lessthanorequalto 128 Generate the primes. P leftarrow GenerateRSAPrime ([k/2]) q leftarrow GenerateRSAPrime([k/2]) Compute the LCM of p-1 and q - 1 t leftarrow (p - 1) (q - 1)/GCD(p-1, q-1) Compute the secret key exponents using the modular inversion feature of the extended GCD algorithm. g, (u, v) leftarrow ExtendedGCD(3, t) Check that the GCD is correct. assert g = 1 Reduce u modulo t d_3 = u mod t Repeat for dS g, (u, v) leftarrow ExtendedGCD(5, t) assert g = 1 d5 = u mod t return p, q, pq, d3, d5
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


