Question: compare and contrast between a key and a practical reliance? [3 marks] (b) The pattern R(A, B, C, D, E) has the accompanying useful conditions.
compare and contrast between a key and a practical reliance? [3 marks] (b) The pattern R(A, B, C, D, E) has the accompanying useful conditions.
(I) What are all of the keys of R? [3 marks] (ii) Which useful conditions disregard Boyce-Codd Normal structure (BCNF)? [3 marks] (iii) Which useful conditions abuse Third Normal structure (3NF)? [3 marks] (iv) Find a lossless-join disintegration of R into BCNF relations.
(a) Let f : A ? B be a capacity with space An and range B. Show that the connection R on A characterized by (x, y) ? R ? f(x) = f(y) is an identicalness connection
(a) Describe five rules that a financial backer could use to assess a business. Which is the most significant, and why? [5 marks] (b) Distinguish among promoting and selling. [5 marks] (c) Distinguish among quantitative and subjective statistical surveying.
(a) Given the accompanying system section in C or Java static int a = 3; static int f(int x, int y) { int z = a+x; ...; return ... } make sense of how the four factors (a, x, y and z) are gotten to from inside f at the guidance level for an engineering like MIPS, ARM or x86. Pay specific consideration with regards to how and when stockpiling is dispensed for these factors, what's more, which framework parts of a standard assemble connect and-execute model are associated with choosing the guidance and deciding the run-time address estimation. Your response ought to momentarily make sense of what happens when f makes a recursive call to itself. [8 marks] (b) Suppose we stretch out the language to permit settled work definitions: static int a = 3; static int f(int x) { static int g(int y) { int z = a+x; ...; return ... } return g(7); } (I) Complete the meaning of g so that, during execution of a call to f, the contrast between the addresses allotted to x and y changes. [2 marks] (ii) Explain a potential run-time system that permits every one of the four factors to be gotten to from inside g.
In a dispersed electronic gathering application every member has a reproduction of a common whiteboard. Just a single client at an at once to the whiteboard, after which the client's update is engendered to all meeting individuals. A committed interaction deals with each whiteboard imitation. Characterize and examine a convention that the reproduction supervisors could use to accomplish this shared avoidance. [10 marks] A help information base is recreated inside a broadly conveyed framework to accomplish high accessibility and low access dormancy. Inside a pecking order of imitations a bunch of high level essential servers keep up with solid consistency of their copies. Depict how this solid consistency could be accomplished. For what reason are the accompanying assertions errors? (a) MIPS is a precise measure for looking at execution among PCs. [5 marks] (b) A benchmark is a normal program which precisely predicts the exhibition of any remaining applications. [5 marks] (c) Complex guidance set PCs limit the semantic hole between machine code and significant level dialects, consequently making applications run all the more rapidly. [5 marks] (d) Data stores generally further develop processor throughput. [5 marks] 3 Digital Communication I Compare circuit exchanging and bundle exchanging, focusing on channel qualities and asset proficiency. [7 marks] What is wave division multiplexing (WDM)? Is it more like circuit exchanging or bundle exchanging and why? [7 marks] Wave length change is the cycle, either optical or optical-electronic-optical, of getting a sign on one frequency and sending on another. How truly does frequency change facilitate the issue of directing optical transporters in an organization? [3 marks] "The immense limit of WDM frameworks will imply that IP becomes excess." Discuss.?
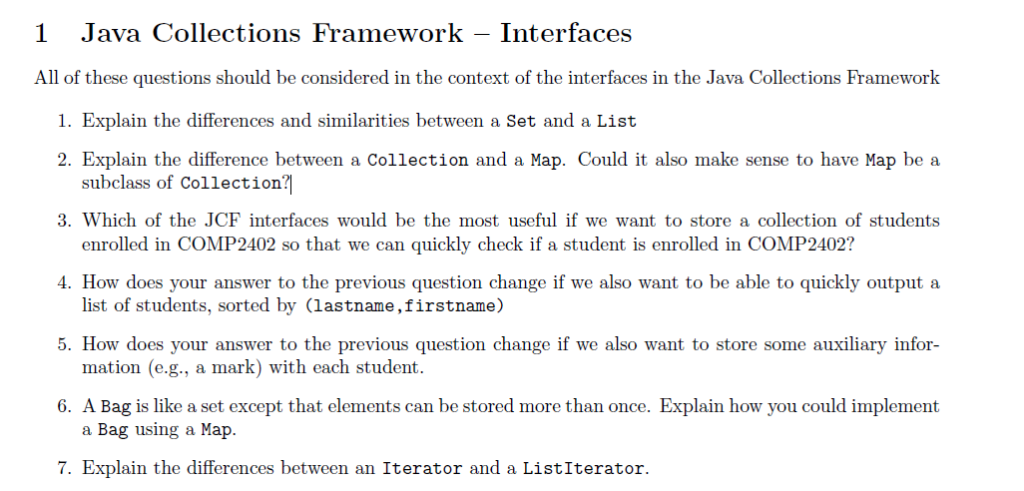
1 Java Collections Framework Interfaces All of these questions should be considered in the context of the interfaces in the Java Collections Framework 1. Explain the differences and similarities between a Set and a List 2. Explain the difference between a Collection and a Map. Could it also make sense to have Map be a subclass of Collection? 3. Which of the JCF interfaces would be the most useful if we want to store a collection of students enrolled in COMP2402 so that we can quickly check if a student is enrolled in COMP2402? 4. How does your answer to the previous question change if we also want to be able to quickly output a list of students, sorted by (lastname, firstname) 5. How does your answer to the previous question change if we also want to store some auxiliary infor- mation (e.g., a mark) with each student. 6. A Bag is like a set except that elements can be stored more than once. Explain how you could implement a Bag using a Map. 7. Explain the differences between an Iterator and a ListIterator.
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


