Question: Compromising a prominent software developer like Microsoft, Adobe, or SAP to get access to all of the entities that use their products is an example
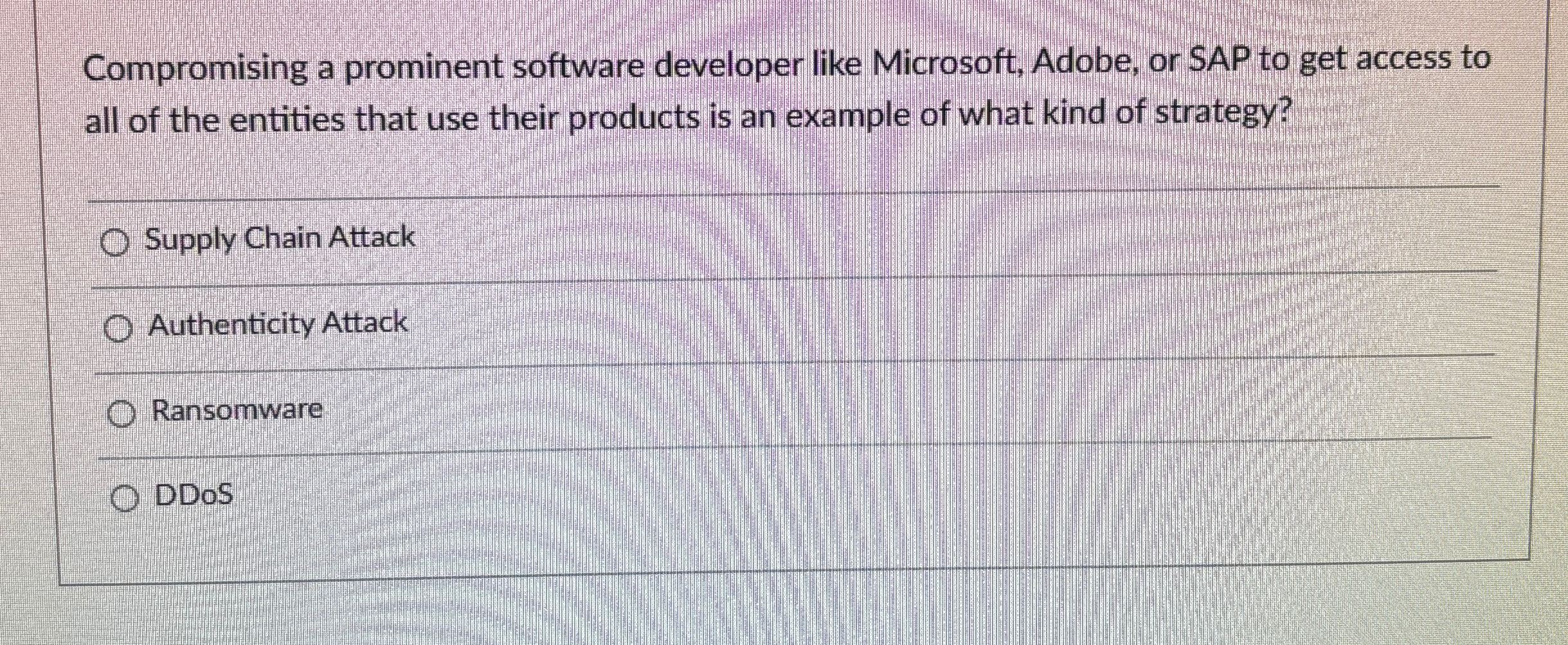
Compromising a prominent software developer like Microsoft, Adobe, or SAP to get access to all of the entities that use their products is an example of what kind of strategy?
Supply Chain Attack
Authenticity Attack
Ransomware
DDoS
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


