Question: Computer Security Briefly describe the scheme illustrated in Figure below Message MAC algorit hm Transmit Compare MAC algorithm MAC Figure 2.3 Message Authentication Using a
Computer Security
Briefly describe the scheme illustrated in Figure below
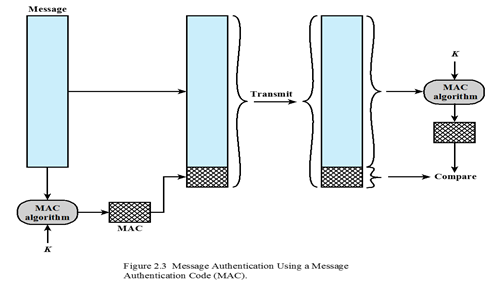
Message MAC algorit hm Transmit Compare MAC algorithm MAC Figure 2.3 Message Authentication Using a Message Authentication Code (MAC)
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


