Question: Computer Security - Replay Attacks -multiple choice question Replay Attacks Choose the best answer Question 13 2 pts Replay Attacks On Monday, Alice uses trusted
Computer Security - Replay Attacks -multiple choice question
Replay Attacks
Choose the best answer
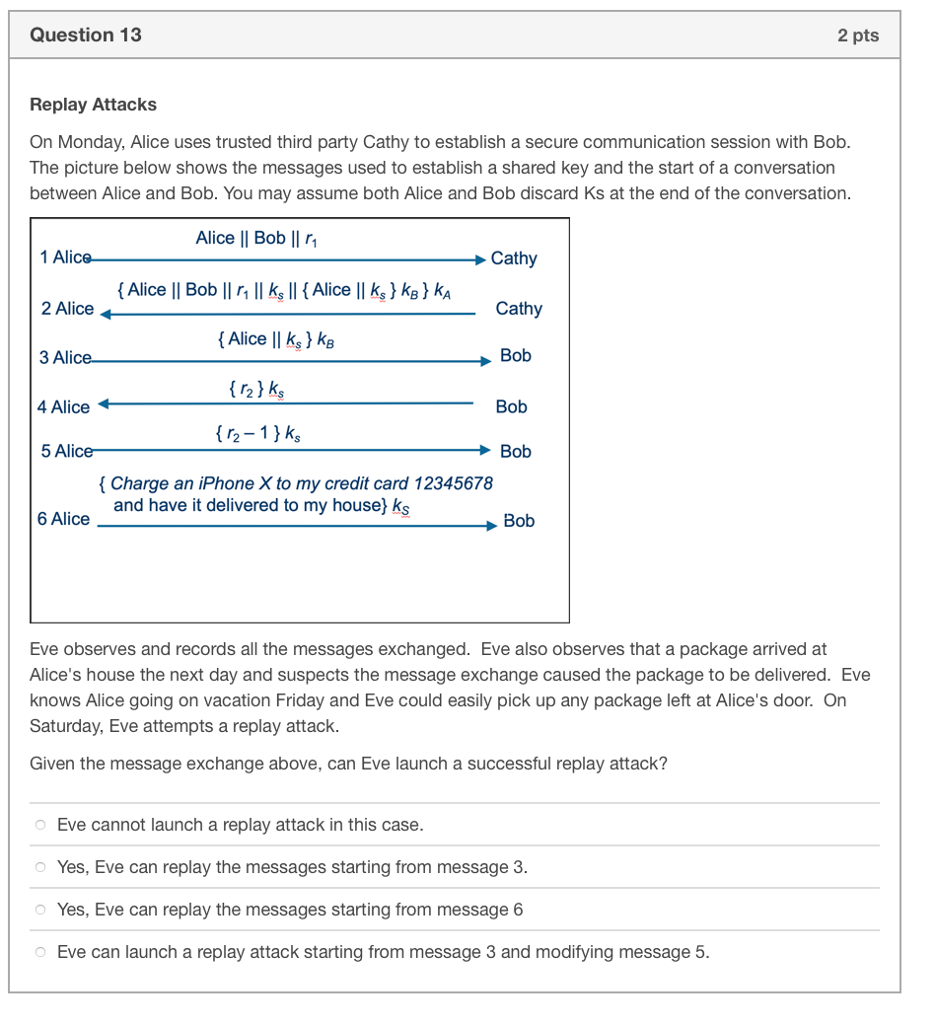
Question 13 2 pts Replay Attacks On Monday, Alice uses trusted third party Cathy to establish a secure communication session with Bob The picture below shows the messages used to establish a shared key and the start of a conversation between Alice and Bob. You may assume both Alice and Bob discard Ks at the end of the conversation Alice I| Bob ll r1 2 Alice 3 Alic 4 Alice 5 AliceBob Cathy (Alice || k,) ks Bob r21 k Bob Charge an iPhone X to my credit card 12345678 and have it delivered to my house) ks 6 Alice Bob Eve observes and records all the messages exchanged. Eve also observes that a package arrived at Alice's house the next day and suspects the message exchange caused the package to be delivered. Eve knows Alice going on vacation Friday and Eve could easily pick up any package left at Alice's door. On Saturday, Eve attempts a replay attack Given the message exchange above, can Eve launch a successful replay attack? Eve cannot launch a replay attack in this case Yes, Eve can replay the messages starting from message 3 Yes, Eve can replay the messages starting from message 6 o Eve can launch a replay attack starting from message 3 and modifying message 5
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


