Configure and Verify RIPv2 Routing Configure RIPv2 on the routers and verify that it is running....
Fantastic news! We've Found the answer you've been seeking!
Question:

Transcribed Image Text:
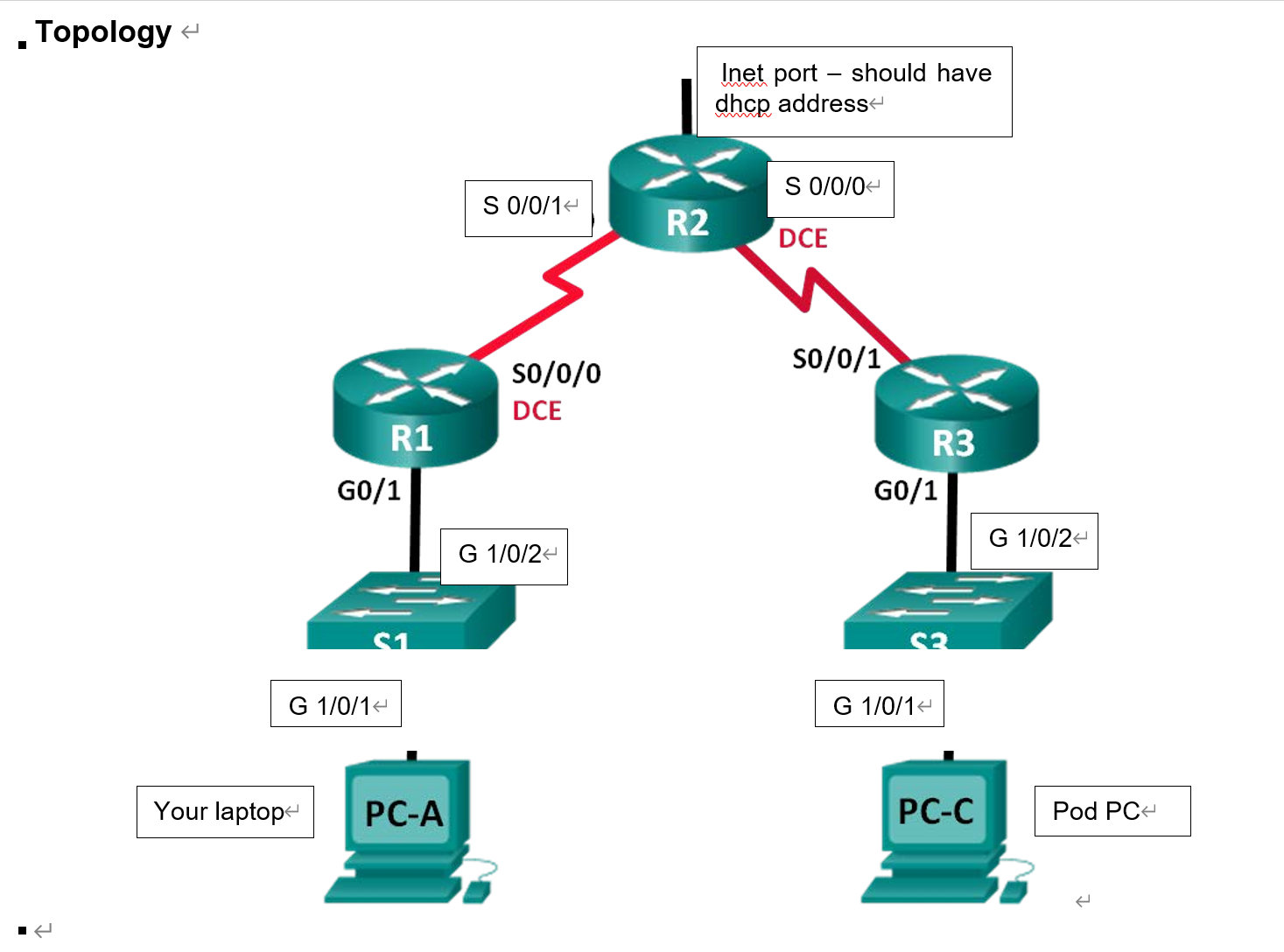
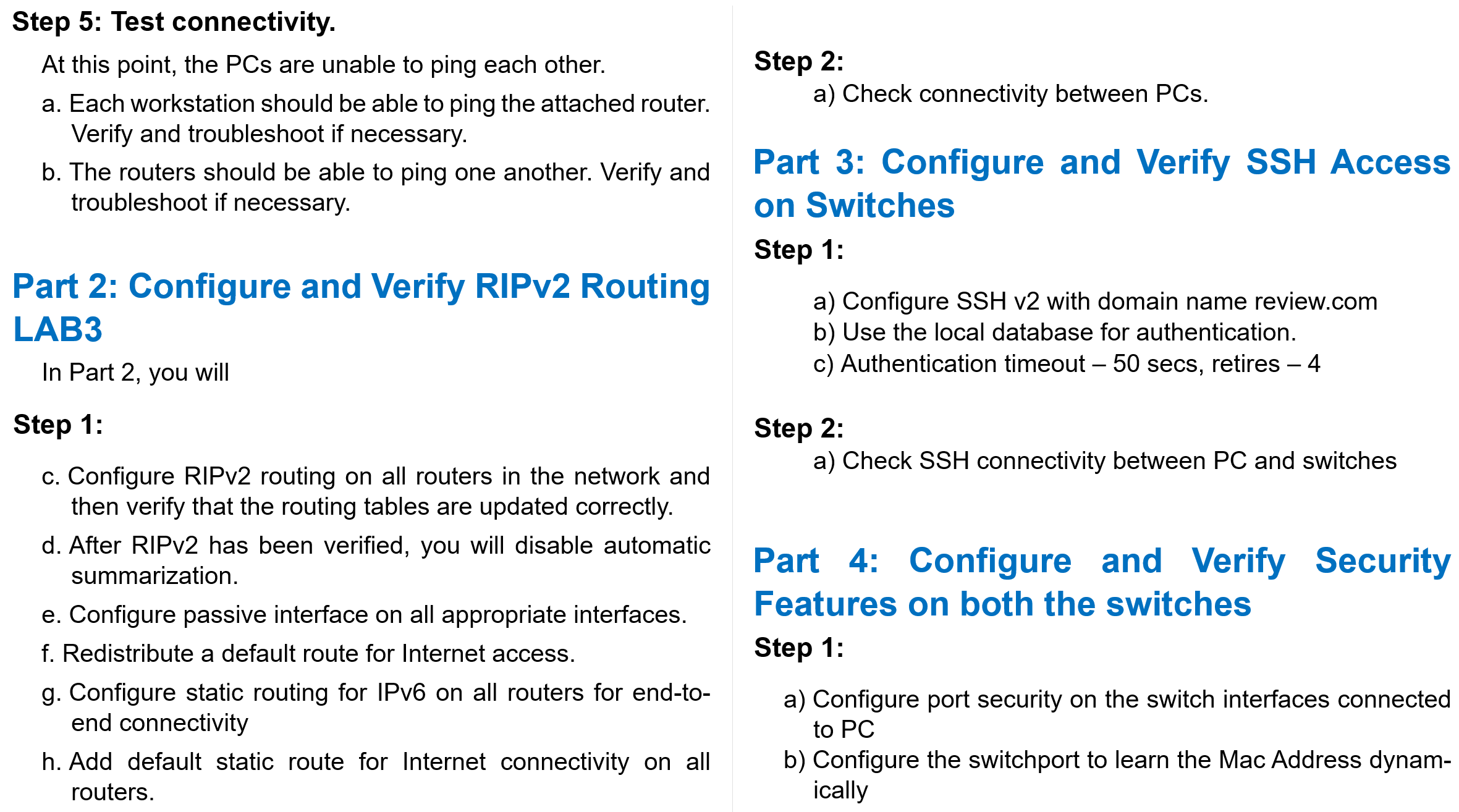
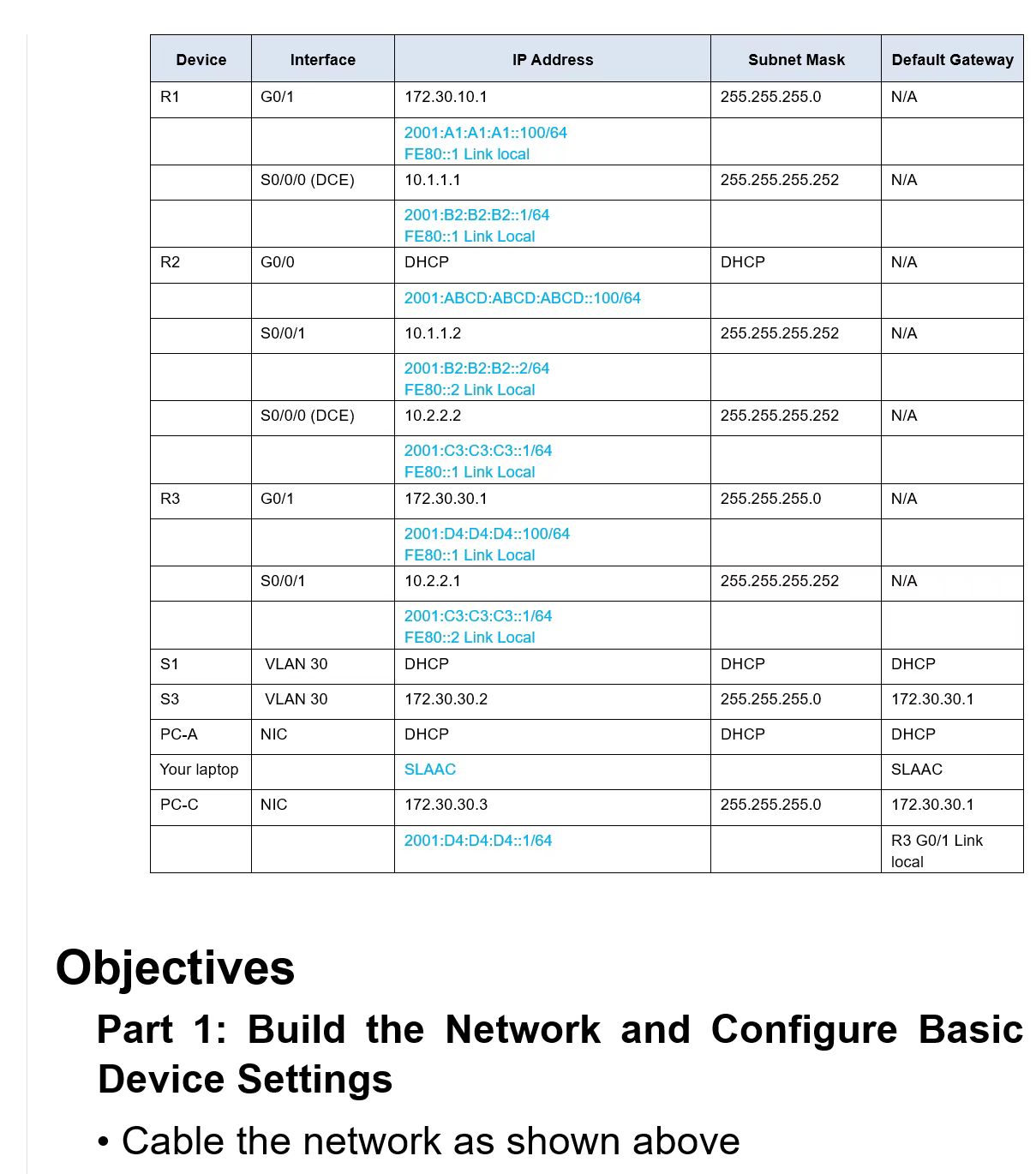
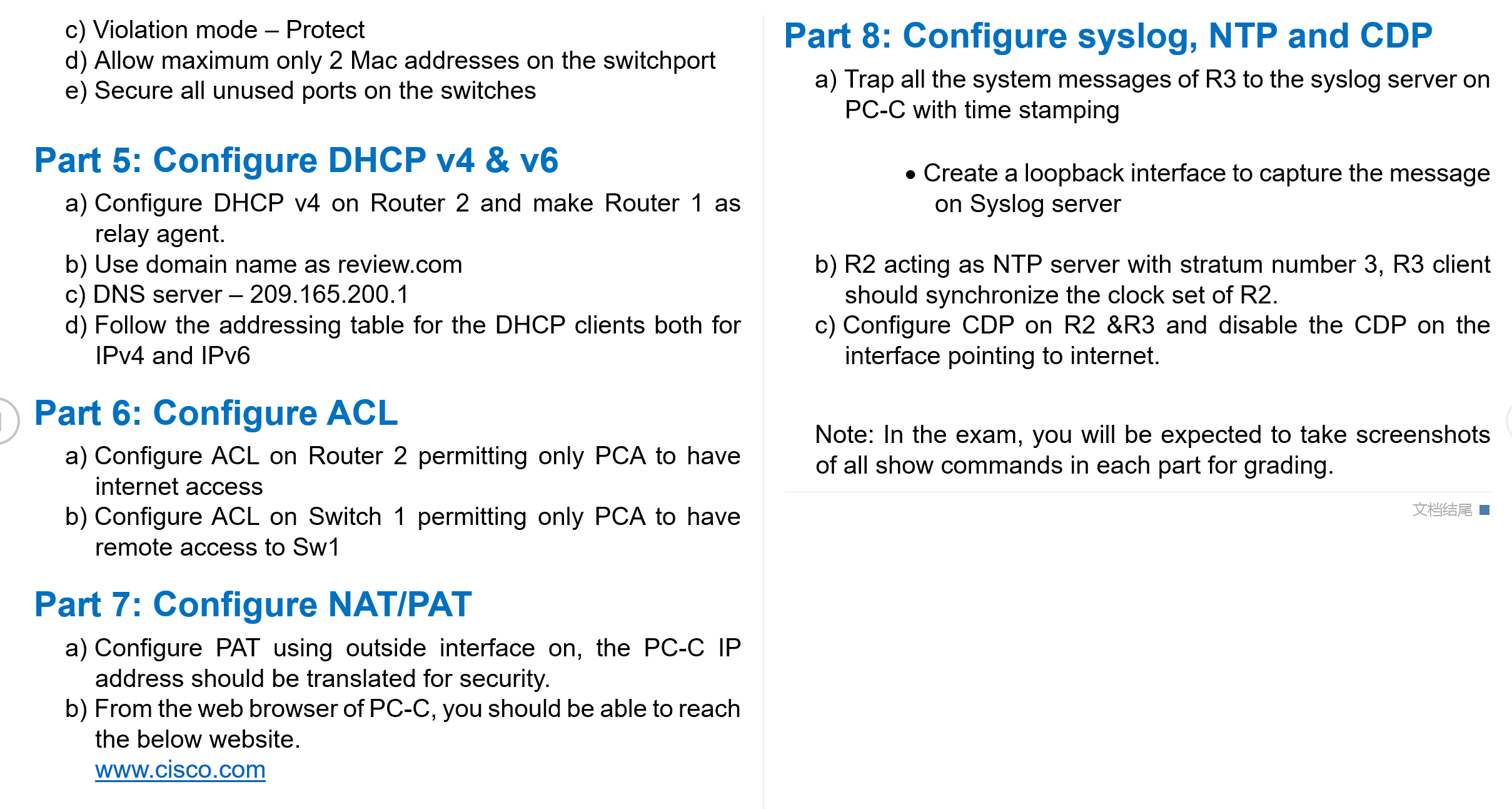
Configure and Verify RIPv2 Routing Configure RIPv2 on the routers and verify that it is running. Configure other features of RIPv2 Add static routing for IPv6 for end to end connectivity. Examine routing tables. Part 3: Configure and Verify SSH Access on Switches Configure SSH access. Modify SSH parameters. Verify the SSH configuration . . Part 4: Configure and Verify Security Features on Switches Configure and verify general security features. Configure and verify port security. Part 5: Adding Screenshots - You will be asked to add all possible verification screenshots during your test Part 1: Build the Network and Configure Basic Device Settings In Part 1, you will set up the network topology on packet tracer and configure basic settings. Step 1: Configure basic settings for R2. a. Disable DNS lookup. b. Configure device names as shown in the topology. c. Configure password encryption. d. Assign review as the privileged EXEC password. e. Assign review as the console and vty passwords. f. Configure a MOTD banner to warn users that unauthorized access is prohibited. g. Configure logging synchronous for the console line. h. Configure a description for each interface with an IP ad- dress. i. Configure the clock rate, if applicable, to the DCE serial interface. Step 4: Configure IP Addressing. Refer to the Addressing Table for IP address information of all the devices. . Topology < Your laptop R1 GO/1 G 1/0/1 < PC-A S 0/0/1 < SO/0/0 DCE G 1/0/2 < R2 Inet port should have dhcp address S 0/0/0 < DCE SO/0/1 R3 GO/1 G 1/0/1 PC-C G 1/0/2 < Pod PC Step 5: Test connectivity. At this point, the PCs are unable to ping each other. a. Each workstation should be able to ping the attached router. Verify and troubleshoot if necessary. b. The routers should be able to ping one another. Verify and troubleshoot if necessary. Part 2: Configure and Verify RIPv2 Routing LAB3 In Part 2, you will Step 1: c. Configure RIPv2 routing on all routers in the network and then verify that the routing tables are updated correctly. d. After RIPv2 has been verified, you will disable automatic summarization. e. Configure passive interface on all appropriate interfaces. f. Redistribute a default route for Internet access. g. Configure static routing for IPv6 on all routers for end-to- end connectivity h. Add default static route for Internet connectivity on all routers. Step 2: a) Check connectivity between PCs. Part 3: Configure and Verify SSH Access on Switches Step 1: a) Configure SSH v2 with domain name review.com b) Use the local database for authentication. c) Authentication timeout - 50 secs, retires 4 Step 2: a) Check SSH connectivity between PC and switches Part 4: Configure and Verify Security Features on both the switches Step 1: a) Configure port security on the switch interfaces connected to PC b) Configure the switchport to learn the Mac Address dynam- ically Device R1 R2 R3 S1 S3 PC-A Your laptop PC-C G0/1 Interface S0/0/0 (DCE) GO/0 S0/0/1 S0/0/0 (DCE) G0/1 S0/0/1 VLAN 30 VLAN 30 NIC NIC 172.30.10.1 2001: A1:A1:A1::100/64 FE80::1 Link local 10.1.1.1 2001:B2:B2:B2::1/64 FE80::1 Link Local DHCP 2001:ABCD:ABCD:ABCD::100/64 10.1.1.2 IP Address 2001:B2:B2:B2::2/64 FE80::2 Link Local 10.2.2.2 2001:C3:C3:C3::1/64 FE80::1 Link Local 172.30.30.1 2001:D4:D4:D4::100/64 FE80::1 Link Local 10.2.2.1 2001:C3:C3:C3::1/64 FE80::2 Link Local DHCP 172.30.30.2 DHCP SLAAC 172.30.30.3 2001:D4:D4:D4::1/64 Subnet Mask 255.255.255.0 255.255.255.252 DHCP 255.255.255.252 255.255.255.252 255.255.255.0 255.255.255.252 DHCP 255.255.255.0 DHCP 255.255.255.0 Default Gateway N/A N/A N/A N/A N/A N/A N/A DHCP 172.30.30.1 DHCP SLAAC 172.30.30.1 R3 G0/1 Link local Objectives Part 1: Build the Network and Configure Basic Device Settings Cable the network as shown above c) Violation mode - Protect d) Allow maximum only 2 Mac addresses on the switchport e) Secure all unused ports on the switches Part 5: Configure DHCP v4 & v6 a) Configure DHCP v4 on Router 2 and make Router 1 as relay agent. b) Use domain name as review.com c) DNS server - 209.165.200.1 d) Follow the addressing table for the DHCP clients both for IPv4 and IPv6 Part 6: Configure ACL a) Configure ACL on Router 2 permitting only PCA to have internet access b) Configure ACL on Switch 1 permitting only PCA to have remote access to Sw1 Part 7: Configure NAT/PAT a) Configure PAT using outside interface on, the PC-C IP address should be translated for security. b) From the web browser of PC-C, you should be able to reach the below website. www.cisco.com Part 8: Configure syslog, NTP and CDP a) Trap all the system messages of R3 to the syslog server on PC-C with time stamping Create a loopback interface to capture the message on Syslog server b) R2 acting as NTP server with stratum number 3, R3 client should synchronize the clock set of R2. c) Configure CDP on R2 &R3 and disable the CDP on the interface pointing to internet. Note: In the exam, you will be expected to take screenshots of all show commands in each part for grading. Configure and Verify RIPv2 Routing Configure RIPv2 on the routers and verify that it is running. Configure other features of RIPv2 Add static routing for IPv6 for end to end connectivity. Examine routing tables. Part 3: Configure and Verify SSH Access on Switches Configure SSH access. Modify SSH parameters. Verify the SSH configuration . . Part 4: Configure and Verify Security Features on Switches Configure and verify general security features. Configure and verify port security. Part 5: Adding Screenshots - You will be asked to add all possible verification screenshots during your test Part 1: Build the Network and Configure Basic Device Settings In Part 1, you will set up the network topology on packet tracer and configure basic settings. Step 1: Configure basic settings for R2. a. Disable DNS lookup. b. Configure device names as shown in the topology. c. Configure password encryption. d. Assign review as the privileged EXEC password. e. Assign review as the console and vty passwords. f. Configure a MOTD banner to warn users that unauthorized access is prohibited. g. Configure logging synchronous for the console line. h. Configure a description for each interface with an IP ad- dress. i. Configure the clock rate, if applicable, to the DCE serial interface. Step 4: Configure IP Addressing. Refer to the Addressing Table for IP address information of all the devices. . Topology < Your laptop R1 GO/1 G 1/0/1 < PC-A S 0/0/1 < SO/0/0 DCE G 1/0/2 < R2 Inet port should have dhcp address S 0/0/0 < DCE SO/0/1 R3 GO/1 G 1/0/1 PC-C G 1/0/2 < Pod PC Step 5: Test connectivity. At this point, the PCs are unable to ping each other. a. Each workstation should be able to ping the attached router. Verify and troubleshoot if necessary. b. The routers should be able to ping one another. Verify and troubleshoot if necessary. Part 2: Configure and Verify RIPv2 Routing LAB3 In Part 2, you will Step 1: c. Configure RIPv2 routing on all routers in the network and then verify that the routing tables are updated correctly. d. After RIPv2 has been verified, you will disable automatic summarization. e. Configure passive interface on all appropriate interfaces. f. Redistribute a default route for Internet access. g. Configure static routing for IPv6 on all routers for end-to- end connectivity h. Add default static route for Internet connectivity on all routers. Step 2: a) Check connectivity between PCs. Part 3: Configure and Verify SSH Access on Switches Step 1: a) Configure SSH v2 with domain name review.com b) Use the local database for authentication. c) Authentication timeout - 50 secs, retires 4 Step 2: a) Check SSH connectivity between PC and switches Part 4: Configure and Verify Security Features on both the switches Step 1: a) Configure port security on the switch interfaces connected to PC b) Configure the switchport to learn the Mac Address dynam- ically Device R1 R2 R3 S1 S3 PC-A Your laptop PC-C G0/1 Interface S0/0/0 (DCE) GO/0 S0/0/1 S0/0/0 (DCE) G0/1 S0/0/1 VLAN 30 VLAN 30 NIC NIC 172.30.10.1 2001: A1:A1:A1::100/64 FE80::1 Link local 10.1.1.1 2001:B2:B2:B2::1/64 FE80::1 Link Local DHCP 2001:ABCD:ABCD:ABCD::100/64 10.1.1.2 IP Address 2001:B2:B2:B2::2/64 FE80::2 Link Local 10.2.2.2 2001:C3:C3:C3::1/64 FE80::1 Link Local 172.30.30.1 2001:D4:D4:D4::100/64 FE80::1 Link Local 10.2.2.1 2001:C3:C3:C3::1/64 FE80::2 Link Local DHCP 172.30.30.2 DHCP SLAAC 172.30.30.3 2001:D4:D4:D4::1/64 Subnet Mask 255.255.255.0 255.255.255.252 DHCP 255.255.255.252 255.255.255.252 255.255.255.0 255.255.255.252 DHCP 255.255.255.0 DHCP 255.255.255.0 Default Gateway N/A N/A N/A N/A N/A N/A N/A DHCP 172.30.30.1 DHCP SLAAC 172.30.30.1 R3 G0/1 Link local Objectives Part 1: Build the Network and Configure Basic Device Settings Cable the network as shown above c) Violation mode - Protect d) Allow maximum only 2 Mac addresses on the switchport e) Secure all unused ports on the switches Part 5: Configure DHCP v4 & v6 a) Configure DHCP v4 on Router 2 and make Router 1 as relay agent. b) Use domain name as review.com c) DNS server - 209.165.200.1 d) Follow the addressing table for the DHCP clients both for IPv4 and IPv6 Part 6: Configure ACL a) Configure ACL on Router 2 permitting only PCA to have internet access b) Configure ACL on Switch 1 permitting only PCA to have remote access to Sw1 Part 7: Configure NAT/PAT a) Configure PAT using outside interface on, the PC-C IP address should be translated for security. b) From the web browser of PC-C, you should be able to reach the below website. www.cisco.com Part 8: Configure syslog, NTP and CDP a) Trap all the system messages of R3 to the syslog server on PC-C with time stamping Create a loopback interface to capture the message on Syslog server b) R2 acting as NTP server with stratum number 3, R3 client should synchronize the clock set of R2. c) Configure CDP on R2 &R3 and disable the CDP on the interface pointing to internet. Note: In the exam, you will be expected to take screenshots of all show commands in each part for grading.
Expert Answer:

Related Book For 

Income Tax Fundamentals 2013
ISBN: 9781285586618
31st Edition
Authors: Gerald E. Whittenburg, Martha Altus Buller, Steven L Gill
Posted Date:
Students also viewed these computer network questions
-
Nisha has completed her MBA and has joined a company which was going to raise fund from long term sources such as Debt and Equity. Nisha was asked by her manager to prepare a report on which could be...
-
An object has a total energy of 5.0 1015 J and a kinetic energy of 2.0 1015 J. What is the magnitude of the object's relativistic momentum?
-
The demand and supply schedules for potato chips are in the table. a. What are the equilibrium price and equilibrium quantity of potato chips? b. If chips were 60 cents a bag, describe the situation...
-
If people pay for good weather, who ultimately receives the good-weather payment?
-
What defense will Ragged Mountain probably assert? Alaina Sweeney went to Ragged Mountain Ski Resort in New Hampshire with a friend. Alaina went snow tubing down a snow-tube run designed exclusively...
-
QUESTION 3 (20 MKS) a) Obtain the time-independent Schrodinger Wave equation from the time dependent equation. [10 mks] b) Solve the time-independent Schrodinger equation given that,(x) = Aekx [10...
-
An appraiser should have no undisclosed financial interest in the results of an appraisal. This standard is intended to ensure impartiality confidentiality cost effectiveness competency
-
Artificial intelligence is becoming increasingly popular in the workplace. However, there have been some complaints regarding its use in education and other fields. Should the use of artificial...
-
Please write a two-page Formal Analysis (consider art elements and principles of design) on a film by any of these expertly directed film masters: Any of these 10 films considered the best directed...
-
From the top of a cliff, a person throws a stone straight downward. The initial speed of the stone just after leaving the person's hand is 9.4 m/s. (a) What is the acceleration (magnitude in m/s and...
-
2. Create the following html page using internal CSS with the same styles as described with green background page Header 3 is red verdana Header 4 is white calibri italic Header 3 is blue arial...
-
What can you do to improve your emotional intelligence skills? List three goals/strategies you can implement to improve your emotional intelligence skills. Do you think EQ predicts more career...
-
There are many ways a teenager can contribute to society. Start from your school. Join student council and other volunteer groups. Take a leadership role in your class and in the school. Use your...
-
Is it a breach of fiduciary duty for a director of a real estate investment trust (REIT) negotiating a joint venture on behalf of the REIT with another director for the development of a portfolio of...
-
Sherry rents her vacation home for 6 months and lives in it for 6 months during the year. Her gross rental income during the year is $4,000. Total real estate taxes for the home are $950, and...
-
Diane is a single taxpayer who qualifies for the earned income credit. Diane has two qualifying children who are 3 and 5 years old. During 2012, Diane's wages are $17,100 and she receives dividend...
-
Steve Drake sells a rental house on January 1, 2012, and receives $130,000 cash and a note for $55,000 at 10 percent interest. The purchaser also assumes the mortgage on the property of $45,000....
-
Tumor-suppressor genes promote cancer when a. they are overexpressed. b. they are expressed in the wrong cell type. c. their function is inactivated. d. they are expressed at the wrong stage of...
-
Explain how DNA microarrays are used in molecular profiling of cancerous tumors.
-
Which of the following types of epigenetic changes may promote cancer? a. DNA methylation b. Covalent modification of histones c. Chromatin remodeling d. All of the above may promote cancer.

Study smarter with the SolutionInn App


