Question: Consider a candidate cryptosystem that is used to encrypt a message m with key k where k is an integer chosen randomly between 1
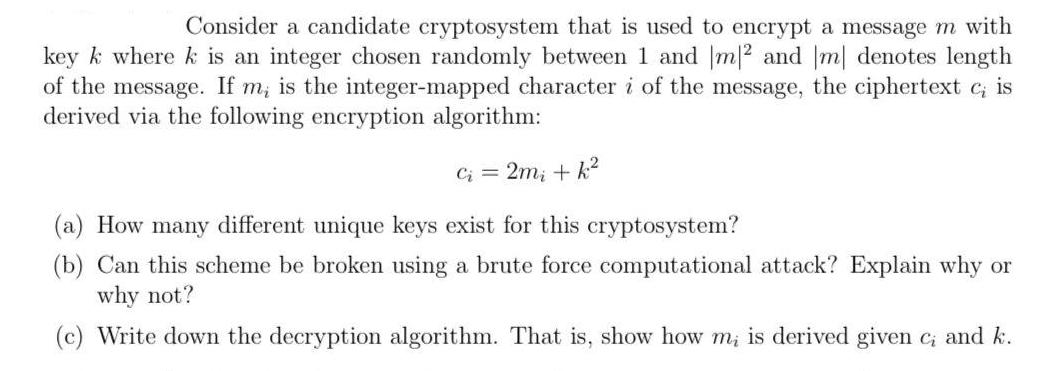
Consider a candidate cryptosystem that is used to encrypt a message m with key k where k is an integer chosen randomly between 1 and m/2 and [m] denotes length of the message. If m, is the integer-mapped character i of the message, the ciphertext c; is derived via the following encryption algorithm: Ci = 2m + f (a) How many different unique keys exist for this cryptosystem? (b) Can this scheme be broken using a brute force computational attack? Explain why or why not? (c) Write down the decryption algorithm. That is, show how m, is derived given c, and k.
Step by Step Solution
There are 3 Steps involved in it
Pg No01 Solution Given datar Q 4 7 Points Consider a candidate Cryptosystem that is used to encrypt ... View full answer

Get step-by-step solutions from verified subject matter experts


