Question: Consider the attack on TCP authentication illustrated in Figure 9.28. Suppose that Trudy cannot guess the initial sequence number 62 exactly. Instead, Trudy can only
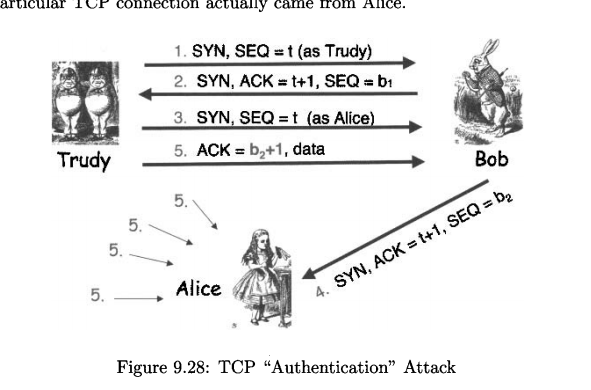
Consider the attack on TCP authentication illustrated in Figure 9.28. Suppose that Trudy cannot guess the initial sequence number 62 exactly. Instead, Trudy can only narrow 62 down to one of, say, 1,000 possible values. How can Trudy conduct an attack so that she is likely to succeed?
ariculr 1oh connecion actually cme rom Allce. I SYN, SEQ 2. SYN, ACK t (as Trudy) t+1, SEQbi af 3. SYN, SEQ t (as Alice) 5. ACK b2+1, data Trudy Bob 5. 5. 5. 5. Alice 4. SYN, ACK t+1, SEQ b2 Figure 9.28: TCP "Authentication" Attack ariculr 1oh connecion actually cme rom Allce. I SYN, SEQ 2. SYN, ACK t (as Trudy) t+1, SEQbi af 3. SYN, SEQ t (as Alice) 5. ACK b2+1, data Trudy Bob 5. 5. 5. 5. Alice 4. SYN, ACK t+1, SEQ b2 Figure 9.28: TCP "Authentication" Attack
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


