Question: Consider the C program below. It has a buffer overflow weakness. List steps required to exploit this weakness and overwrite the return pointer (EIP) stored
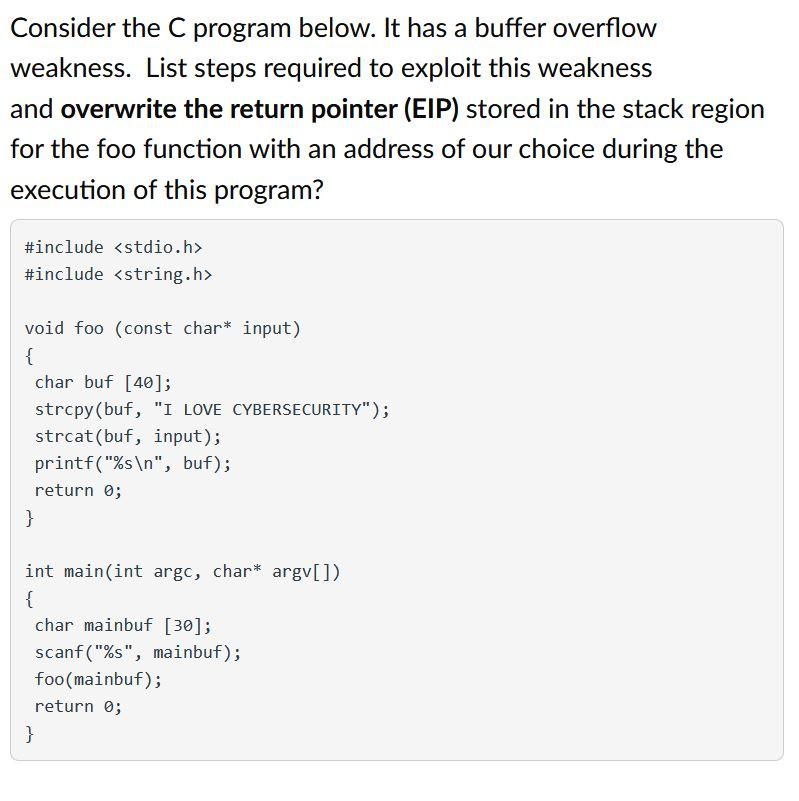
Consider the C program below. It has a buffer overflow weakness. List steps required to exploit this weakness and overwrite the return pointer (EIP) stored in the stack region for the foo function with an address of our choice during the execution of this program? #include
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


