Question: Consider the following challenge-response authentication protocols: Explain which of Protocols 2 and 3 are vulnerable to an off-line key recovery attack, justifying your answers carefully.
Consider the following challenge-response authentication protocols:
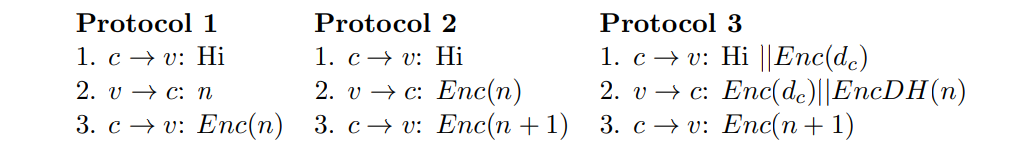
Explain which of Protocols 2 and 3 are vulnerable to an off-line key recovery attack, justifying your answers carefully.
Protocol 1 Protocol 2 Protocol 3 1. c
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


