Question: consider the following code. def func(a, b): return a + b result = func(1, 2) * func('hello', 'world') What will the value of result
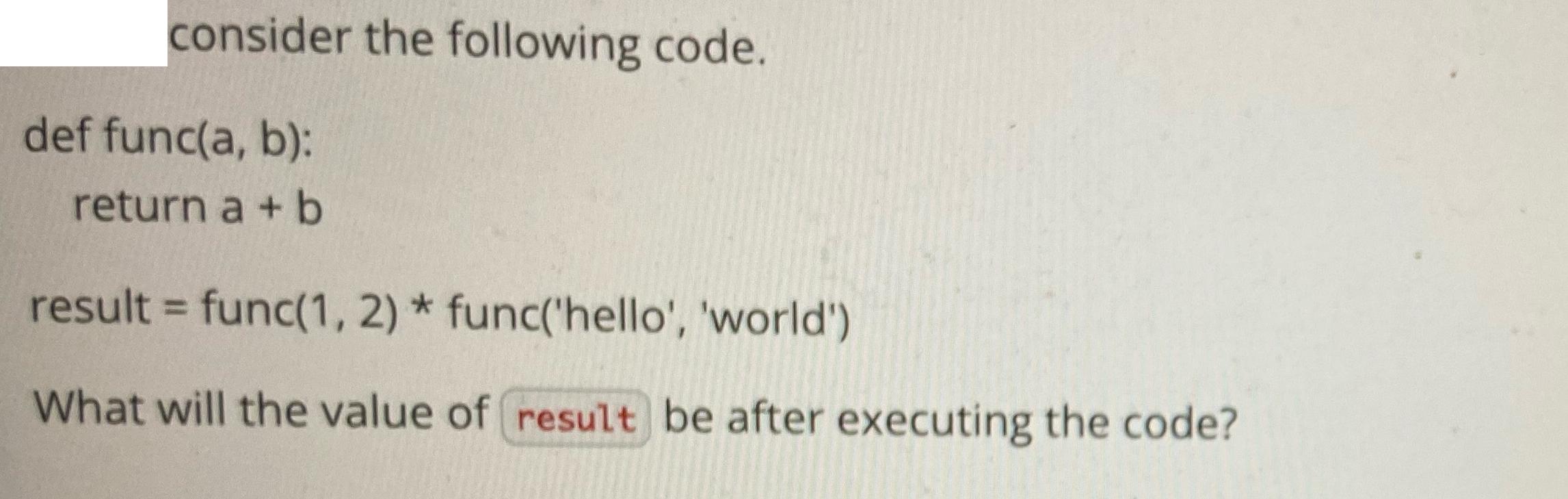
consider the following code. def func(a, b): return a + b result = func(1, 2) * func('hello', 'world') What will the value of result be after executing the code?
Step by Step Solution
There are 3 Steps involved in it
Answer Lets analyze the code step by step The function fun... View full answer

Get step-by-step solutions from verified subject matter experts


