Consider the following encryption scheme: To encrypt a message of size 2n bits, first break it...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
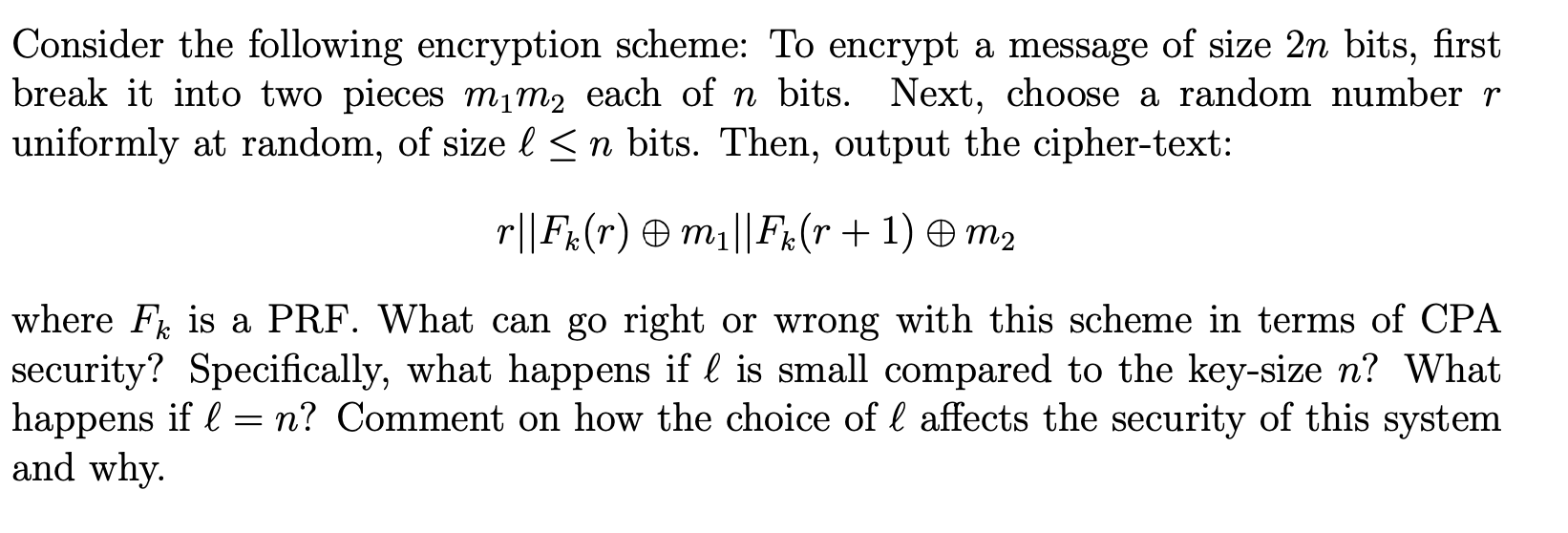
Consider the following encryption scheme: To encrypt a message of size 2n bits, first break it into two pieces m₁m2 each of n bits. Next, choose a random number r uniformly at random, of size l≤n bits. Then, output the cipher-text: r||Fk(r) – m₁||Fk (r + 1) © m₂ where F is a PRF. What can go right or wrong with this scheme in terms of CPA security? Specifically, what happens if is small compared to the key-size n? What happens if = n? Comment on how the choice of affects the security of this system and why. Consider the following encryption scheme: To encrypt a message of size 2n bits, first break it into two pieces m₁m2 each of n bits. Next, choose a random number r uniformly at random, of size l≤n bits. Then, output the cipher-text: r||Fk(r) – m₁||Fk (r + 1) © m₂ where F is a PRF. What can go right or wrong with this scheme in terms of CPA security? Specifically, what happens if is small compared to the key-size n? What happens if = n? Comment on how the choice of affects the security of this system and why.
Expert Answer:

Related Book For 

Data Structures and Algorithms in Java
ISBN: 978-1118771334
6th edition
Authors: Michael T. Goodrich, Roberto Tamassia, Michael H. Goldwasser
Posted Date:
Students also viewed these programming questions
-
For a material requirements planning (MRP) system to determine what is required to make a product, what 3 documents are necessary? What information do each of these documents provide?
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Below are total utilities cost for Gold's Gym. Using the high-low method, what are the forecasted utilities cost for August if the gym had 3,200 customers come to the gym? (assume this is still...
-
Describe six danger signs of a bust-out artist.
-
At the Fermilab accelerator in Batavia, Illinois, protons having momentum 4.80 x 10-16 kg #m/s are held in a circular orbit of radius 1.00 km by an upward magnetic field. What is the magnitude of...
-
Let X1,... ,Xn be iid n(,2). Find a function of S2, the sample variance, say g(S2), that satisfies Eg(S2) = . (Hint: Try g(S2) = cS2, where c is a constant.)
-
Eco Manufacturing Ltd produces timber felling machines for the forestry industry around the world. Its two machines are the Tree Toppler, which cuts down trees and clears undergrowth, and the Timber...
-
A vibrating string 50.0 cm long is under a tension of 1.00 N. The results from five successive stroboscopic pictures are shown in Fig. 15.39. The strobe rate is set at 5000 flashes per minute, and...
-
What's Your Understanding of Governance to Deliver Long-term Value and Performance? How can a governance and accountability framework can help to develop long-term value for the company and ensure it...
-
The bookkeeper has prepared a preliminary trial balance of Suzzy and Daryl for the year ended 31 December as follows. GH Capital account Profit and loss account at 1 January Bank loan Debtors and...
-
Is it appropriate to send an email and call the individual the same day to ask if they have received your email
-
Moana and Jane are employed by Sobecal (a pharmaceutical company) to research and develop new pharmaceuticals. Moana and Jane are full of enthusiasm for research, so at weekends they often carry out...
-
Why is having knowledge and the capability to creatively apply that knowledge in creating unique solutions for their buyers so important for today's salesperson?
-
In the event that oil prices increase sharply, or there is a Global spike in terrorist attacks: Does the event affect aggregate demand (AD) or aggregate supply (AS)? Is the event's effect on AD or AS...
-
Explain, The experimental studies in Section 5 challenge the idea of self-interest in economics and government policies. They show that people are motivated by factors beyond material incentives,...
-
How do ecological niche dynamics contribute to the maintenance of biodiversity, and what mechanisms underlie species coexistence and competition within complex ecological communities?
-
Which one of the following ray diagrams is correct for the ray of light incident on a lens as shown in figure? [NCERT Exemplar] 3 NTI Nall
-
In Exercises 15 through 30, find the derivative dy/dx. In some of these problems, you may need to use implicit differentiation or logarithmic differentiation. y ex + et -2x 1 + e
-
Al says he can prove that all sheep in a flock are the same color: Base case: One sheep. It is clearly the same color as itself. Induction step: A flock of n sheep. Take a sheep, a, out. The...
-
The PredatoryCreditCard class provides a processMonth( ) method that models the completion of a monthly cycle. Modify the class so that once a customer has made ten calls to charge during a month,...
-
Suppose you are given two circularly linked lists, L and M. Describe an algorithm for telling if L and M store the same sequence of elements (but perhaps with different starting points).
-
Draw the magnetic field lines associated with the magnets in Figures \(27.1 b-d\) (both outside and inside the magnets). Assume that the pole on the left of each magnet is the north pole. Figure 27.1...
-
For each situation shown in Figure 27.28, apply the appropriate right-hand rule to determine the direction at position \(\mathrm{P}\) of the magnetic field generated by the current-carrying wire....
-
For each situation in Figures \(27.20a, 27.20 b\), and \(27.21 a\), reverse the polarity of the magnet and then apply the appropriate right-hand rule to determine the direction of the force exerted...

Study smarter with the SolutionInn App