Question: Consider the following message authentication code: H: {0, 1}* {0, 1}n H(m) = = m mod k where k is an n-bit secret. (n
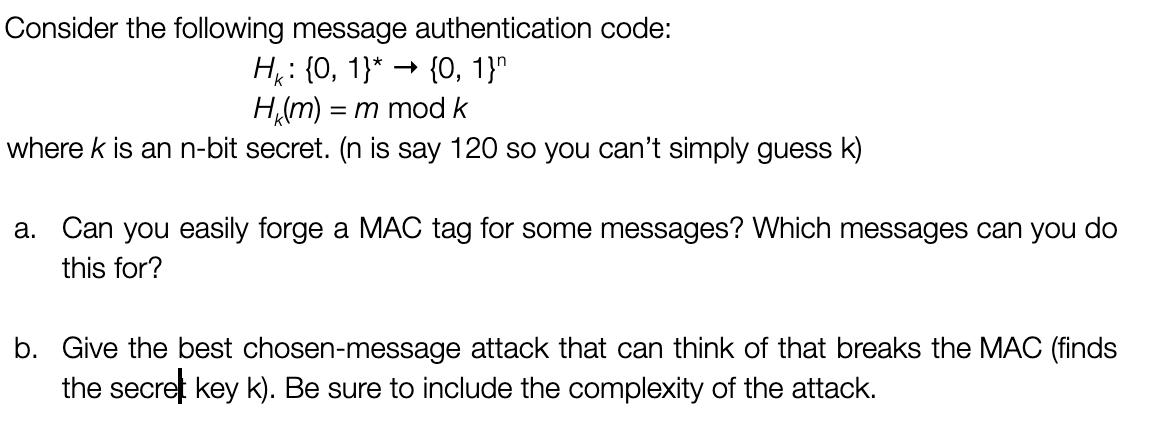
Consider the following message authentication code: H: {0, 1}* {0, 1}n H(m) = = m mod k where k is an n-bit secret. (n is say 120 so you can't simply guess k) a. Can you easily forge a MAC tag for some messages? Which messages can you do this for? b. Give the best chosen-message attack that can think of that breaks the MAC (finds the secret key k). Be sure to include the complexity of the attack.
Step by Step Solution
3.50 Rating (150 Votes )
There are 3 Steps involved in it
a Can you easily forge a MAC tag for some messages Which messages can you do this for Yesyou can easily forge a MAC tag for any message that is equal to the secret key k mod kFor exampleif the secret ... View full answer

Get step-by-step solutions from verified subject matter experts


