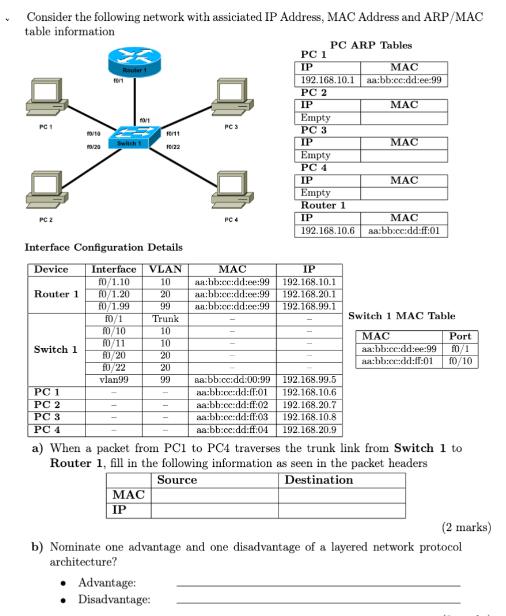
Consider the following network with assiciated IP Address, MAC Address and ARP/MAC table information PC 1...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
Consider the following network with assiciated IP Address, MAC Address and ARP/MAC table information PC 1 PC 2 Switch 1 10/10 10/20 PC 1 PC 2 PC 3 PC 4 Router 1011 Switch Interface Configuration Details Device Interface VLAN f0/1.10 10 Router 1 f0/1.20 20 99 10/1 10/1.99 f0/1 10/10 10/11 f0/20 f0/22 vlan99 F011 10:22 MAC IP Trunk 10 10 20 20 99 • Advantage: • Disadvantage: PC S PC 4 PC 1 IP PC ARP Tables MAC 192.168.10.1 aa:bb:cc:dd:ee:99 PC 2 IP MAC Empty PC 3 IP Empty PC 4 IP Empty Router 1 IP 192.168.10.6 MAC aa:bb:cc:dd:ee:99 IP 192.168.10.1 aa:bb:cc:dd:ee:99 192.168.20.1 aa:bb:cc:dd:ce:99 192.168.99.1 aa:bb:cc:dd:00:99 192.168.99.5 aa:bb:cc:dd:ff:01 192.168.10.6 aa:bb:cc:dd:ff:02 192.168.20.7 aa:bb:ce:dd:ff:03 192.168.10.8 aa:bb:cc:dd:ff:04 192.168.20.9 MAC MAC MAC aa:bb:cc:dd:ff:01 MAC Switch 1 MAC Table a) When a packet from PC1 to PC4 traverses the trunk link from Switch 1 to Router 1, fill in the following information as seen in the packet headers Source Destination Port aa:bb:cc:dd:ee:99 f0/1 aa:bb:cc:dd:ff:01 10/10 (2 marks) b) Nominate one advantage and one disadvantage of a layered network protocol architecture? Consider the following network with assiciated IP Address, MAC Address and ARP/MAC table information PC 1 PC 2 Switch 1 10/10 10/20 PC 1 PC 2 PC 3 PC 4 Router 1011 Switch Interface Configuration Details Device Interface VLAN f0/1.10 10 Router 1 f0/1.20 20 99 10/1 10/1.99 f0/1 10/10 10/11 f0/20 f0/22 vlan99 F011 10:22 MAC IP Trunk 10 10 20 20 99 • Advantage: • Disadvantage: PC S PC 4 PC 1 IP PC ARP Tables MAC 192.168.10.1 aa:bb:cc:dd:ee:99 PC 2 IP MAC Empty PC 3 IP Empty PC 4 IP Empty Router 1 IP 192.168.10.6 MAC aa:bb:cc:dd:ee:99 IP 192.168.10.1 aa:bb:cc:dd:ee:99 192.168.20.1 aa:bb:cc:dd:ce:99 192.168.99.1 aa:bb:cc:dd:00:99 192.168.99.5 aa:bb:cc:dd:ff:01 192.168.10.6 aa:bb:cc:dd:ff:02 192.168.20.7 aa:bb:ce:dd:ff:03 192.168.10.8 aa:bb:cc:dd:ff:04 192.168.20.9 MAC MAC MAC aa:bb:cc:dd:ff:01 MAC Switch 1 MAC Table a) When a packet from PC1 to PC4 traverses the trunk link from Switch 1 to Router 1, fill in the following information as seen in the packet headers Source Destination Port aa:bb:cc:dd:ee:99 f0/1 aa:bb:cc:dd:ff:01 10/10 (2 marks) b) Nominate one advantage and one disadvantage of a layered network protocol architecture?
Expert Answer:
Answer rating: 100% (QA)
This is the answer MAC IP Source Destination aabbccddff01 aabbccddff99 192... View the full answer

Related Book For 

Computer Networking A Top-Down Approach
ISBN: 978-0133594140
7th edition
Authors: James Kurose, Keith Ross
Posted Date:
Students also viewed these computer network questions
-
Access Control Lists are just what they sound like and yet they're so powerful and specialized that they're often misunderstood. In your initial post, talk about what you think they are now. Put the...
-
IFRS and U.S. GAAP are relatively similar with respect to current liabilities and contingencies. Relatively minor differences relate to when financing must be in place for a liability expected to be...
-
Dickinson Company has $12,080,000 million in assets. Currently half of these assets are financed with long-term debt at 10.4 percent and half with common stock having a par value of $8. Ms. Park,...
-
Three friends are choosing a restaurant for dinner. Here are their preferences: a. If the three friends use a Borda count to make their decision, where do they go to eat? b. On their way to their...
-
Describe the three ways a mutual fund can generate returns for investors.
-
Which five statements are least appropriate? Practical considerations when conducting the presentation are: a. Anticipate questions and ensure full answers are provided. Some auditors see questions...
-
What are the three steps of the planning phase of the strategic marketing process? Answer: The three steps of the planning phase of the strategic marketing process are: (1) Conducting a situation...
-
Super Clean, Inc. produces and sells stain remover. Information about the budget for the year 2012 is as follows: 1. The company expects to sell 50,000 bottles of stain remover in the first quarter,...
-
View Policies Show Attempt History Current Attempt in Progress Mike Greenberg opened Cheyenne Window Washing Inc. on July 1, 2022. During July, the following transactions were completed. July 1 1 3 5...
-
HealthFull Nurse-Run Clinic: Table 6.2 analyzes appointments that are lost (cannot be scheduled) because of limits to capacity. However, another problem at HealthFull Clinic is cancelled...
-
Power and politics in organizational behaviour
-
An important first step of exploratory data analysis is always to visualize the data. Construct a scatterplot of each time series (i.e., two different plots). If you need pointers on how to make a...
-
Cleanie Wombat Cleanie Wombat is a small Australian company that makes cleaning products. The chemical formulas used for its products were developed through R&D conducted by the company's small R&D...
-
As a manager at Yummy Melts, Martin is responsible for the firm's Just Right brand of ice cream. He recently approved a proposal to test market new ice cream flavors. He is also considering the...
-
Cogenesis Corporation is replacing their current steam plant with a 6-megawatt cogeneration plant that will produce both steam and electric power for their operations. What is the impact of a 5% and...
-
Suppose ABC firm is considering an investment that would extend the life of one of its facilities for 5 years. The project would require upfront costs of $9.97M plus $28.94M investment in equipment....
-
You have just been hired as a financial analyst for Lydex Company, a manufacturer of safety helmets. Your boss has asked you to perform a comprehensive analysis of the companys financial statements,...
-
The liquidliquid extractor in Figure 8.1 operates at 100F and a nominal pressure of 15 psia. For the feed and solvent flows shown, determine the number of equilibrium stages to extract 99.5% of the...
-
Compare and contrast the properties of a centralized and a distributed routing algorithm. Give an example of a routing protocol that takes a centralized and a decentralized approach.
-
Consider the example in Figure 8.28. Suppose Trudy is a woman-in-the middle. Who can insert data-grams into the stream of data-gram going from Rl and R2. As part of a reply attack, Trudy sends a...
-
List several popular messaging apps. Do they use the same protocols as SMS?
-
E10.6. Applying Cash Flow Relations (Easy) A firm reported free cash flow of $430 million and operating income of $390 million. a. By how much did its net operating assets change during the period?...
-
E10.7. Applying Cash Flow Relations (Medium) An analyst prepared reformulated balance sheets for the years 2009 and 2008 as follows. (in millions of dollars): Operating assets 2009 $640 Financial...
-
E10.3. Analyzing Cash Flows (Medium) Consider the following comparative balance sheets for the Liquidity Company: Operating cash December 31 2008 2007 $ 435,000 $ 50,000 40,000 -0- 100,000 400,000...

Study smarter with the SolutionInn App


