Question: Consider the following protocol: 1. A KDC: 2. KDC A: 3. AB IDA | IDB || N1 E(Ka, [K: || IDE | M || ECK,
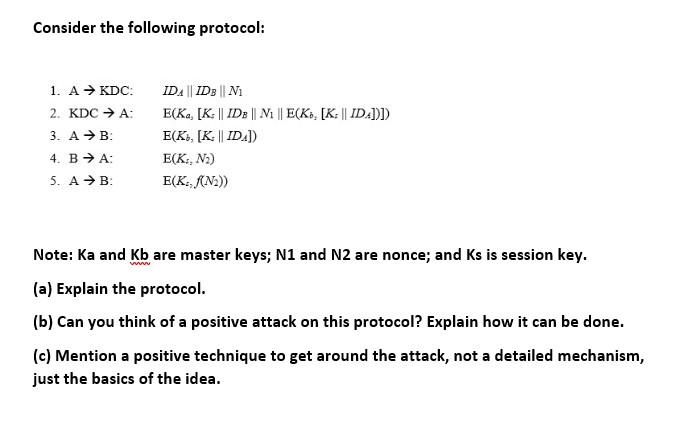
Consider the following protocol: 1. A KDC: 2. KDC A: 3. AB IDA | IDB || N1 E(Ka, [K: || IDE | M || ECK, [K: || ID.]))) E(K, [K: || ID)) E(K, N) E(K:, /(N2)) 4. BA: 5. AB Note: Ka and Kb are master keys; N1 and N2 are nonce; and Ks is session key. (a) Explain the protocol. (b) Can you think of a positive attack on this protocol? Explain how it can be done. (c) Mention a positive technique to get around the attack, not a detailed mechanism, just the basics of the idea
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


