Question: Consider the following protocol: Step 1: A + B : {NA, A}pk(B) Step 2: B + A: {{NA}pk(A); {NB}pk(A) }inv(pk(1)) Step 3: A + B
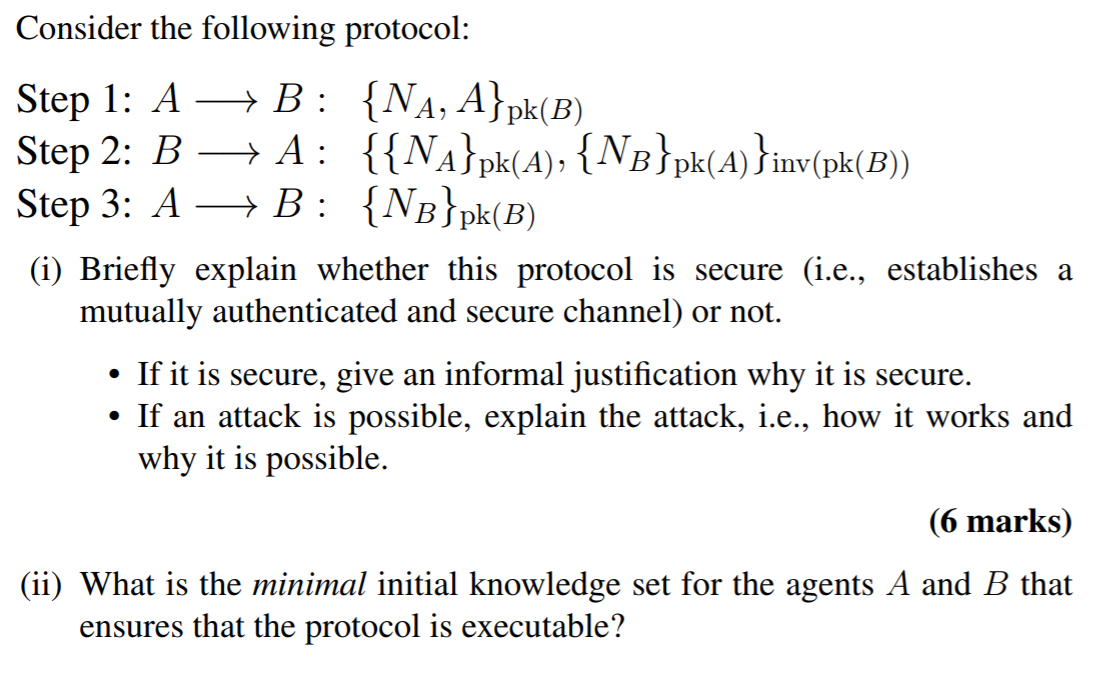
Consider the following protocol: Step 1: A + B : {NA, A}pk(B) Step 2: B + A: {{NA}pk(A); {NB}pk(A) }inv(pk(1)) Step 3: A + B : {NB}pk(B) (i) Briefly explain whether this protocol is secure (i.e., establishes a mutually authenticated and secure channel) or not. If it is secure, give an informal justification why it is secure. If an attack is possible, explain the attack, i.e., how it works and why it is possible. . (6 marks) (ii) What is the minimal initial knowledge set for the agents A and B that ensures that the protocol is executable
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


