Question: Constructing a multi-block MAC from a secure single-block MAC Suppose you are given a secure, single-block Message Authentication Code (MAC) scheme MACSB that can securely
Constructing a multi-block MAC from a secure single-block MAC
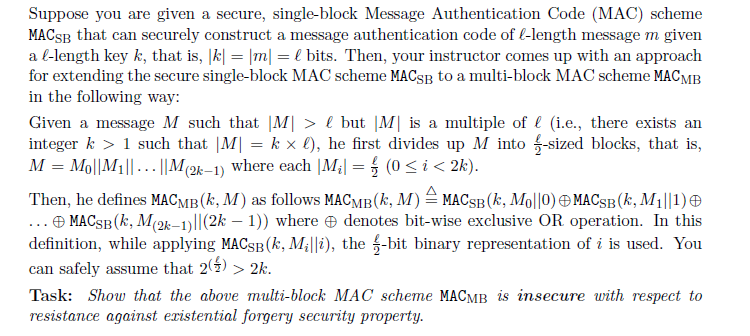
Suppose you are given a secure, single-block Message Authentication Code (MAC) scheme MACSB that can securely construct a message authentication code of l-length message m given a l-length key k, that is, k = m = l bits. Then, your instructor comes up with an approach for extending the secure single-block MAC scheme MACSB to a multi-block MAC scheme MACMB in the following way: Given a message M such that M > l but M is a multiple of l (i.e., there exists an integer k > 1 such that M| = kx), he first divides up M into --sized blocks, that is, M = Mo||M1|| ... ||M2k-1) where each |M| = 0 2k. Task: Show that the above multi-block MAC scheme MACMB is insecure with respect to resistance against existential forgery security property. Suppose you are given a secure, single-block Message Authentication Code (MAC) scheme MACSB that can securely construct a message authentication code of l-length message m given a l-length key k, that is, k = m = l bits. Then, your instructor comes up with an approach for extending the secure single-block MAC scheme MACSB to a multi-block MAC scheme MACMB in the following way: Given a message M such that M > l but M is a multiple of l (i.e., there exists an integer k > 1 such that M| = kx), he first divides up M into --sized blocks, that is, M = Mo||M1|| ... ||M2k-1) where each |M| = 0 2k. Task: Show that the above multi-block MAC scheme MACMB is insecure with respect to resistance against existential forgery security property
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


