Question: CoursHeroTranscribedText Select the appropriate port number, process name, and Protocol. Port # Process Name Protocol used Used for: 25 x FTP TCP File transfer-control 22
CoursHeroTranscribedText
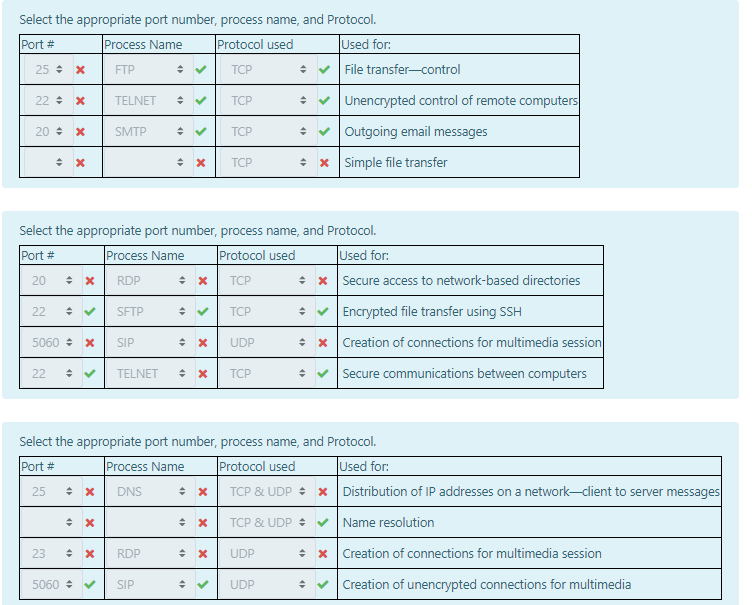
Select the appropriate port number, process name, and Protocol. Port # Process Name Protocol used Used for: 25 x FTP TCP File transfer-control 22 = 20- x x " TELNET TCP Unencrypted control of remote computers SMTP TCP Outgoing email messages x x = TCP xSimple file transfer Port # Select the appropriate port number, process name, and Protocol. Process Name Used for: Protocol used 20 = x RDP TCP Secure access to network-based directories 22 SFTP TCP Encrypted file transfer using SSH 5060 + SIP = UDP = Creation of connections for multimedia session 22 TELNET TCP Secure communications between computers Select the appropriate port number, process name, and Protocol. Process Name Used for: xDistribution of IP addresses on a network-client to server messages TCP & UDP Name resolution Port # Protocol used 25 DNS TCP & UDP = x 23 = x RDP = x UDP UDP 5060 SIP Creation of connections for multimedia session Creation of unencrypted connections for multimedia
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


