Question: Create a program that generates a secure password. Prompt the user for the minimum length, the number of special characters, and the number of
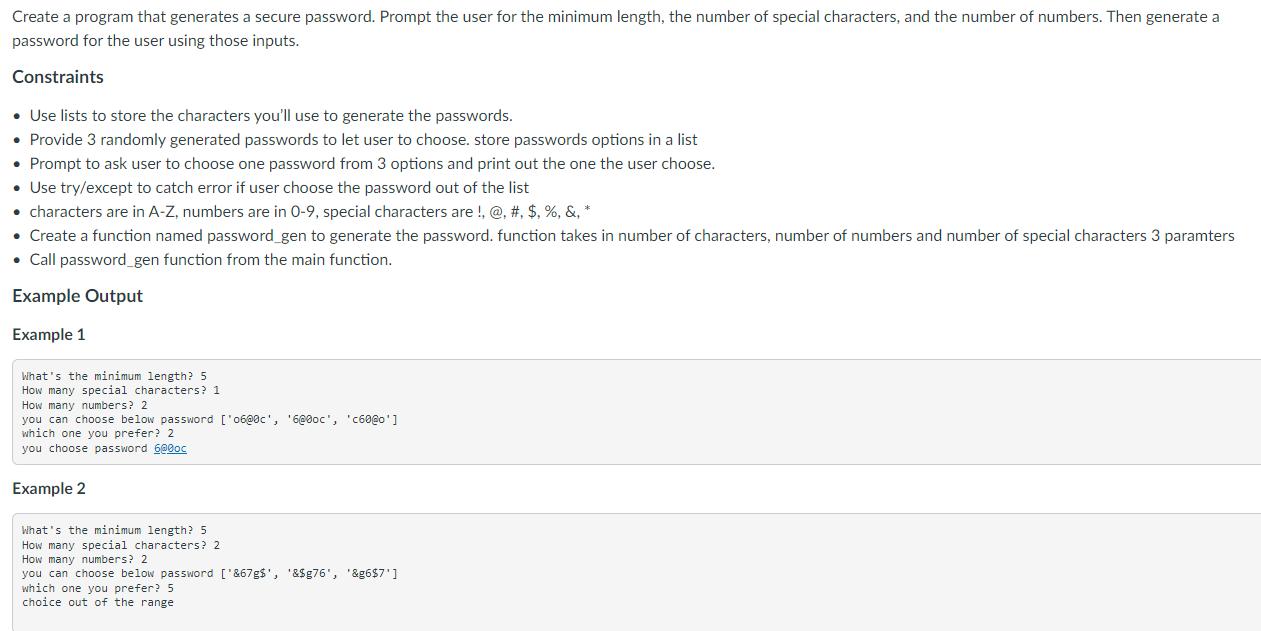
Create a program that generates a secure password. Prompt the user for the minimum length, the number of special characters, and the number of numbers. Then generate a password for the user using those inputs. Constraints Use lists to store the characters you'll use to generate the passwords. Provide 3 randomly generated passwords to let user to choose. store passwords options in a list Prompt to ask user to choose one password from 3 options and print out the one the user choose. Use try/except to catch error if user choose the password out of the list characters are in A-Z, numbers are in 0-9, special characters are !, @, #, $, %, &, * Create a function named password_gen to generate the password. function takes in number of characters, number of numbers and number of special characters 3 paramters Call password_gen function from the main function. Example Output Example 1 What's the minimum length? 5 How many special characters? 1 How many numbers? 2 you can choose below password ['06@0c', '6@0oc', 'c60@o'] which one you prefer? 2 you choose password 6@0oc Example 2 What's the minimum length? 5 How many special characters? 2. How many numbers? 2. you can choose below password ['&67g$', '&$g76', '&g6$7'] which one you prefer? 5. choice out of the range
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


