Question: Create a program that will ask the user some personal information. the program should be able to display a paragraph using the information provided
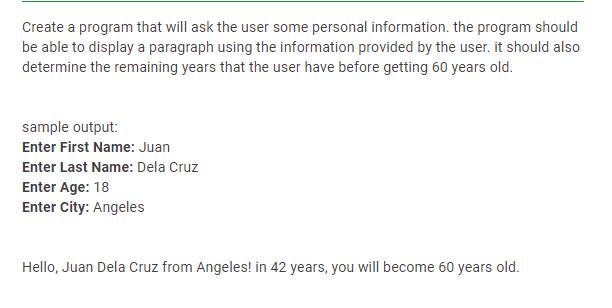
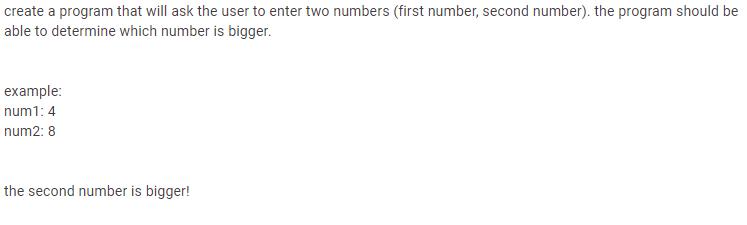
Create a program that will ask the user some personal information. the program should be able to display a paragraph using the information provided by the user. it should also determine the remaining years that the user have before getting 60 years old. sample output: Enter First Name: Juan Enter Last Name: Dela Cruz Enter Age: 18 Enter City: Angeles Hello, Juan Dela Cruz from Angeles! in 42 years, you will become 60 years old. create a program that will ask the user to enter two numbers (first number, second number). the program should be able to determine which number is bigger. example: num1: 4 num2: 8 the second number is bigger!
Step by Step Solution
3.43 Rating (159 Votes )
There are 3 Steps involved in it
Python Personal Information Program firstname inputEn... View full answer

Get step-by-step solutions from verified subject matter experts


