Question: Cyber Security Forensics ttempt.php?attempt=8039728cmid=851555 A key logger is an example of Select one: O a. spyware b. rootkit O C. ransomware O d. trojan O
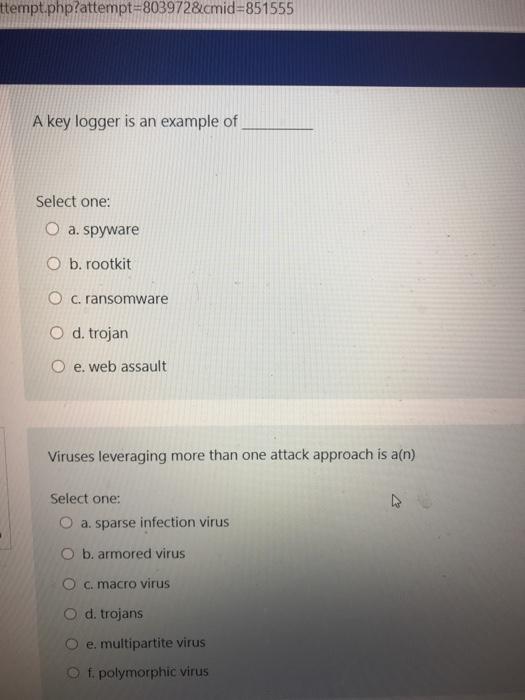
ttempt.php?attempt=8039728cmid=851555 A key logger is an example of Select one: O a. spyware b. rootkit O C. ransomware O d. trojan O e. web assault Viruses leveraging more than one attack approach is a(n) Select one: O a. sparse infection virus O b. armored virus O c. macro virus O d. trojans e. multipartite virus f. polymorphic virus
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


