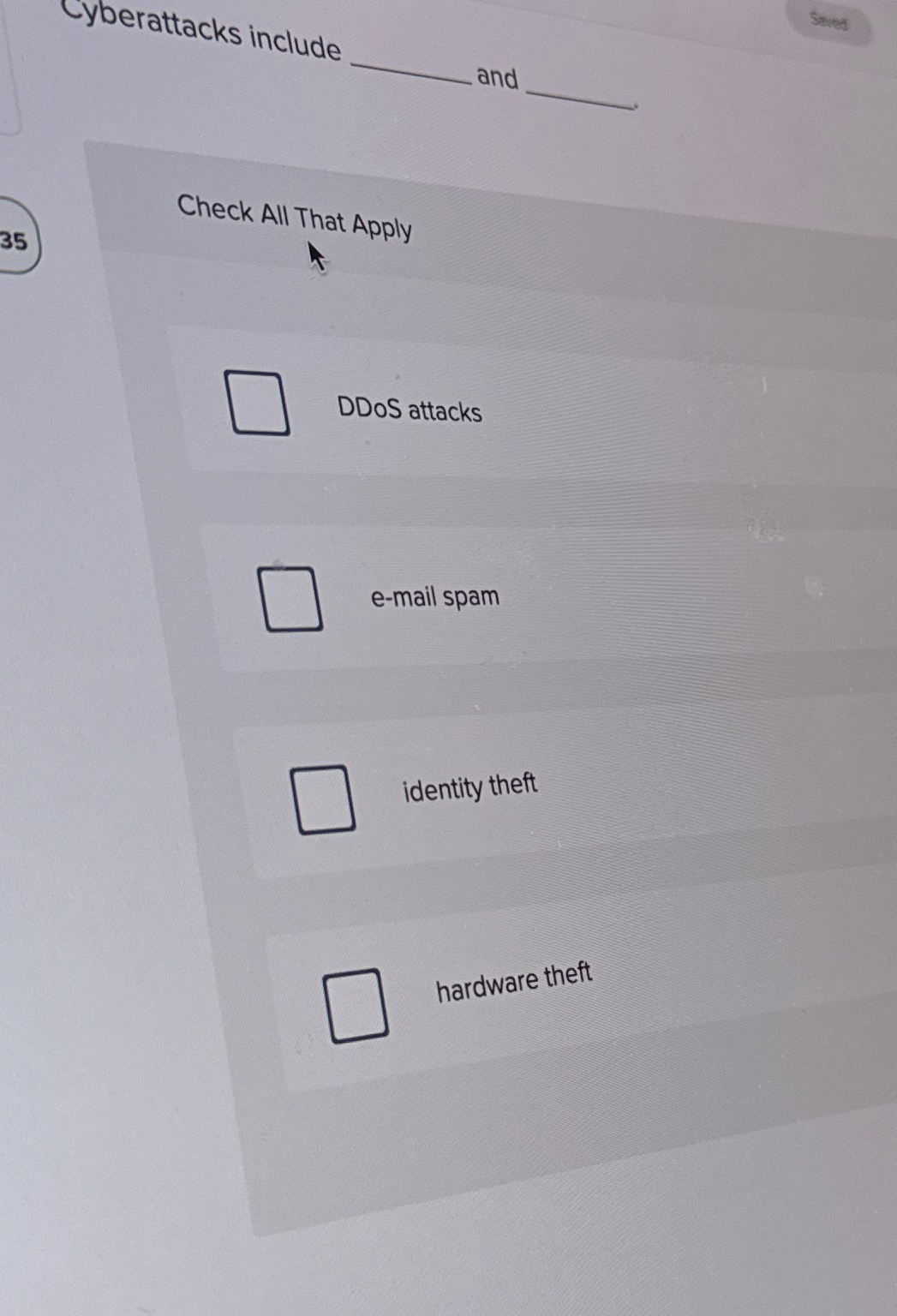
Question: cyberattacks include and Check All That Apply DDoS attacks e - mail spam identity theft hardware theft
Step by Step Solution
There are 3 Steps involved in it
For the question Cyberattacks include and from the gi... View full answer

Get step-by-step solutions from verified subject matter experts


