Question: D ocument (Word or PDF) that contains A domain model Use Case Robustness Diagram Descriptions of Test Cases The game is played using: ***************... CONNEC
 Document (Word or PDF) that contains
Document (Word or PDF) that contains
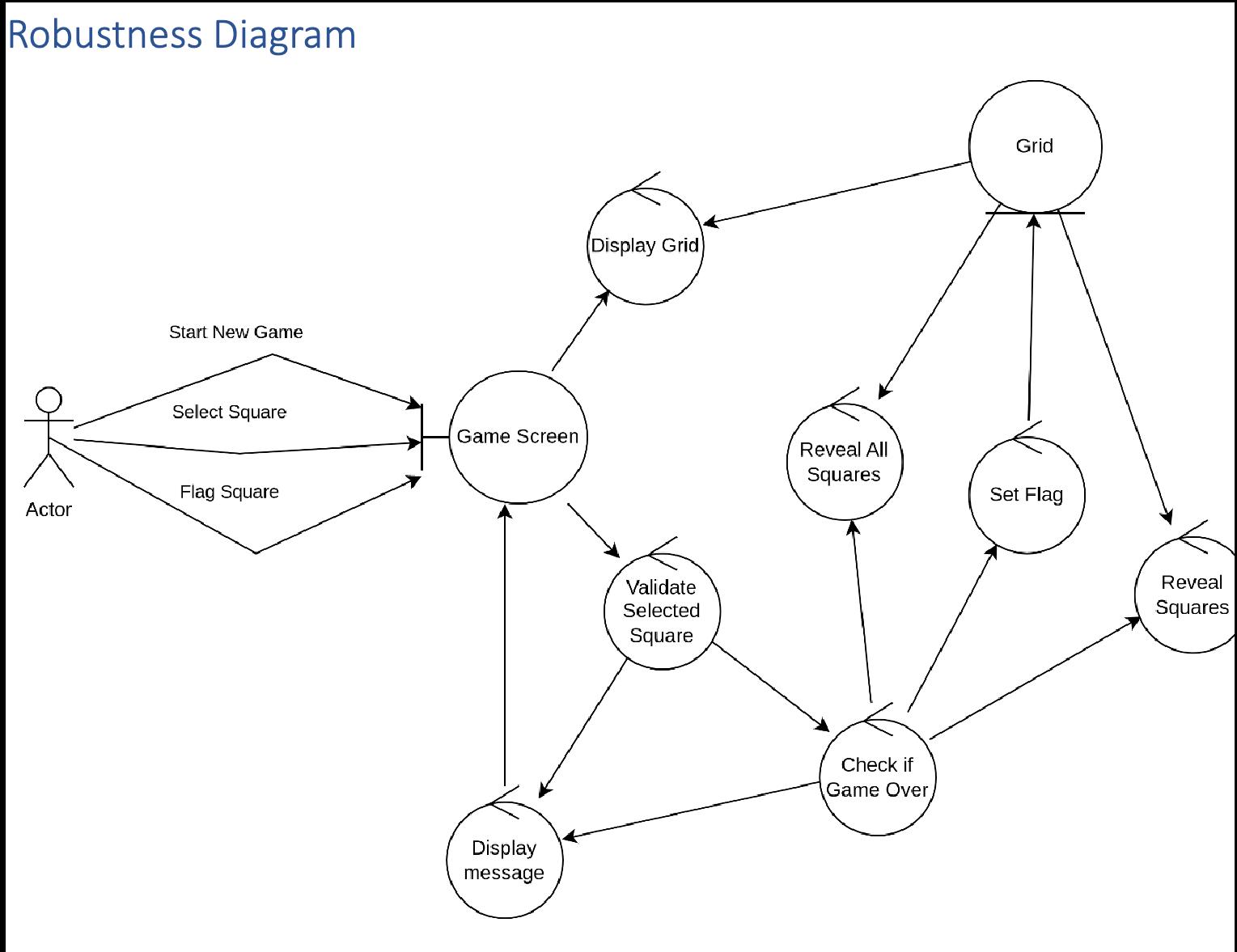
- A domain model
- Use Case
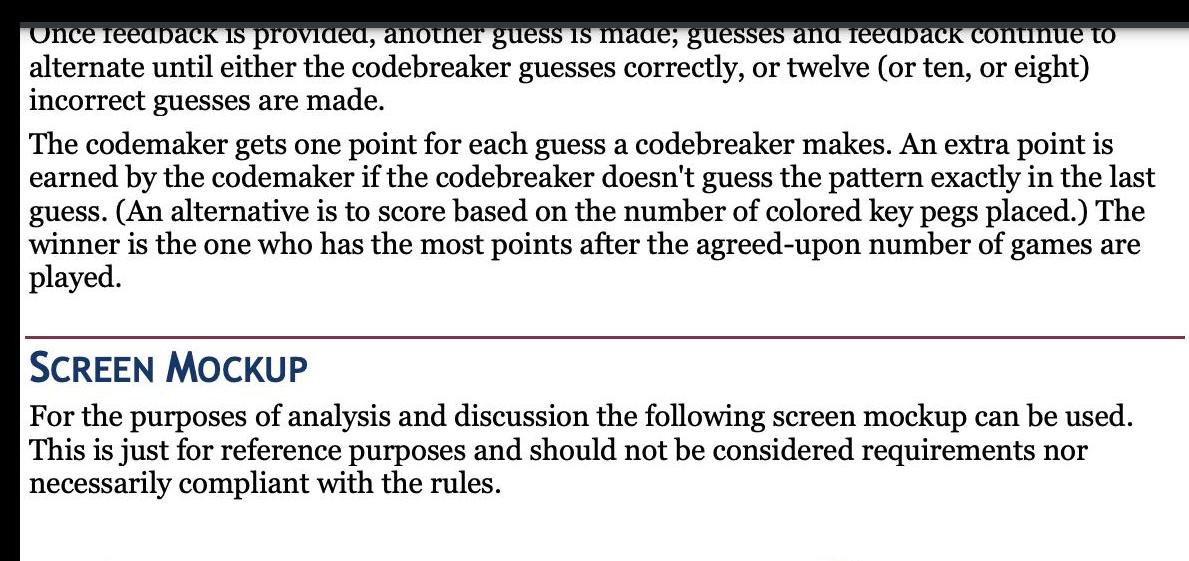
- Robustness Diagram
- Descriptions of Test Cases
![Use Case User 1. Starts new game 3. Selects square on grid [ALT-1] ALT-1: Flag Square 3.a Sets flag on](https://dsd5zvtm8ll6.cloudfront.net/si.experts.images/questions/2023/08/64eda10573edd_1693294851289.jpg)
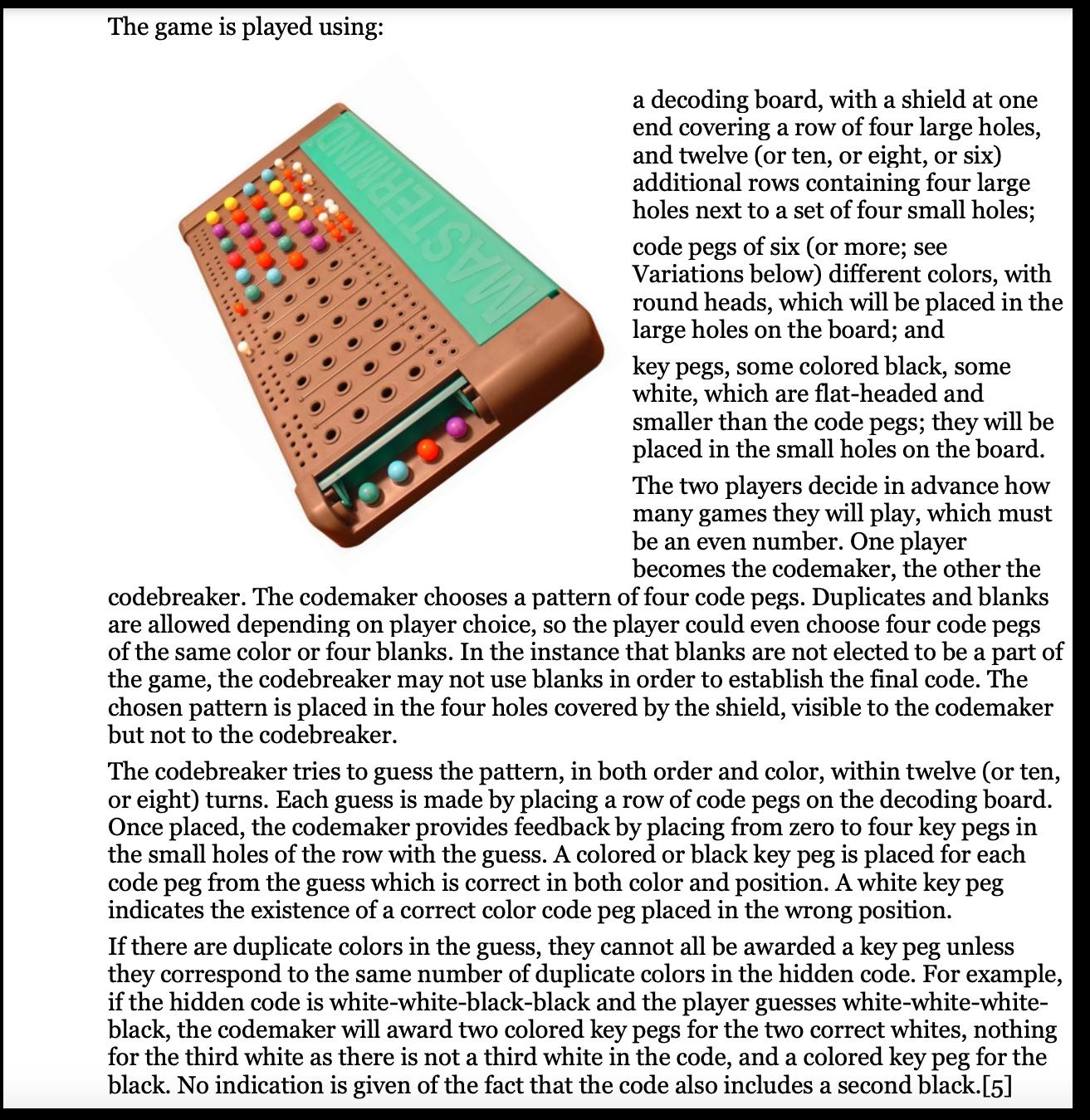
The game is played using: ***************... CONNEC a decoding board, with a shield at one end covering a row of four large holes, and twelve (or ten, or eight, or six) additional rows containing four large holes next to a set of four small holes; code pegs of six (or more; see Variations below) different colors, with round heads, which will be placed in the large holes on the board; and key pegs, some colored black, some white, which are flat-headed and smaller than the code pegs; they will be placed in the small holes on the board. The two players decide in advance how many games they will play, which must be an even number. One player becomes the codemaker, the other the codebreaker. The codemaker chooses a pattern of four code pegs. Duplicates and blanks are allowed depending on player choice, so the player could even choose four code pegs of the same color or four blanks. In the instance that blanks are not elected to be a part of the game, the codebreaker may not use blanks in order to establish the final code. The chosen pattern is placed in the four holes covered by the shield, visible to the codemaker but not to the codebreaker. The codebreaker tries to guess the pattern, in both order and color, within twelve (or ten, or eight) turns. Each guess is made by placing a row of code pegs on the decoding board. Once placed, the codemaker provides feedback by placing from zero to four key pegs in the small holes of the row with the guess. A colored or black key peg is placed for each code peg from the guess which is correct in both color and position. A white key peg indicates the existence of a correct color code peg placed in the wrong position. If there are duplicate colors in the guess, they cannot all be awarded a key peg unless they correspond to the same number of duplicate colors in the hidden code. For example, if the hidden code is white-white-black-black and the player guesses white-white-white- black, the codemaker will award two colored key pegs for the two correct whites, nothing for the third white as there is not a third white in the code, and a colored key peg for the black. No indication is given of the fact that the code also includes a second black.[5]
Step by Step Solution
3.47 Rating (160 Votes )
There are 3 Steps involved in it
Introduction This discussion explores the screen mockup of a game model providing an analysis of its key features and gameplay elements through four provided images The focus is on identifying the def... View full answer

Get step-by-step solutions from verified subject matter experts


