Question: Diffie-Hellman exchange protocol. Alice and Bob agrees to use the public prime p = 1051 and the public primitive root a = 7. Alice
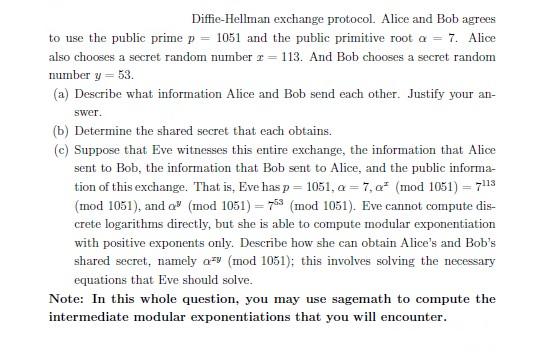
Diffie-Hellman exchange protocol. Alice and Bob agrees to use the public prime p = 1051 and the public primitive root a = 7. Alice also chooses a secret random number r= 113. And Bob chooses a secret random number y = 53. (a) Describe what information Alice and Bob send each other. Justify your an- swer. (b) Determine the shared secret that each obtains. (c) Suppose that Eve witnesses this entire exchange, the information that Alice sent to Bob, the information that Bob sent to Alice, and the public informa- tion of this exchange. That is, Eve has p = 1051, a=7,a (mod 1051) = 7113 (mod 1051), and a (mod 1051) = 753 (mod 1051). Eve cannot compute dis- crete logarithms directly, but she is able to compute modular exponentiation with positive exponents only. Describe how she can obtain Alice's and Bob's shared secret, namely a (mod 1051); this involves solving the necessary equations that Eve should solve. Note: In this whole question, you may use sagemath to compute the intermediate modular exponentiations that you will encounter.
Step by Step Solution
3.55 Rating (152 Votes )
There are 3 Steps involved in it
ANSWER This exercise is about y 3 Describe what information Alice bob send each other 8017 2 Given i... View full answer

Get step-by-step solutions from verified subject matter experts


