Question: Discuss the cloud security threat shown in the below figure. Cloud Service Consumer A (attacker) overload Cloud Service Consumer B
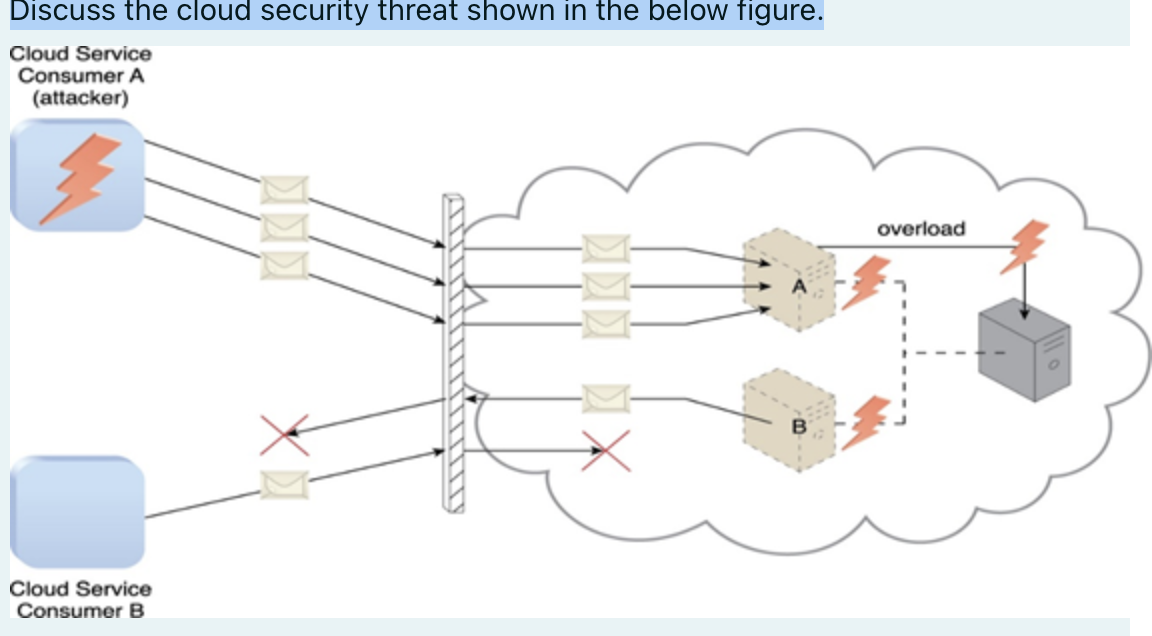
Discuss the cloud security threat shown in the below figure. Cloud Service Consumer A (attacker) overload Cloud Service Consumer B
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


