Dissatisfied with Kerberos (he's difficult to please), Prof. Pedantic proposes a simpler protocol called Chomp ChompTM...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
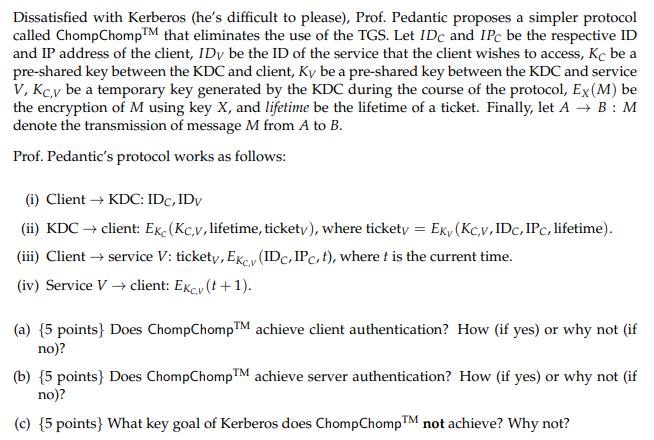
Dissatisfied with Kerberos (he's difficult to please), Prof. Pedantic proposes a simpler protocol called Chomp ChompTM that eliminates the use of the TGS. Let IDc and IPC be the respective ID and IP address of the client, IDy be the ID of the service that the client wishes to access, Kc be a pre-shared key between the KDC and client, Ky be a pre-shared key between the KDC and service V, Kc,y be a temporary key generated by the KDC during the course of the protocol, Ex (M) be the encryption of M using key X, and lifetime be the lifetime of a ticket. Finally, let A → B : M denote the transmission of message M from A to B. Prof. Pedantic's protocol works as follows: (i) Client → KDC: IDC, IDv (ii) KDC → client: Ekc (Kcv, lifetime, tickety), where tickety = Eky (Kc,v, IDc, IPC, lifetime). (iii) Client → service V: tickety, EKcy (IDC, IPC, t), where t is the current time. (iv) Service V→ client: Excy (t+1). (a) {5 points} Does ChompChompTM achieve client authentication? How (if yes) or why not (if no)? (b) {5 points} Does Chomp ChompTM achieve server authentication? How (if yes) or why not (if no)? (c) {5 points} What key goal of Kerberos does Chomp ChompTM not achieve? Why not? Dissatisfied with Kerberos (he's difficult to please), Prof. Pedantic proposes a simpler protocol called Chomp ChompTM that eliminates the use of the TGS. Let IDc and IPC be the respective ID and IP address of the client, IDy be the ID of the service that the client wishes to access, Kc be a pre-shared key between the KDC and client, Ky be a pre-shared key between the KDC and service V, Kc,y be a temporary key generated by the KDC during the course of the protocol, Ex (M) be the encryption of M using key X, and lifetime be the lifetime of a ticket. Finally, let A → B : M denote the transmission of message M from A to B. Prof. Pedantic's protocol works as follows: (i) Client → KDC: IDC, IDv (ii) KDC → client: Ekc (Kcv, lifetime, tickety), where tickety = Eky (Kc,v, IDc, IPC, lifetime). (iii) Client → service V: tickety, EKcy (IDC, IPC, t), where t is the current time. (iv) Service V→ client: Excy (t+1). (a) {5 points} Does ChompChompTM achieve client authentication? How (if yes) or why not (if no)? (b) {5 points} Does Chomp ChompTM achieve server authentication? How (if yes) or why not (if no)? (c) {5 points} What key goal of Kerberos does Chomp ChompTM not achieve? Why not?
Expert Answer:
Answer rating: 100% (QA)
The image provided appears to contain a theoretical discussion of an authentication protocol named ChompChomp which is proposed as an alternative to the Kerberos protocol The question asks to evaluate ... View the full answer

Related Book For 

Financial Reporting and Analysis
ISBN: 978-1259722653
7th edition
Authors: Lawrence Revsine, Daniel Collins, Bruce Johnson, Fred Mittelstaedt, Leonard Soffer
Posted Date:
Students also viewed these programming questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Nikes approach to managing supplier responsibility has greatly evolved since the 1990s when the media uncovered claims of child labor, underpaid workers, and poor working conditions in several Asian...
-
Research an organization that has EITHER done a great job at identifying how they are socially responsible, or that has gotten into "hot water" for not being ethical in their advertising. If you...
-
What is the acceleration of a car that maintains a constant velocity of 100 km/h for 10 s? (Why do some of your classmates who correctly answer the preceding question get this question wrong?)
-
ROGER: I think modern society is becoming more and more violent every day. Just look at the increase in murder, rape, and robbery. Violence is clearly an evil that must be eradicated. MARK: You might...
-
State the advantages of chain drive over belt drive. Draw neat sketches of simple and compound gear train.
-
The information systems (IS) department at Jacobsons Inc. consists of eight employees, including the IS Manager, Melinda Cullen. Melinda is responsible for the day-to-day oversight of the IS function...
-
Disney needs to close Magic Kingdom to remodel and update the castle. Disney's advisors presented two renovation alternatives: (1) a quick facelift or (2) a complete rebuild. The quick facelift would...
-
1. Discuss the main issues faced by Yalla Momos. 2. Evaluate the current financial performance of Yalla Momos and compare his performance to the industry ratios. 3. Elaborate on the relevant factors...
-
Bob Loblaw and Wayne Jarvis get together to form a new corporation. They each own 50% of the stock. Neither is employed by the corporation. In the first year of operation, the corporation generates...
-
Roman Company was established a few years ago. The company operates all over the beautiful Pacific Northwest. Roman Company has just completed its current accounting period for the year. Roman...
-
6. Write the equation of a line that has a slope of and a y-intercept of -2. (3 pts)
-
Hand Written Pro Forma Using the Simple Stacked Cash Flow. Construct a 3-year projection. Assume the purchase price was determined at a 9.0% CAP Rate (Rate of Return with No Debt) Givens: NOI -...
-
A customer intends to leverage serverless lambda functions on AWS to build a REST service. What are the typical parameters that need to setup in Lambda to ensure everything runs well?
-
what ways can environmental scanning techniques and trend analysis frameworks be leveraged to anticipate emergent challenges and opportunities, informing the strategic direction and priorities...
-
Mick Stone disposed of the following assets during tax year 2017-18: (1) On 19 May 2017, Mick sold a freehold warehouse for 522,000. The warehouse was purchased on 6 August 2005 for 258,000, and was...
-
SCHEDULE OF COST OF GOODS MANUFACTURED The following information is supplied for Sanchez Welding and Manufacturing Company. Prepare a schedule of cost of goods manufactured for the year ended...
-
Glick Corporation offers a 10% volume discount to customers who purchase more than 10,000 units of its yoga mats in a calendar year. The volume discount applies to all units purchased in the year,...
-
Margaret Magee has served both as an outside director to Maxcor Manufacturing since 2010 and as a member of the company's compensation committee since 2014. Margaret has been reviewing Maxcor's 2017...
-
Royal Dutch Shell had pretax income of $2,047 million, $28,314 million and $33,592 million in 2015, 2014, and 2013, respectively. Presented below are excerpts from the 2015 annual report of Royal...
-
The two transistors in Figure P32.26 are connected to each other by wires and also connected to input wires at terminals \(\mathrm{A}\) and \(\mathrm{B}\). The output of this combination depends on...
-
Is the light bulb in Figure P32.27 lit? Data from Figure P32.27 (e)
-
Which circuit in Figure P32.25 produces the greatest current in the emitter? Data from Figure P32.25 A B n-type p-type n-type n-type p-type n-type C n-type p-type n-type HHHHH

Study smarter with the SolutionInn App