Question: Dnce upon a time, the following cyptographic hash function was proposed as a way of ensuring data integrity: 1. Given some plaintext spell (message), m=m1m2mn,
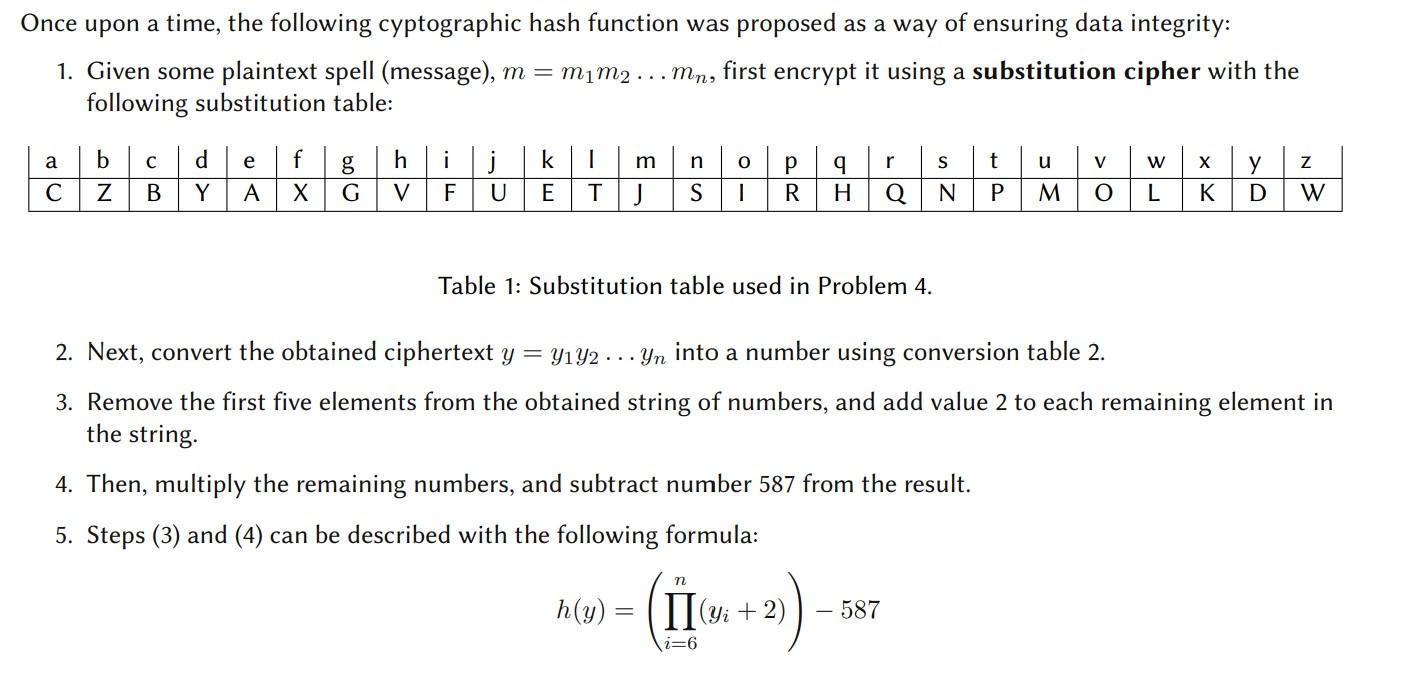
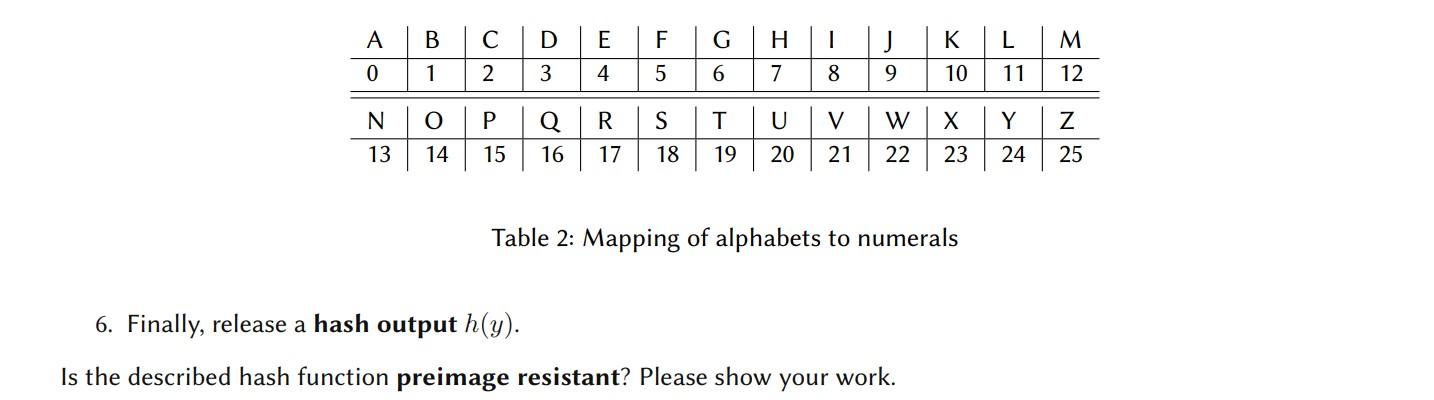
Dnce upon a time, the following cyptographic hash function was proposed as a way of ensuring data integrity: 1. Given some plaintext spell (message), m=m1m2mn, first encrypt it using a substitution cipher with the following substitution table: Ca Table 1: Substitution table used in Problem 4. 2. Next, convert the obtained ciphertext y=y1y2yn into a number using conversion table 2. 3. Remove the first five elements from the obtained string of numbers, and add value 2 to each remaining element in the string. 4. Then, multiply the remaining numbers, and subtract number 587 from the result. 5. Steps (3) and (4) can be described with the following formula: h(y)=(i=6n(yi+2))587 Table 2: Mapping of alphabets to numerals 6. Finally, release a hash output h(y). Is the described hash function preimage resistant? Please show your work
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


