Question: Do not Copy Wikipedia. Please give step by step solution. Suppose Bob's public key is e, secret key is d, and RSA modulus is n.
Do not Copy Wikipedia. Please give step by step solution.
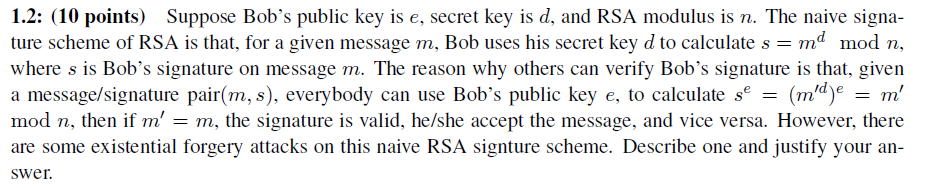
Suppose Bob's public key is e, secret key is d, and RSA modulus is n. The naive signature scheme of RSA is that, for a given message m, Bob uses his secret key d to calculate s = m^d mod n, where s is Bob's signature on message m. The reason why others can verify Bob's signature is that, given a message/signature pair(m, s), everybody can use Bob's public key e, to calculate s^e = (m'^d)^e = m' mod n, then if m! = m, the signature is valid, he/she accept the message, and vice versa. However, there are some existential forgery attacks on this naive RSA signature scheme. Describe one and justify your
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


