Question: Domain primitives can only exist if they are Secure In Code Valid Defined Question 8 (1 point) E Listen According to chapter 5. One
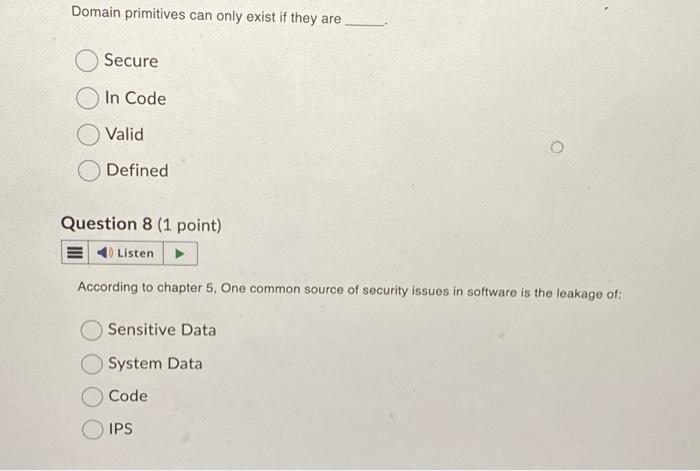
Domain primitives can only exist if they are Secure In Code Valid Defined Question 8 (1 point) E Listen According to chapter 5. One common source of security issues in software is the leakage of: Sensitive Data System Data Code IPS
Step by Step Solution
★★★★★
3.41 Rating (170 Votes )
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock

Domain primitives can only exist if they are Defined In the context of software development and systems design domain primitives are fundamental building blocks or elements that represent concepts or ... View full answer

Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


