Question: Effective Security Controls for End-users 1. Describe typical organization IT environment 2. Describe two major vulnerabilities regarding end-users 3. Describe effective controls to mitigate
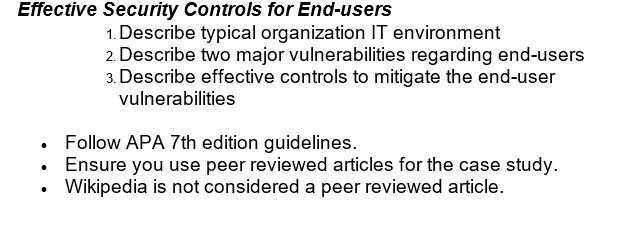
Effective Security Controls for End-users 1. Describe typical organization IT environment 2. Describe two major vulnerabilities regarding end-users 3. Describe effective controls to mitigate the end-user vulnerabilities . Follow APA 7th edition guidelines. Ensure you use peer reviewed articles for the case study. Wikipedia is not considered a peer reviewed article.
Step by Step Solution
3.56 Rating (167 Votes )
There are 3 Steps involved in it
To conduct daytoday functions and improve productivity modern businesses depend on technology The efficient use of technology influences workplace efficiency lowers operational costs while improving c... View full answer

Get step-by-step solutions from verified subject matter experts
Document Format (1 attachment)
6368a530eab6b_106401.docx
120 KBs Word File


