Question: Encryption techniques where both users share a key are known as encryption. Symmetric Asymmetric Cipher Algorithm Question 4 9 5 pts Encryption techniques where both
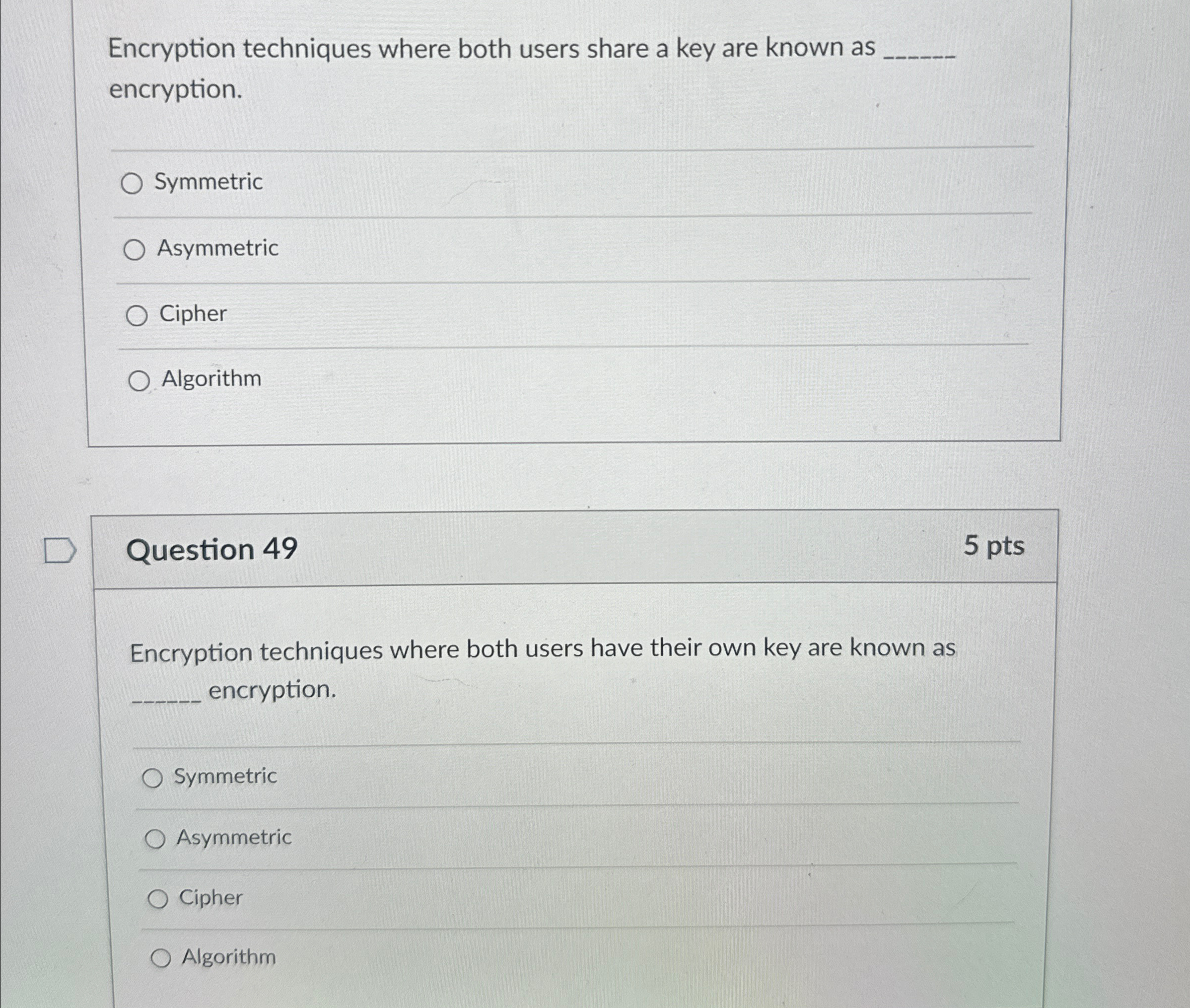
Encryption techniques where both users share a key are known as encryption.
Symmetric
Asymmetric
Cipher
Algorithm
Question
pts
Encryption techniques where both users have their own key are known as
encryption.
Symmetric
Asymmetric
Cipher
Algorithm
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


