Question: Explain ? m2 m3 m4 mg m6 IV E- E- E- E encrypt with secret key CO Consider the cipher block chaining (CBC) mode of
Explain ?
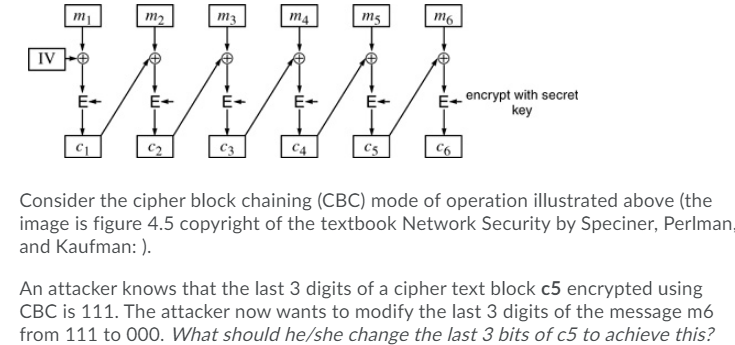
m2 m3 m4 mg m6 IV E- E- E- E encrypt with secret key CO Consider the cipher block chaining (CBC) mode of operation illustrated above (the image is figure 4.5 copyright of the textbook Network Security by Speciner, Perlman, and Kaufman:). An attacker knows that the last 3 digits of a cipher text block c5 encrypted using CBC is 111. The attacker now wants to modify the last 3 digits of the message m6 from 111 to 000. What should he/she change the last 3 bits of c5 to achieve this? m2 m3 m4 mg m6 IV E- E- E- E encrypt with secret key CO Consider the cipher block chaining (CBC) mode of operation illustrated above (the image is figure 4.5 copyright of the textbook Network Security by Speciner, Perlman, and Kaufman:). An attacker knows that the last 3 digits of a cipher text block c5 encrypted using CBC is 111. The attacker now wants to modify the last 3 digits of the message m6 from 111 to 000. What should he/she change the last 3 bits of c5 to achieve this
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


