Question: Fall 2017 8. The system of user identification and authentication that prevents unauthorized users from gaining o network resources is call Network server Firewall Network
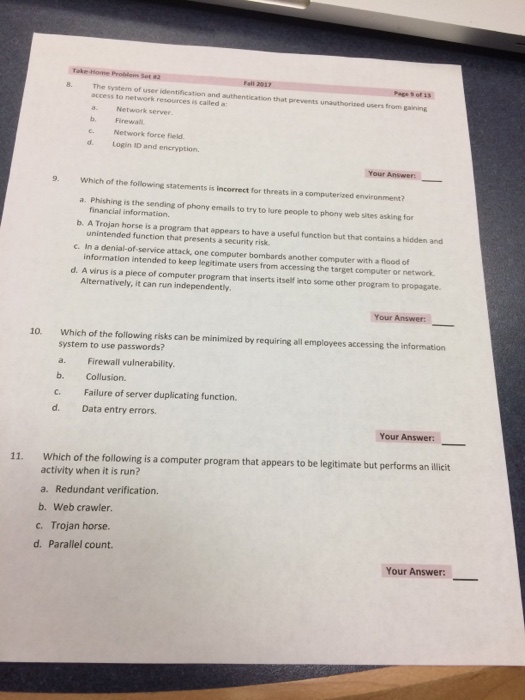
Fall 2017 8. The system of user identification and authentication that prevents unauthorized users from gaining o network resources is call Network server Firewall Network force Field ed a a. b. d. Login ID and encryption 9 Which of the following statements is incorrect for threats in a computerized environment? a. Phishing is the sending of phony emails to try to lure people to phony web sites asking for financial information. b. A Trojan horse is a program that appears to have a useful function but that contains a hidden and c. In a denial-of-service attack, one computer bombards another computer with a flood of d. A virus is a piece of computer program that inserts itself into some other program to propagate unintended function that presents a security risk information intended to keep legitimate users from accessing the target computer or network Alternatively, it can run independently 10. Which of the following risks can be minimized by requiring all employees accessing the information system to use passwords? a. Firewall vulnerability. b. Collusion c. Failure of server duplicating function d. Data entry errors Your Answer: 11. Which of the following is a computer program that appears to be legitimate but performs an illicit activity when it is run? a. Redundant verification. b. Web crawler c. Trojan horse d. Parallel count. Your
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


