Question: Field checks, access control, and change logs are three ways in which q , can be implemented following the insertion of incorrect data into a
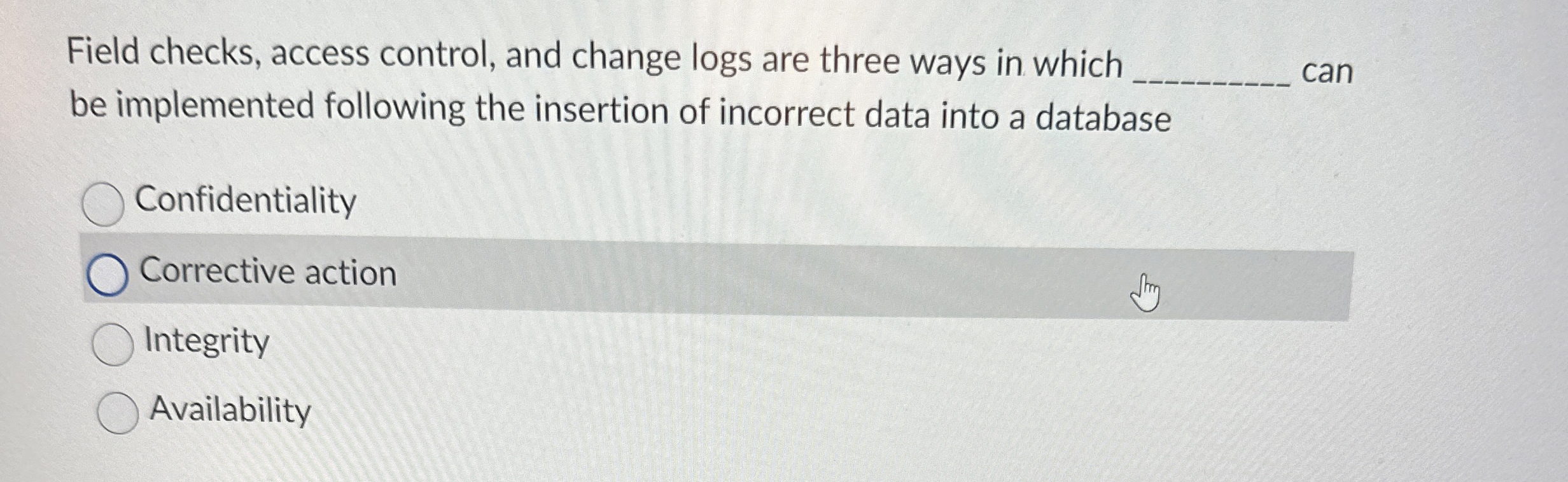
Field checks, access control, and change logs are three ways in which can be implemented following the insertion of incorrect data into a database
Confidentiality
Corrective action
Integrity
Availability
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


