Question: Figure Q2(b): Program code (i) State the attack of the above program code. [1 mark] (ii) Explain how the system can be exploited by this
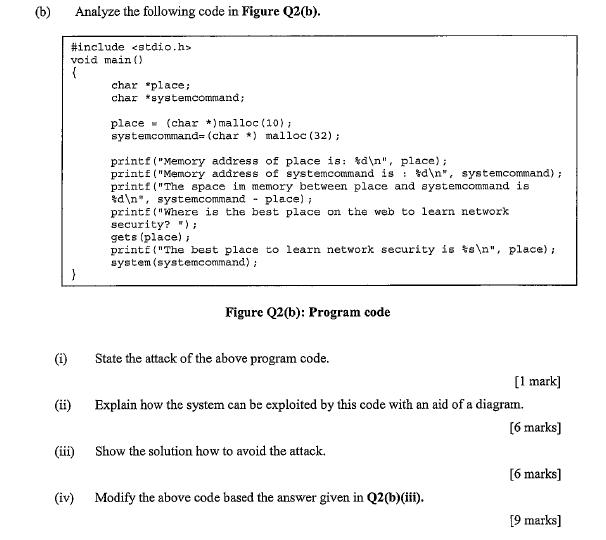
Figure Q2(b): Program code (i) State the attack of the above program code. [1 mark] (ii) Explain how the system can be exploited by this code with an aid of a diagram. [6 marks] (iii) Show the solution how to avoid the attack. [6 marks] (iv) Modify the above code based the answer given in Q2 (b)(iii). [9 marks]
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


