Question: Fill the table below: Department/Area CEO & Admin Sales & Marketing IT Support No. oft Type oft Threats Cyber Security (A) Assess Threats (B)
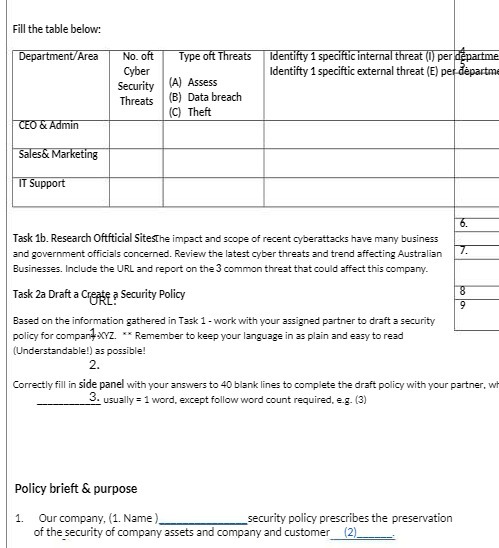
Fill the table below: Department/Area CEO & Admin Sales & Marketing IT Support No. oft Type oft Threats Cyber Security (A) Assess Threats (B) Data breach (C) Theft Identifty 1 speciftic internal threat (1) per departme Identifty 1 speciftic external threat (E) per departme 6. Task 1b. Research Oftfticial Sitesthe impact and scope of recent cyberattacks have many business and government officials concerned. Review the latest cyber threats and trend affecting Australian Businesses. Include the URL and report on the 3 common threat that could affect this company. Task 2a Draft a Create a Security Policy URL: Based on the information gathered in Task 1 - work with your assigned partner to draft a security policy for companXYZ. ** Remember to keep your language in as plain and easy to read (Understandable!) as possible! 2. 7. 8 9 Correctly fill in side panel with your answers to 40 blank lines to complete the draft policy with your partner, wh 3. usually = 1 word, except follow word count required, e.g. (3) Policy brieft & purpose 1. Our company, (1. Name) security policy prescribes the preservation of the security of company assets and company and customer (2)
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


