For all (and only) dynamic programming problems in this class, we would like you to follow...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
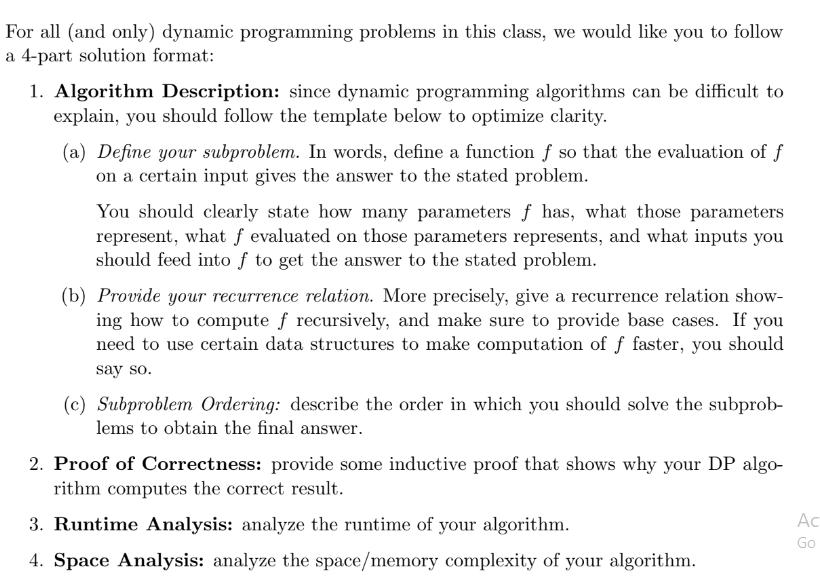
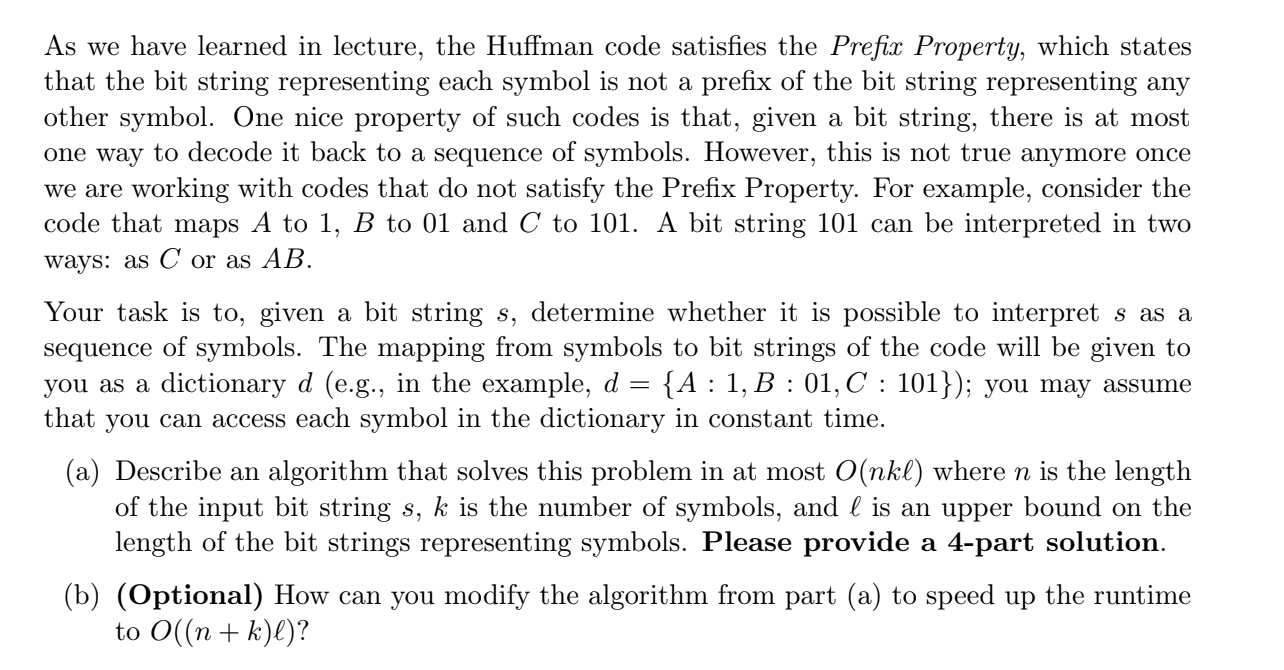
For all (and only) dynamic programming problems in this class, we would like you to follow a 4-part solution format: 1. Algorithm Description: since dynamic programming algorithms can be difficult to explain, you should follow the template below to optimize clarity. (a) Define your subproblem. In words, define a function f so that the evaluation of f on a certain input gives the answer to the stated problem. You should clearly state how many parameters f has, what those parameters represent, what f evaluated on those parameters represents, and what inputs you should feed into f to get the answer to the stated problem. (b) Provide your recurrence relation. More precisely, give a recurrence relation show- ing how to compute f recursively, and make sure to provide base cases. If you need to use certain data structures to make computation of f faster, you should say so. (c) Subproblem Ordering: describe the order in which you should solve the subprob- lems to obtain the final answer. 2. Proof of Correctness: provide some inductive proof that shows why your DP algo- rithm computes the correct result. 3. Runtime Analysis: analyze the runtime of your algorithm. 4. Space Analysis: analyze the space/memory complexity of your algorithm. Ac Go As we have learned in lecture, the Huffman code satisfies the Prefix Property, which states that the bit string representing each symbol is not a prefix of the bit string representing any other symbol. One nice property of such codes is that, given a bit string, there is at most one way to decode it back to a sequence of symbols. However, this is not true anymore once we are working with codes that do not satisfy the Prefix Property. For example, consider the code that maps A to 1, B to 01 and C to 101. A bit string 101 can be interpreted in two ways: as C or as AB. Your task is to, given a bit string s, determine whether it is possible to interpret s as a sequence of symbols. The mapping from symbols to bit strings of the code will be given to you as a dictionary d (e.g., in the example, d {A 1, B 01, C: 101}); you may assume = : that you can access each symbol in the dictionary in constant time. (a) Describe an algorithm that solves this problem in at most O(nkl) where n is the length of the input bit string s, k is the number of symbols, and l is an upper bound on the length of the bit strings representing symbols. Please provide a 4-part solution. (b) (Optional) How can you modify the algorithm from part (a) to speed up the runtime to O((n + k)l)? For all (and only) dynamic programming problems in this class, we would like you to follow a 4-part solution format: 1. Algorithm Description: since dynamic programming algorithms can be difficult to explain, you should follow the template below to optimize clarity. (a) Define your subproblem. In words, define a function f so that the evaluation of f on a certain input gives the answer to the stated problem. You should clearly state how many parameters f has, what those parameters represent, what f evaluated on those parameters represents, and what inputs you should feed into f to get the answer to the stated problem. (b) Provide your recurrence relation. More precisely, give a recurrence relation show- ing how to compute f recursively, and make sure to provide base cases. If you need to use certain data structures to make computation of f faster, you should say so. (c) Subproblem Ordering: describe the order in which you should solve the subprob- lems to obtain the final answer. 2. Proof of Correctness: provide some inductive proof that shows why your DP algo- rithm computes the correct result. 3. Runtime Analysis: analyze the runtime of your algorithm. 4. Space Analysis: analyze the space/memory complexity of your algorithm. Ac Go As we have learned in lecture, the Huffman code satisfies the Prefix Property, which states that the bit string representing each symbol is not a prefix of the bit string representing any other symbol. One nice property of such codes is that, given a bit string, there is at most one way to decode it back to a sequence of symbols. However, this is not true anymore once we are working with codes that do not satisfy the Prefix Property. For example, consider the code that maps A to 1, B to 01 and C to 101. A bit string 101 can be interpreted in two ways: as C or as AB. Your task is to, given a bit string s, determine whether it is possible to interpret s as a sequence of symbols. The mapping from symbols to bit strings of the code will be given to you as a dictionary d (e.g., in the example, d {A 1, B 01, C: 101}); you may assume = : that you can access each symbol in the dictionary in constant time. (a) Describe an algorithm that solves this problem in at most O(nkl) where n is the length of the input bit string s, k is the number of symbols, and l is an upper bound on the length of the bit strings representing symbols. Please provide a 4-part solution. (b) (Optional) How can you modify the algorithm from part (a) to speed up the runtime to O((n + k)l)?
Expert Answer:
Answer rating: 100% (QA)
1 Algorithm Description a Define your subproblem In this part you are defining the smaller more manageable problems that make up the larger problem Its crucial to clearly specify the function f its pa... View the full answer

Related Book For 

Financial Accounting and Reporting a Global Perspective
ISBN: 978-1408076866
4th edition
Authors: Michel Lebas, Herve Stolowy, Yuan Ding
Posted Date:
Students also viewed these programming questions
-
Hyten Corporation On June 5, 1998, a meeting was held at Hyten Corporation, between Bill Knapp, Director of Marketing/Sales, and John Rich, director of engineering. The purpose of the meeting was to...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Compare sand, die, investment, lost foam, and continuous casting techniques.
-
A Fink roof truss is loaded as shown. Determine the force in members DF, DG, and EG. 4.8 ft 4.8 ft 4.8 ft 4.8 ft 500 500 lb | 500 lh S00 Ib 500 lh ,. 250 lb. 250 Ih D. 9.6 t -14.4 ft 4.4 t- 6 it'6 R...
-
What is check kiting? How might auditors detect kiting?
-
Consider the following cash flow profile and assume MARR is 10 percent/year. a. What does Descartes' rule of signs tell us about the IRR(s) of this project? b. What does Norstrom's criterion tell us...
-
DeWitt Company uses flexible budgets to control its selling expenses. Monthly sales are expected to range from $170,000 to $200,000. Variable costs and their percentage relationship to sales are:...
-
List and describe/discuss the five advantages of intermediate sanctions over traditional probation or incarceration.
-
Two blocks, of masses M = 2.0 kg and 2M, are connected to a spring of spring constant k = 200 N/m that has one end fixed, as shown in Figure. The horizontal surface and the pulley are frictionless,...
-
Read the article Competition and pricing and suppose that you are the manager of a convenience store in a suburban neighborhood. Your location is on the corner of a major intersection with two other...
-
Checkpoint 2 - Advanced Caesar Cipher When encrypted, each letter in the message steps forward multiple letters in the alphabet (A encrypted by five becomes F). When decrypted, each letter in the...
-
Based on your own knowledge and experience, provide FIVE major considerations for choosing software tools to ensure accounting/bookkeeping compliance.
-
Explain what you think would happen if there was error in Mitosis?
-
A certain integrated circuit (IC) represented by the triangular symbol below has a maximum operating voltage of VIC = 5 V before damage is likely to occur. 04 R + 7.2 V+ R2 VIC Integrated Circuit -...
-
A horizontal frictionless table has a small hole in its center. Block A on the table is connected to block B hanging beneath by a string of negligible mass which passes through the hole. Initially, B...
-
(a The issued share capital of Alpha, a limited liability company, is as follows: K Ordinary shares of 10n each 1,000,000 8% Redeemable preference shares of 50n each 500,000 In the year ended 31...
-
What does non-recourse financing mean?
-
Stora Enso is a Finnish integrated global paper producer. Its sales have varied significantly over the past four years. The Group had, in 2011, some 30,000 employees in more than 35 countries...
-
Poulenc & Associates, a consulting firm, was incorporated on 1 June X1. On 30 June, the trial balance shows the following balances for selected accounts: Analysis reveals the following additional...
-
=> Prepare a 15-minute oral presentation on the history of charts of accounts, with particular reference to the French chart of accounts (dating from 1942). => Prepare a 15-minute oral presentation...
-
Which of the following typical topics in an investment policy statement (IPS) is most closely linked to the clients distinctive needs? A. Procedures. B. Investment Guidelines. C. Statement of Duties...
-
The section of the investment policy statement (IPS) that provides information about how the policy may be executed, including investment constraints, is best described as the: A. Investment...
-
A written investment policy statement (IPS) is most likely to succeed if: A. Created by a software program to assure consistent quality. B. It is a collaborative effort of the client and the...

Study smarter with the SolutionInn App