Give a short portrayal of the three sections that make up the Global Situating System (GPS), and
Question:
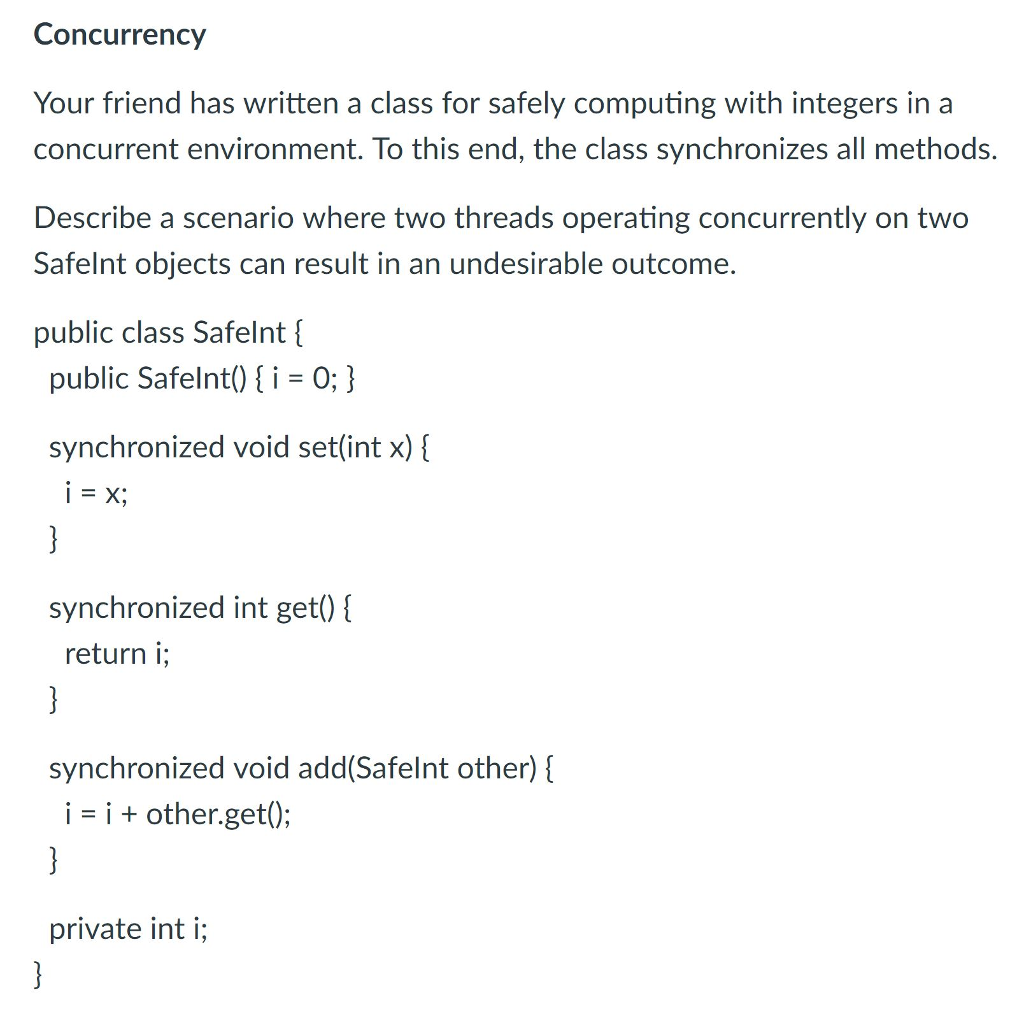
Give a short portrayal of the three sections that make up the Global Situating System (GPS), and their fundamental programming, equipment and data parts. [5 marks] ? [5 marks] (c) What information is communicated in the GPS signs, and how could it be utilized by collectors? [5 marks] (d) Explain a portion of the manners by which an extra correspondence channel can be utilized to help a GPS collector, and what benefits the client could notice. [5 marks] 3 Digital Communication II (a) Describe the OSI (Open Systems Interconnections) reference model and talk about instances of the systems administration works ordinarily connected with each part. [14 marks] (b) What do we mean by layer infringement? Examine a portion of the reasons that could lead a logical convention implementer to participate in layer infringement and outline with a model. [6 marks] 4 Distributed Systems (a) You have been approached to plan an occasion arrangement and total assistance to work above distribute/buy in middleware to be sent in different natural observing situations. Your administration is to publicize and distribute undeniable level occasions important to applications. It might buy into any distributed occasions in the area of sending. Your administration may itself be dispersed. Recognize a rundown of specialized plan issues you would raise with your client earlier to indicating the help exhaustively. [12 marks] (b) By method for an outline show the utilization of vector tickers to execute the conveyance in causal request of multicast messages among individuals from a shut, unstructured interaction bunch. Incorporate a clarification of the message conveyance calculation.
A few banks issue their Automatic Teller Machine (ATM) card clients with an arbitrarily chosen individual indentification number (PIN). Others issue their clients with an underlying PIN just, and let the clients pick their own PIN the first time they utilize the card in an ATM. Portray the benefits and burdens of these methodologies. [5 marks] Once more, a few banks process the client PIN by encoding the record number utilizing DES and a key known distinctly to their focal frameworks and ATMs, taking the first four hex digits of the outcome, supplanting the digits A, . . . , F with 0, . . . , 5 separately, lastly, in the event that the primary digit of the outcome is 0, supplanting it with a 1. What is the likelihood that a crook can get the PIN right given three speculations? [5 marks] However different banks have utilized DES, and a key known distinctly to their focal frameworks and ATMs, to scramble the PIN (whether haphazardly created or client chose); they then, at that point, compose the outcome on the attractive strip on the client's card, so the ATM can check it without reference to the focal framework. Portray the impediments of this course of action. [5 marks] To forestall assaults in view of controlling attractive strips, banks in some nations have moved to utilizing savvy cards. What impact would you expect such a move to have on the occurrence of card-based extortion?