Given a block diagram of an IP datagram as shown below to be sent from a...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
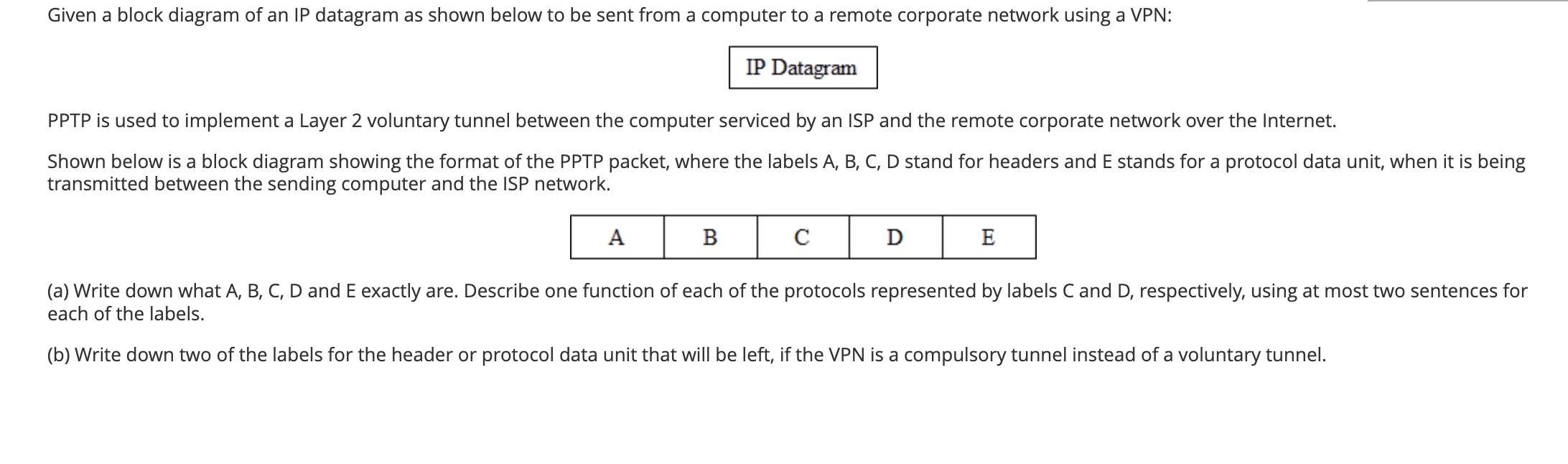
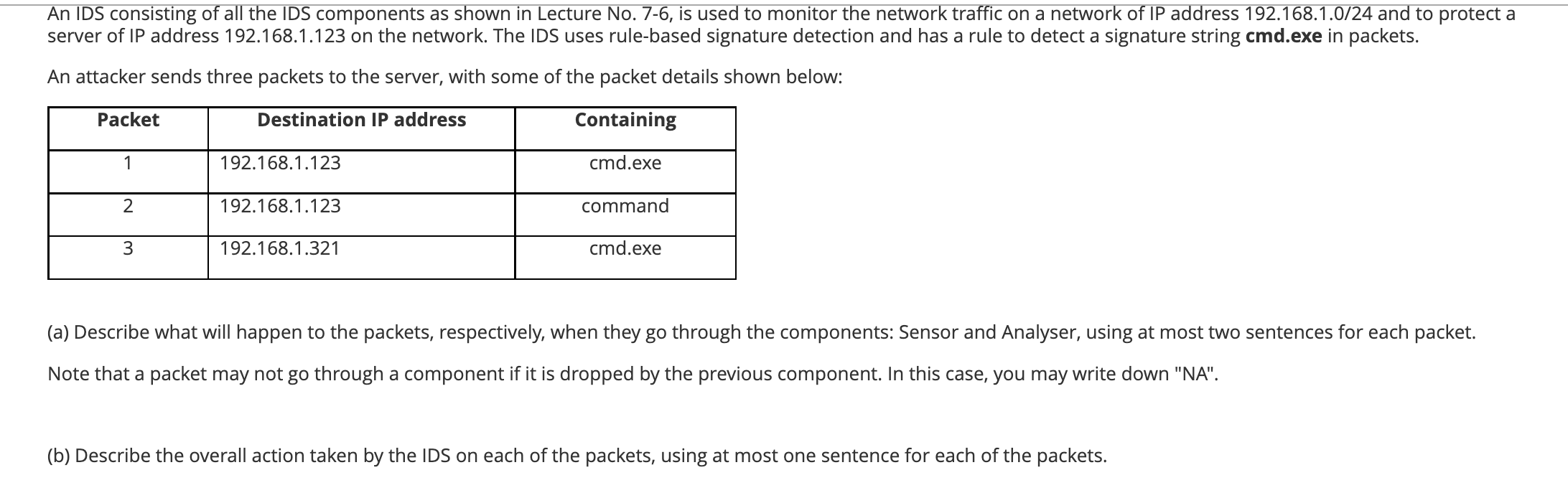
Given a block diagram of an IP datagram as shown below to be sent from a computer to a remote corporate network using a VPN: IP Datagram PPTP is used to implement a Layer 2 voluntary tunnel between the computer serviced by an ISP and the remote corporate network over the Internet. Shown below is a block diagram showing the format of the PPTP packet, where the labels A, B, C, D stand for headers and E stands for a protocol data unit, when it is being transmitted between the sending computer and the ISP network. A B D E (a) Write down what A, B, C, D and E exactly are. Describe one function of each of the protocols represented by labels C and D, respectively, using at most two sentences for each of the labels. (b) Write down two of the labels for the header or protocol data unit that will be left, if the VPN is a compulsory tunnel instead of a voluntary tunnel. An IDS consisting of all the IDS components as shown in Lecture No. 7-6, is used to monitor the network traffic on a network of IP address 192.168.1.0/24 and to protect a server of IP address 192.168.1.123 on the network. The IDS uses rule-based signature detection and has a rule to detect a signature string cmd.exe in packets. An attacker sends three packets to the server, with some of the packet details shown below: Packet Destination IP address 1 192.168.1.123 2 192.168.1.123 3 192.168.1.321 Containing cmd.exe command cmd.exe (a) Describe what will happen to the packets, respectively, when they go through the components: Sensor and Analyser, using at most two sentences for each packet. Note that a packet may not go through a component if it is dropped by the previous component. In this case, you may write down "NA". (b) Describe the overall action taken by the IDS on each of the packets, using at most one sentence for each of the packets. Given a block diagram of an IP datagram as shown below to be sent from a computer to a remote corporate network using a VPN: IP Datagram PPTP is used to implement a Layer 2 voluntary tunnel between the computer serviced by an ISP and the remote corporate network over the Internet. Shown below is a block diagram showing the format of the PPTP packet, where the labels A, B, C, D stand for headers and E stands for a protocol data unit, when it is being transmitted between the sending computer and the ISP network. A B D E (a) Write down what A, B, C, D and E exactly are. Describe one function of each of the protocols represented by labels C and D, respectively, using at most two sentences for each of the labels. (b) Write down two of the labels for the header or protocol data unit that will be left, if the VPN is a compulsory tunnel instead of a voluntary tunnel. An IDS consisting of all the IDS components as shown in Lecture No. 7-6, is used to monitor the network traffic on a network of IP address 192.168.1.0/24 and to protect a server of IP address 192.168.1.123 on the network. The IDS uses rule-based signature detection and has a rule to detect a signature string cmd.exe in packets. An attacker sends three packets to the server, with some of the packet details shown below: Packet Destination IP address 1 192.168.1.123 2 192.168.1.123 3 192.168.1.321 Containing cmd.exe command cmd.exe (a) Describe what will happen to the packets, respectively, when they go through the components: Sensor and Analyser, using at most two sentences for each packet. Note that a packet may not go through a component if it is dropped by the previous component. In this case, you may write down "NA". (b) Describe the overall action taken by the IDS on each of the packets, using at most one sentence for each of the packets.
Expert Answer:

Posted Date:
Students also viewed these computer network questions
-
Compare and contrast the two prominent data analysis techniques that could be used in a qualitative descriptive study: thematic analysis and content analysis. Differentiate the different types of...
-
Let A, B be sets. Define: (a) the Cartesian product (A B) (b) the set of relations R between A and B (c) the identity relation A on the set A [3 marks] Suppose S, T are relations between A and B, and...
-
Explain informally the difference between Godel's completeness theorem and his first incompleteness theorem. [8 marks] (b) State the meaning of Hoare triples {P} C {Q} in separation logic. [3 marks]...
-
Question: Calculate the mass of the liquid for each trial. (Subtract the mass of the empty graduated cylinder from the mass of the graduated cylinder with liquid.) Trial 1 10.6 Trial 2 10.0 Trial 3...
-
The City of Titanville established an Investment Trust Fund for Bay Town and Valley City. The cities contributed $ 200,000 and $ 100,000, respectively, to the fund. During 2012 the following...
-
Suppose you are asked to make a loan for 10% from one year for now; you decided to compare interest rates with Government bonds and make at least 2% premium over that. One year bond has 5% and two...
-
Enter up the books from the following details for the month of March, and extract a trial balance as at 31 March 19X6. 33 2 19X6 March 1 Started business with 800 in the bank. Bought goods on credit...
-
Castle Leasing Company signs a lease agreement on January 1, 2014, to lease electronic equipment to Jan Way Company. The term of the noncancelable lease is 2 years, and payments are required at the...
-
2. Rise & Shine is a bed and breakfast establishment at the heart of the city. The guests appreciate its gourmet breakfasts and individually decorated rooms. The overhead budget for the most recen...
-
Determine whether the following definitions are stipulative, lexical, precising, Theoretical, or persuasive 1. Blind means, for federal income-tax purposes, either the inability to see better than...
-
Requirement: Calculate the IRR of this project.?Should the project be accepted? Total assets Short-term assets/Cash Current senior debt Net senior debt Subordinated debt (quasi-equity) Retained...
-
National League Gear has two classes of stock authorized: 6%, $20 par preferred, and $5 par value common. The following transactions affect stockholders' equity during 2024, National League's first...
-
How many pars should a hotel have for linen and terry? Explain why each par is needed
-
How do field salespeople differ from inside salespeople (including the sales structure of your firm in the answer)? Discuss Briefly?
-
During the month of January, an employer incurred the following payroll taxes: FICA Social Security taxes of $260.40, FICA Medicare taxes of $60.90, FUTA taxes of $25.20, and SUTA taxes of $226.80....
-
Ivanhoe Company is considering two different, mutually exclusive capital expenditure proposals. Project A will cost $415,000, has an expected useful life of 11 years and a salvage value of zero, and...
-
Suppose that due to the COVID-19 pandemic, millions of households are spending much more time at home. They are all looking for things to do and ways to spend their time. How might we model this...
-
Distinguish among total-moisture content, free-moisture content, equilibrium-moisture content, unbound moisture, and bound moisture.
-
Heshimu, Inc., has a \($1,000\) face value convertible bond issue that is currently selling in the market for \($975.\) Each bond is exchangeable at any time for 40 shares of the companys stock. The...
-
Consider the following two congestion networks with the indicated cost functions for a flow \(x\) on the respective edge; for example, \(50+x\) is short for \(c(x)=50+x\). Note that different edges...
-
Consider the following congestion network with three nodes. As shown, an edge has the cost function \(c(x)=x\) if the flow (number of users) on that edge is \(x\), except for the edges \(v u\) and...

Study smarter with the SolutionInn App

