Question: Given the following byte stuffing scheme: Special Characters Character in data Character sent soh eot esc Character soh eot esc Character to Hex Code
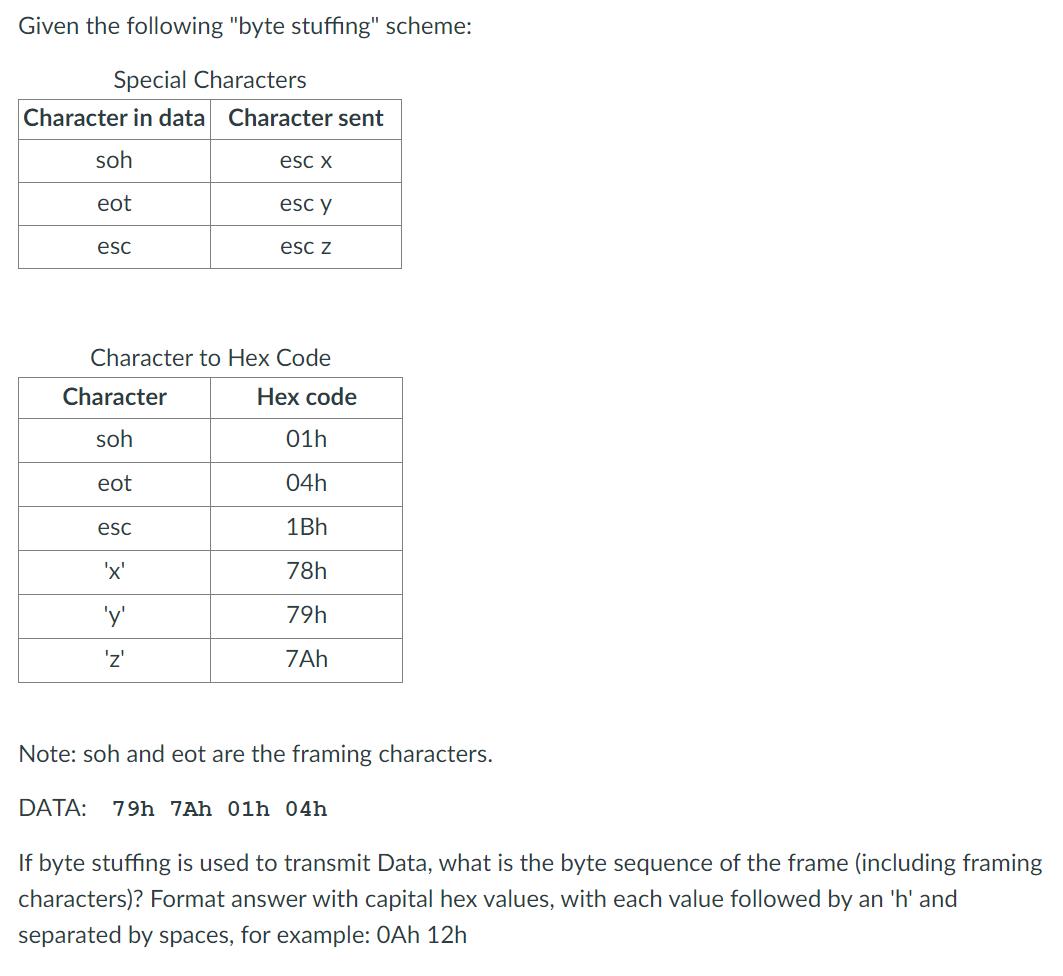
Given the following "byte stuffing" scheme: Special Characters Character in data Character sent soh eot esc Character soh eot esc Character to Hex Code 'x' esc x 'y' 'Z' esc y esc z Hex code 01h 04h 1Bh 78h 79h 7Ah Note: soh and eot are the framing characters. DATA: 79h 7Ah 01h 04h If byte stuffing is used to transmit Data, what is the byte sequence of the frame (including framing characters)? Format answer with capital hex values, with each value followed by an 'h' and separated by spaces, for example: 0Ah 12h
Step by Step Solution
3.35 Rating (155 Votes )
There are 3 Steps involved in it
Byte stuffing is a technique used in data communication to differentiate data from control informati... View full answer

Get step-by-step solutions from verified subject matter experts


