Question: Given the following method to be considered within the Single Linked List class, what does this method do public boolean Undefined() { Node ptr
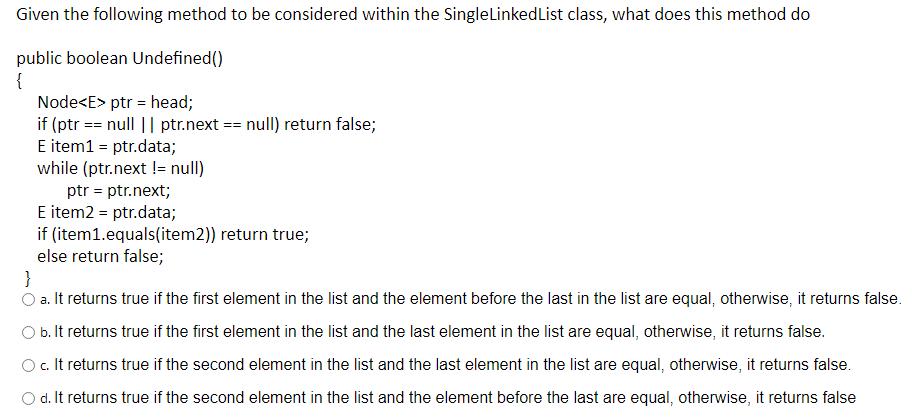
Given the following method to be considered within the Single Linked List class, what does this method do public boolean Undefined() { Node ptr = head; if (ptr == null || ptr.next == null) return false; E item1 = ptr.data; while (ptr.next != null) ptr = ptr.next; E item2 = ptr.data; if (item1.equals(item2)) return true; else return false; } O a. It returns true if the first element in the list and the element before the last in the list are equal, otherwise, it returns false. O b. It returns true if the first element in the list and the last element in the list are equal, otherwise, it returns false. O c. It returns true if the second element in the list and the last element in the list are equal, otherwise, it returns false. d. It returns true if the second element in the list and the element before the last are equal, otherwise, it returns false
Step by Step Solution
There are 3 Steps involved in it
The detailed answer for the above question is provided below The given method in the Sin... View full answer

Get step-by-step solutions from verified subject matter experts


