Question: Given the following protocol in which the sender performs the following operation: y = Ek (x Il sigkpr (H (x))), Where x is the message,
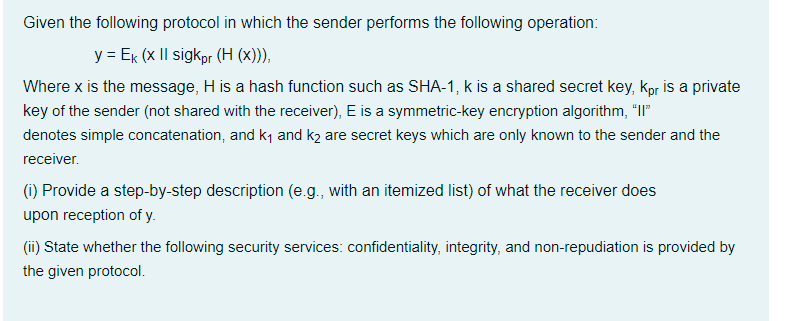
Given the following protocol in which the sender performs the following operation: y = Ek (x Il sigkpr (H (x))), Where x is the message, H is a hash function such as SHA-1, k is a shared secret key, kpr is a private key of the sender (not shared with the receiver), E is a symmetric-key encryption algorithm, T denotes simple concatenation, and ky and k2 are secret keys which are only known to the sender and the receiver (1) Provide a step-by-step description (e.g., with an itemized list) of what the receiver does upon reception of y. (i) State whether the following security services: confidentiality, integrity, and non-repudiation is provided by the given protocol
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


