Question: Group Problem Set # 2 TEAM # NAMES (1) Worth 50 pts. Describe and explain in detail why the forms of non-repudiation (non- repudiation of
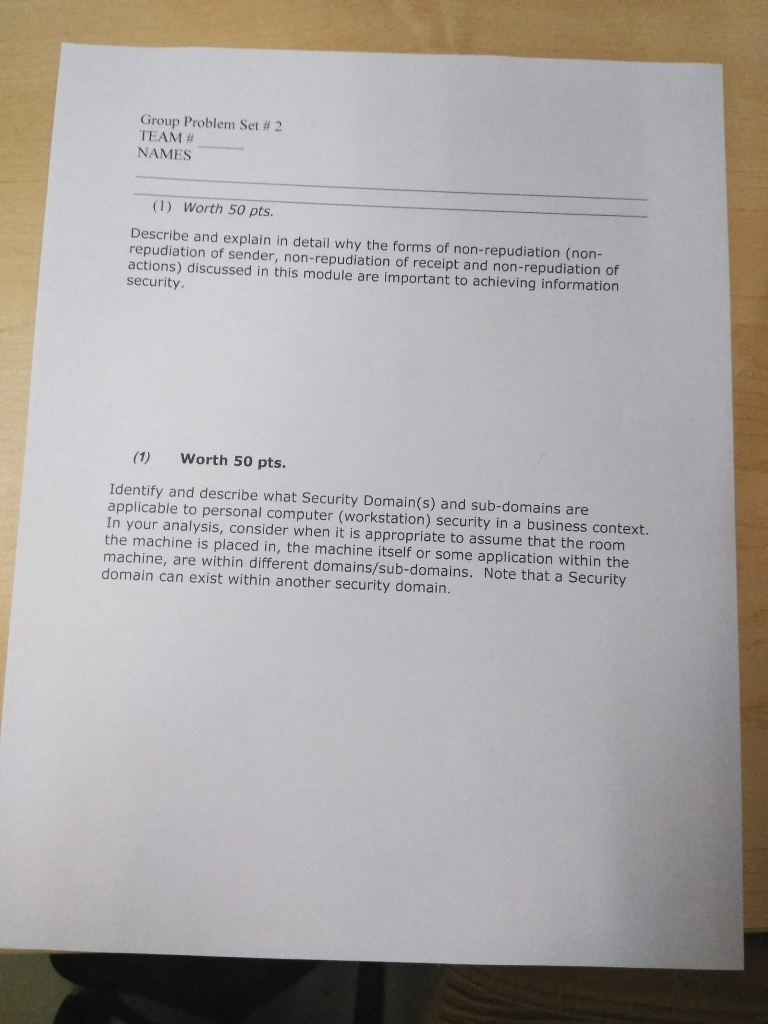
Group Problem Set # 2 TEAM # NAMES (1) Worth 50 pts. Describe and explain in detail why the forms of non-repudiation (non- repudiation of sender, non-repudiation of receipt and non-repudiation of actions) discussed in this module are important to achieving information security. (1) Worth 50 pts. Identify and describe what Security Domain(s) and sub-domains are applicable to personal computer (workstation) security in a business context In your analysis, consider when it is appropriate to assume that the room the machine is placed in, the machine itself or some application within the machine, are within different domains/sub-domains. Note that a Security domain can exist within another security domain
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


