Question: Hello! I want example for each attack in the right with the explanation of how to distinguish between them Threat Consequence Unauthorized Threat Action (attack)
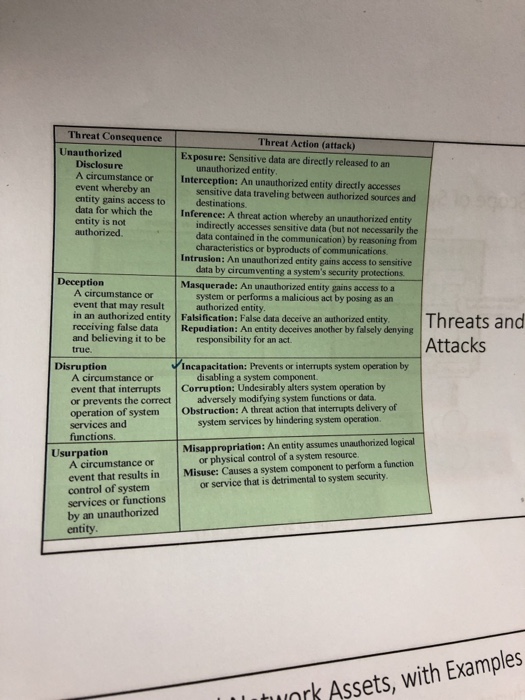
Threat Consequence Unauthorized Threat Action (attack) Exposure: Sensitive data are directly released to an Disclosu re unauthorized entity A circumstance or Interception: An unauthorized entity directly accesses event whereby an entity gains access to data for which the Inference: A threat action whereby an unauthorized entity entity is not authorized sensitive data traveling between authorized sources and destinations indirectly accesses sensitive data (but not necessarily the data contained in the communication) by reasoning from characteristics or byproducts of communications Intrusion: An unauthorized entity gains access to sensitive data by circumventing a system's security protections Masquerade: An unauthorized entity gains access to a A circumstance or event that may result system or performs a malicious act by posing as an authorized entity in an authorized entity Falsification: False data deceive an authorized entity receiving false data Repudiation: An entity deceives another by falsely denying and believing it to be responsibility for an act true. Attacks Disruption Incapacitation: Prevents or interrupts system operation by disabling a system component A circumstance or event that interrupts Corruption: Undesirably alters system operation by or prevents the correct adversely modifying system functions or data operation of system Obstruction: A threat action that interrupts delivery of services and system services by hindering system operation. functions Usurpatiorn Misappropriation: An entity assumes unauthorized logical or physical control of a system resource. event that results in Misuse: Causes a system component to perform a function control of system services or functions by an unauthorized entity A circumstance or or service that is detrimental to system security. nrk Assets, with Examples
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


