Here we are investigating various ways of how we can use a CPA- secure scheme to...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
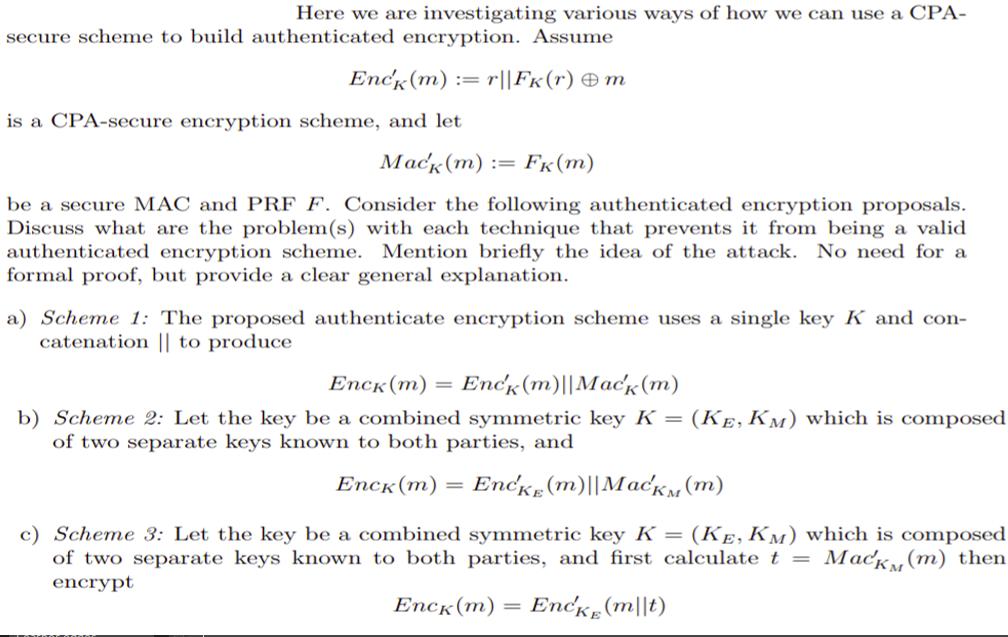
Here we are investigating various ways of how we can use a CPA- secure scheme to build authenticated encryption. Assume Enck (m) : r||FK(r) m is a CPA-secure encryption scheme, and let Mack (m) := Fk (m) be a secure MAC and PRF F. Consider the following authenticated encryption proposals. Discuss what are the problem(s) with each technique that prevents it from being a valid authenticated encryption scheme. Mention briefly the idea of the attack. No need for a formal proof, but provide a clear general explanation. a) Scheme 1: The proposed authenticate encryption scheme uses a single key K and con- catenation || to produce Enck (m) = Enck (m) | Mack (m) b) Scheme 2: Let the key be a combined symmetric key K = (KE, KM) which is composed of two separate keys known to both parties, and Enck (m) Encke (m)||MacKM (m) c) Scheme 3: Let the key be a combined symmetric key K = (KE, KM) which is composed of two separate keys known to both parties, and first calculate t = Mack (m) then encrypt Enck (m) Encke (mt) Here we are investigating various ways of how we can use a CPA- secure scheme to build authenticated encryption. Assume Enck (m) : r||FK(r) m is a CPA-secure encryption scheme, and let Mack (m) := Fk (m) be a secure MAC and PRF F. Consider the following authenticated encryption proposals. Discuss what are the problem(s) with each technique that prevents it from being a valid authenticated encryption scheme. Mention briefly the idea of the attack. No need for a formal proof, but provide a clear general explanation. a) Scheme 1: The proposed authenticate encryption scheme uses a single key K and con- catenation || to produce Enck (m) = Enck (m) | Mack (m) b) Scheme 2: Let the key be a combined symmetric key K = (KE, KM) which is composed of two separate keys known to both parties, and Enck (m) Encke (m)||MacKM (m) c) Scheme 3: Let the key be a combined symmetric key K = (KE, KM) which is composed of two separate keys known to both parties, and first calculate t = Mack (m) then encrypt Enck (m) Encke (mt)
Expert Answer:
Related Book For 

Cost Management A Strategic Emphasis
ISBN: 978-0078025532
6th edition
Authors: Edward Blocher, David Stout, Paul Juras, Gary Cokins
Posted Date:
Students also viewed these programming questions
-
Let A, B be sets. Define: (a) the Cartesian product (A B) (b) the set of relations R between A and B (c) the identity relation A on the set A [3 marks] Suppose S, T are relations between A and B, and...
-
can someone solve this Modern workstations typically have memory systems that incorporate two or three levels of caching. Explain why they are designed like this. [4 marks] In order to investigate...
-
In your own words, define or explain the terms or symbols (a) (b) [ ]; (c) Spectator ion; (d) Weak acid.
-
Search on the Internet for the 2015 annual report for Sanofi-Aventis. Find the accounts receivable disclosure note. Required: 1. Sanofi-Aventis subtracts "impairment" from the gross value of accounts...
-
Flicker, Inc., a closely held corporation, acquired a passive activity this year. Gross income from operations of the activity was $160,000. Operating expenses, not including depreciation, were...
-
What is a decomposer? What organisms function as decomposers in most communities?
-
Joshua Hill, Bates & Hill Fabricators production manager, has just completed the companys production budget and manufacturing overhead budget for the first quarter. He also has received the direct...
-
17) The network analysts assume that there is a linear relationship between the number of users accessing. the network and the load of network traffic. Write a Python program for network traffic...
-
Ryan and Blake Lively are married filing jointly taxpayers. Ryan's birthdate is August 10, 1982 and Social Security number is 434-14-4448. Blake's birthdate is March 19, 1983 and their Social...
-
Plenty of work goes into developing a persuasive narrative. The oral presentation of that narrative is many times your only opportunity to tel it, so how can you make the best of it, whether in front...
-
13. The innermost moon of Jupiter orbits the planet with a radius of 422 of Jupiter? 103 km and a period of 1.77 days. What is the mass 14. Two moons orbit a planet in nearly circular orbits. Moon A...
-
What mitigation techniques for political, social, and economic risks should be taken by an MNC considering operation in Brazil take? Explain
-
You are considering purchasing a business that is being auctioned to many strategic buyers (it's being sold in a competitive market). You estimate that the project has a CAPM beta of 1.5. You believe...
-
QUESTION 2 On the first day of each month, starting in May, 2007 Smith deposited $1000 into a bank account. During 2007 the account earned a nominal annual rate of interest of 6% compounded monthly....
-
1. The riskless interest rate is 2%. You hold a portfolio consisting of short-term safe assets and the market portfolio of risky assets, which has a mean return of 7% and a standard deviation of 20%....
-
A rifle bullet with mass 7.00 g and initial horizontal velocity 290 m/s strikes and embeds itself in a block with mass 0.993 kg that rests on a frictionless surface and is attached to one end of an...
-
The baseball player A hits the ball from a height of 3.36 ft with an initial velocity of 34.8 ft/s. 0.14 seconds after the ball is hit, player B who is standing 15 ft away from home plate begins to...
-
Maxwell's direct labor costs for the month of January follow: Problem Information Direct labor hourly rate paid............................................. 28.5 Total standard direct labor hours for...
-
Data Performance, a computer software consulting company, has three major functional areas: computer programming, information systems consulting, and software training. Carol Bingham, a pricing...
-
One way the value chain can be helpful is to provide a basis for a company to determine the full cost of its product or service over the entire value chain. Often companies tend to focus only on...
-
In the context of the proof of Theorem 4.3, prove that \[\lim _{n ightarrow \infty}\left|\int_{a}^{b} g_{m}(x) d F(x)-\int_{a}^{b} g(x) d F(x)ight| for any \(\delta_{\varepsilon}>0\). Theorem 4.3...
-
Let \(\mathbf{X}\) be a \(d\)-dimensional random vector with distribution function \(F\). Let \(g: \mathbb{R}^{d} ightarrow \mathbb{R}\) be a continuous function such that \(|g(\mathbf{x})| \leq b\)...
-
Let \(\left\{\mathbf{X}_{n}ight\}_{n=1}^{\infty}\) be a sequence of \(d\)-dimensional random vectors that converge in distribution to a random vector \(\mathbf{X}\) as \(n ightarrow \infty\). Let...

Study smarter with the SolutionInn App



