Question: How can cryptography be used to create an unforgeable message? What other terms can be used to refer to a secret and a public
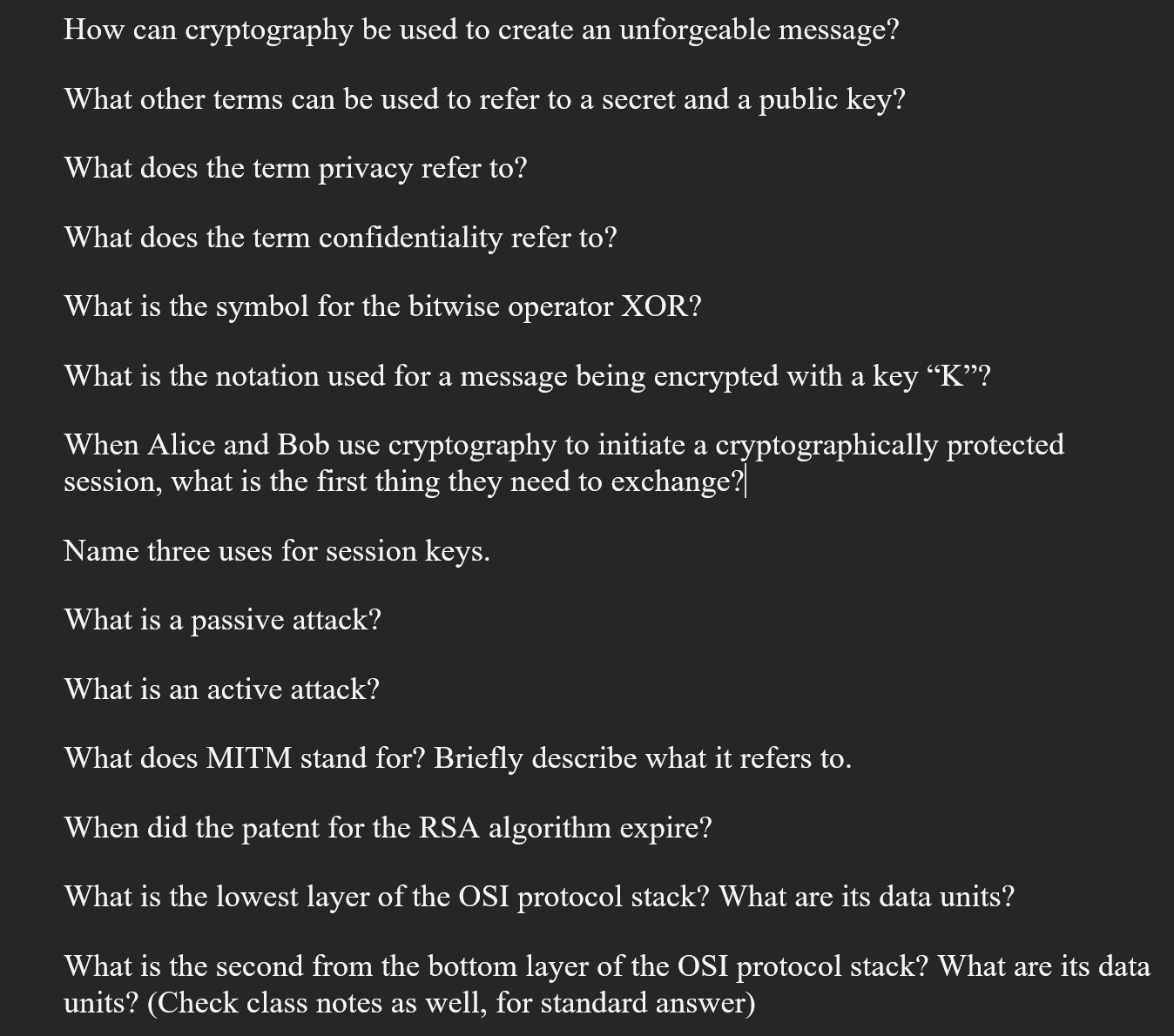
How can cryptography be used to create an unforgeable message? What other terms can be used to refer to a secret and a public key? What does the term privacy refer to? What does the term confidentiality refer to? What is the symbol for the bitwise operator XOR? What is the notation used for a message being encrypted with a key K? When Alice and Bob use cryptography to initiate a cryptographically protected session, what is the first thing they need to exchange? Name three uses for session keys. What is a passive attack? What is an active attack? What does MITM stand for? Briefly describe what it refers to. When did the patent for the RSA algorithm expire? What is the lowest layer of the OSI protocol stack? What are its data units? What is the second from the bottom layer of the OSI protocol stack? What are its data units? (Check class notes as well, for standard answer)
Step by Step Solution
3.36 Rating (152 Votes )
There are 3 Steps involved in it
Lets address each question one by one 1 How can cryptography be used to create an unforgeable message Cryptography can be used to create an unforgeable message through the use of digital signatures A ... View full answer

Get step-by-step solutions from verified subject matter experts


