Question: How much management data would be generated in a centralized management approach (Figure 2), assuming data collection of 7 simple network management protocol counters
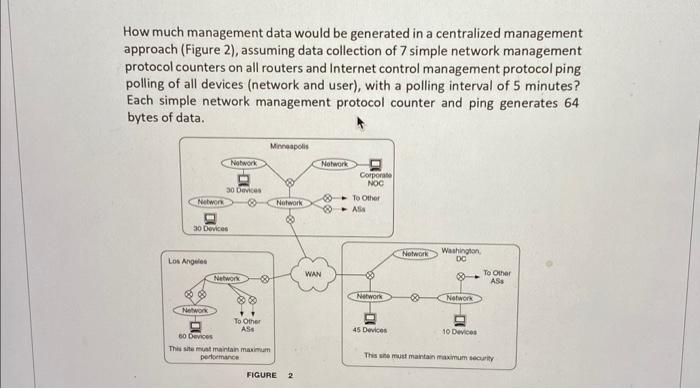
How much management data would be generated in a centralized management approach (Figure 2), assuming data collection of 7 simple network management protocol counters on all routers and Internet control management protocol ping polling of all devices (network and user), with a polling interval of 5 minutes? Each simple network management protocol counter and ping generates 64 bytes of data. Network 30 Devices Los Angeles Network Network 30 Devices Network Minneapolis To Other ASS 60 Devices This site must maintain maximum performance Network FIGURE 2 Network WAN Corporate NOC To Other Ass Network 45 Devices Network Washington, DO Network 10 Devices To Other ASS This site must maintain maximum security
Step by Step Solution
3.57 Rating (147 Votes )
There are 3 Steps involved in it
To calculate the amount of management data generated per polling interval we need to consider both t... View full answer

Get step-by-step solutions from verified subject matter experts


