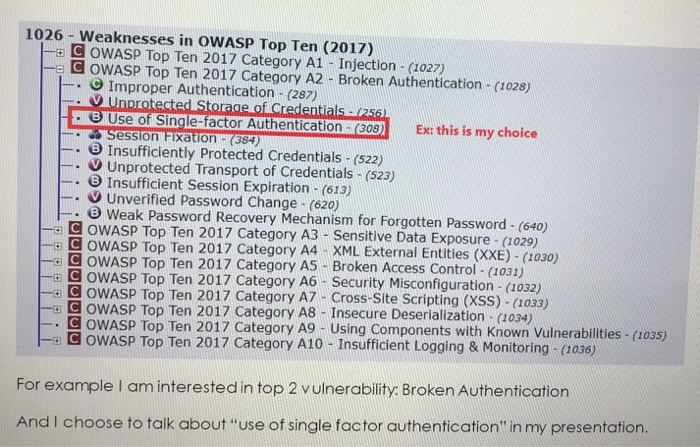
I choose this topic: CWE-640: week password recovery mechanism for forgotten password Description: Knowing Security Weaknesses. This
Fantastic news! We've Found the answer you've been seeking!
Question:
I choose this topic:
CWE-640: week password recovery mechanism for forgotten password
Transcribed Image Text:
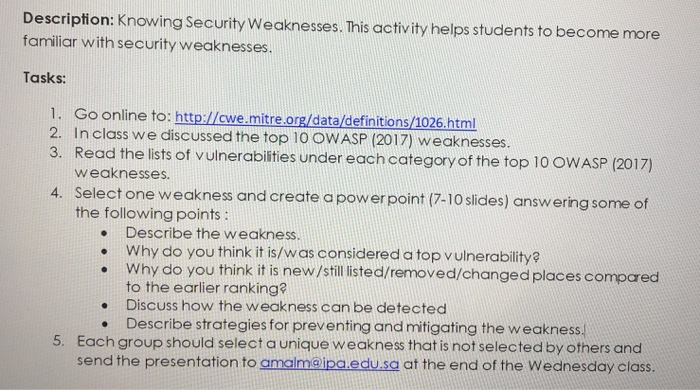
Description: Knowing Security Weaknesses. This activity helps students to become more familiar with security weaknesses. Tasks: 1. Go online to: http://cwe.mitre.org/data/definitions/1026.html 2. In class we discussed the top 10 OWASP (2017) weaknesses. 3. Read the lists of vulnerabilities under each category of the top 10 OWASP (2017) weaknesses. 4. Select one weakness and create a power point (7-10 slides) answering some of the following points: Describe the weakness. Why do you think it is/was considered a top vulnerability? Why do you think it is new/still listed/removed/changed places compared to the earlier ranking? Discuss how the weakness can be detected ● Describe strategies for preventing and mitigating the weakness. 5. Each group should select a unique weakness that is not selected by others and send the presentation to amalm@ipa.edu.sa at the end of the Wednesday class. ● ● ● 1026 - Weaknesses in OWASP Top Ten (2017) -8 COWASP Top Ten 2017 Category A1 - Injection - (1027) COWASP Top Ten 2017 Category A2 - Broken Authentication - (1028) Improper Authentication - (287) Unprotected Storage of Credentials - (256) B Use of Single-factor Authentication - (308) Session Fixation - (384) Insufficiently Protected Credentials - (522) Unprotected Transport of Credentials - (523) Insufficient Session Expiration - (613) Unverified Password Change - (620) . . . Ex: this is my choice 8 Weak Password Recovery Mechanism for Forgotten Password - (640) OWASP Top Ten 2017 Category A3 - Sensitive Data Exposure - (1029) XML External Entities (XXE) - (1030) Broken Access Control - (1031) E3 COWASP Top Ten 2017 Category A4 © COWASP Top Ten 2017 Category A5 D COWASP Top Ten 2017 Category A6- Security Misconfiguration - (1032) O COWASP Top Ten 2017 Category A7- Cross-Site Scripting (XSS) - (1033) Insecure Deserialization - (1034) D OWASP Top Ten 2017 Category A8 OWASP Top Ten 2017 Category A9 Using Components with Known Vulnerabilities - (1035) OWASP Top Ten 2017 Category A10 - Insufficient Logging & Monitoring - (1036) For example I am interested in top 2 vulnerability: Broken Authentication And I choose to talk about use of single factor authentication in my presentation. Description: Knowing Security Weaknesses. This activity helps students to become more familiar with security weaknesses. Tasks: 1. Go online to: http://cwe.mitre.org/data/definitions/1026.html 2. In class we discussed the top 10 OWASP (2017) weaknesses. 3. Read the lists of vulnerabilities under each category of the top 10 OWASP (2017) weaknesses. 4. Select one weakness and create a power point (7-10 slides) answering some of the following points: Describe the weakness. Why do you think it is/was considered a top vulnerability? Why do you think it is new/still listed/removed/changed places compared to the earlier ranking? Discuss how the weakness can be detected ● Describe strategies for preventing and mitigating the weakness. 5. Each group should select a unique weakness that is not selected by others and send the presentation to amalm@ipa.edu.sa at the end of the Wednesday class. ● ● ● 1026 - Weaknesses in OWASP Top Ten (2017) -8 COWASP Top Ten 2017 Category A1 - Injection - (1027) COWASP Top Ten 2017 Category A2 - Broken Authentication - (1028) Improper Authentication - (287) Unprotected Storage of Credentials - (256) B Use of Single-factor Authentication - (308) Session Fixation - (384) Insufficiently Protected Credentials - (522) Unprotected Transport of Credentials - (523) Insufficient Session Expiration - (613) Unverified Password Change - (620) . . . Ex: this is my choice 8 Weak Password Recovery Mechanism for Forgotten Password - (640) OWASP Top Ten 2017 Category A3 - Sensitive Data Exposure - (1029) XML External Entities (XXE) - (1030) Broken Access Control - (1031) E3 COWASP Top Ten 2017 Category A4 © COWASP Top Ten 2017 Category A5 D COWASP Top Ten 2017 Category A6- Security Misconfiguration - (1032) O COWASP Top Ten 2017 Category A7- Cross-Site Scripting (XSS) - (1033) Insecure Deserialization - (1034) D OWASP Top Ten 2017 Category A8 OWASP Top Ten 2017 Category A9 Using Components with Known Vulnerabilities - (1035) OWASP Top Ten 2017 Category A10 - Insufficient Logging & Monitoring - (1036) For example I am interested in top 2 vulnerability: Broken Authentication And I choose to talk about use of single factor authentication in my presentation.
Expert Answer:

Related Book For 

Auditing Cases An Interactive Learning Approach
ISBN: 978-0133852103
6th edition
Authors: Mark S. Beasley, Frank A. Buckless, Steven M. Glover, Douglas F. Prawitt
Posted Date:
Students also viewed these programming questions
-
Choose either the topic of global payments or bundled payments and respond to the following: Summarize how your selected topic functions within healthcare operational management. Explain how it can...
-
Choose a current topic related to Object Oriented Systems Analysis and Design. Make sure your topic is related to Object Oriented Systems Analysis and Design.
-
Choose a topic in motor learning or control and/or disease. If disease, it must be about motor learning and control aspects. Find three EXPERIMENTAL articles (> 2012) that have explored aspects of...
-
Historically, investment spending has experienced more extreme upward and downward swings than consumer spending. Why do you think this is so?
-
The cash records of Satter Company show the following four situations. 1. The June 30 bank reconciliation indicated that deposits in transit total $920. During July, the general ledger account Cash...
-
A 0.635-cm hydraulic line suddenly ruptures 8 m from a reservoir with a gage pressure of 207 kPa. Compare the laminar and inviscid flow rates from the ruptured line in cubic meters per second.
-
Otis Carpenter opened a medical practice in Alexandria, Virginia. Requirement 1. Record the preceding transactions in the journal of Otis Carpenter, M.D., RC. Include an explanation with each entry....
-
The Excel file Salary Data provides information on current salary, beginning salary, previous experience (in months) when hired, and total years of education for a sample of 100 employees in a firm....
-
Thandiworks as a portfolio manager at VBS bank, which is a registered financial services provider. Over the weekend, she attended a friend'sbraaiparty.Nandi, a friend of hers, mentioned that she was...
-
Create a query in Design view, using the Cap1 Inventory table to answer the question For the supplier ID of SUPP-06, for each item name and retail price, what is the markup for each item if marked up...
-
XYZ Corporation began operations on January 1, 2020. Presented below is selected information related to XYZ on December 31, 2020. Prepare an Income statement for XYZ company. Equipment 435,000...
-
A large textile company is trying to decide among three options for a process. The costs associated with these alternatives are shown below. Alternative Y will need an upgrade of $9700 at the end of...
-
Again, as a consultant to Mr. Entrepreneur, you are asked to rank the proposals using the IRR (Internal Rate of Return) method. Which project should be selected under the IRR approach? What is the...
-
Sodium chloride is the primary salt dissolved in ocean water. For every liter, there are about 35 grams of salt dissolved in ocean water, which corresponds to a salt concentration of 0.6 moles/liter,...
-
The following information was reported in the December 31 financial statements of National Airways, Incorporated (listed alphabetically, amounts in millions). Accounts Payable Accounts Receivable...
-
Howard Jones is the Chief Financial Officer (CFO) for Swan Company which makes special order printers for personal computers. As his assistant, he wants you to compute certain items of information...
-
- Describe how a budget can help you ensure that you spend your money wisely. Explain how you would arrange the columns and rows to accomplish your task. Identify how you could use color and cell...
-
Citing a scientific article, explain in your own words, how DNA fingerprinting has been used in forensic science to solve crimes and why it may not always be accurate or effective.
-
Some will argue that KPMG inappropriately subordinated its judgments to Xerox preferences. How could accounting firms ensure that auditors do not subordinate their judgments to client preferences on...
-
Given the technology linkages between business partners in eBusiness systems, how might an eBusiness system like Harley-Davidson's increase business risks for its business partners?
-
Based on your review of the transcript, to what extent do you observe any of the tendencies that might create bias in regards to your professional judgment about the reasonableness of the allowance...
-
How does the presence of a whistle-blowing process improve quality control and independence at a public accounting firm?
-
Trish Mulcahy, a new junior in your office, says that she does not understand why she cannot work on the audit of a company that is a client of your firm and that is owned by her uncle. Trish says...
-
How do these standards differ for (1) errors, (2) frauds, (3) direct-effect illegal acts, and (4) far-removed-effect illegal acts?

Study smarter with the SolutionInn App