Question: (i) Consider the LLC which uses the flag bits with bit stuffing method for data framing. The sending LLC receives the stream of data shown
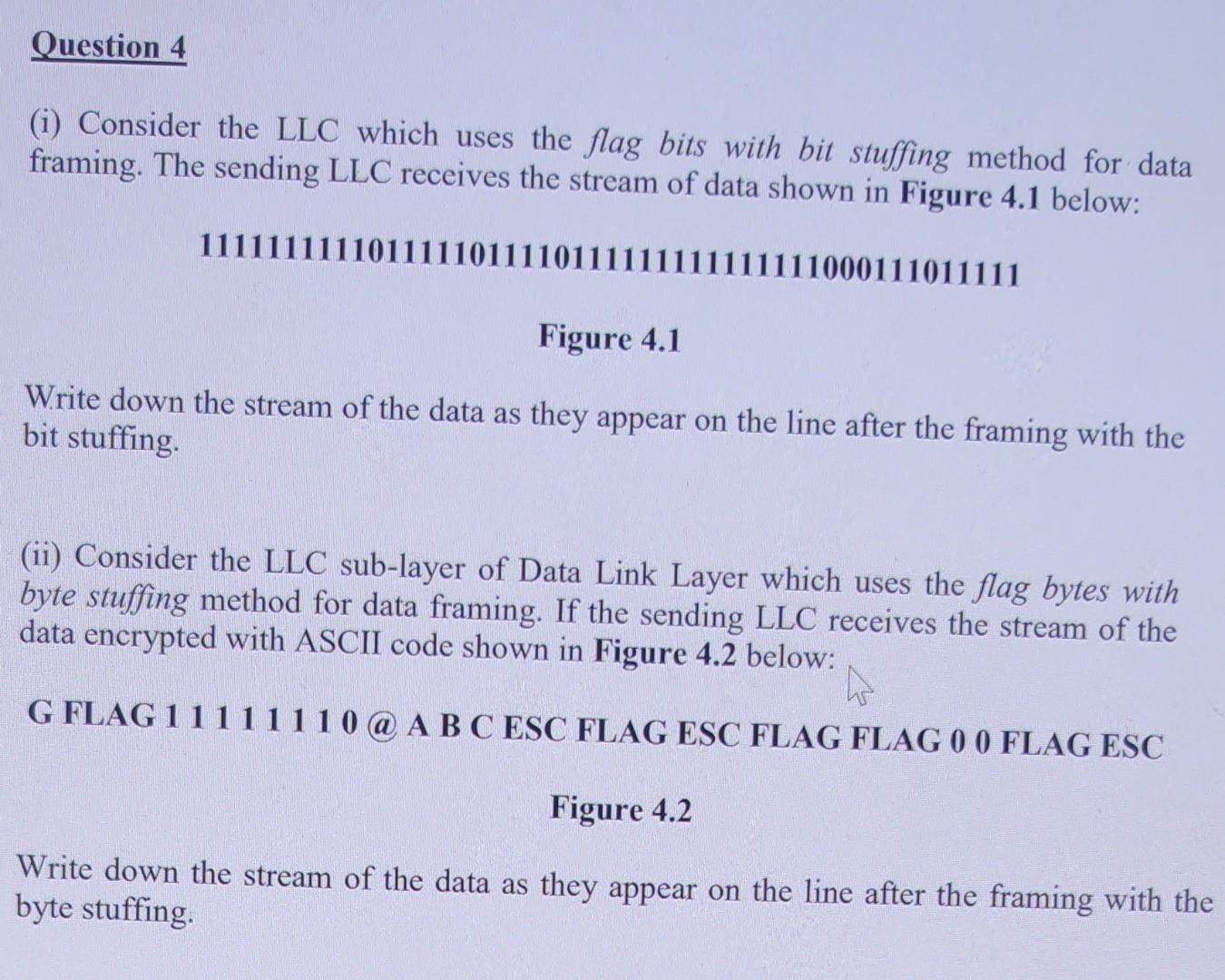
(i) Consider the LLC which uses the flag bits with bit stuffing method for data framing. The sending LLC receives the stream of data shown in Figure 4.1 below: 1111111111011111011110111111111111111000111011111 Figure 4.1 Write down the stream of the data as they appear on the line after the framing with the bit stuffing. (ii) Consider the LLC sub-layer of Data Link Layer which uses the flag bytes with byte stuffing method for data framing. If the sending LLC receives the stream of the data encrypted with ASCII code shown in Figure 4.2 below: G FLAG 11111110 A B C ESC FLAG ESC FLAG FLAG 00 FLAG ESC Figure 4.2 Write down the stream of the data as they appear on the line after the framing with the byte stuffing. (i) Consider the LLC which uses the flag bits with bit stuffing method for data framing. The sending LLC receives the stream of data shown in Figure 4.1 below: 1111111111011111011110111111111111111000111011111 Figure 4.1 Write down the stream of the data as they appear on the line after the framing with the bit stuffing. (ii) Consider the LLC sub-layer of Data Link Layer which uses the flag bytes with byte stuffing method for data framing. If the sending LLC receives the stream of the data encrypted with ASCII code shown in Figure 4.2 below: G FLAG 11111110 A B C ESC FLAG ESC FLAG FLAG 00 FLAG ESC Figure 4.2 Write down the stream of the data as they appear on the line after the framing with the byte stuffing
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


