Question: I need a solution ASAP please Problem 2: Return oriented programming Suppose an attacker finds the following code fragments in the libc library once it
I need a solution ASAP please 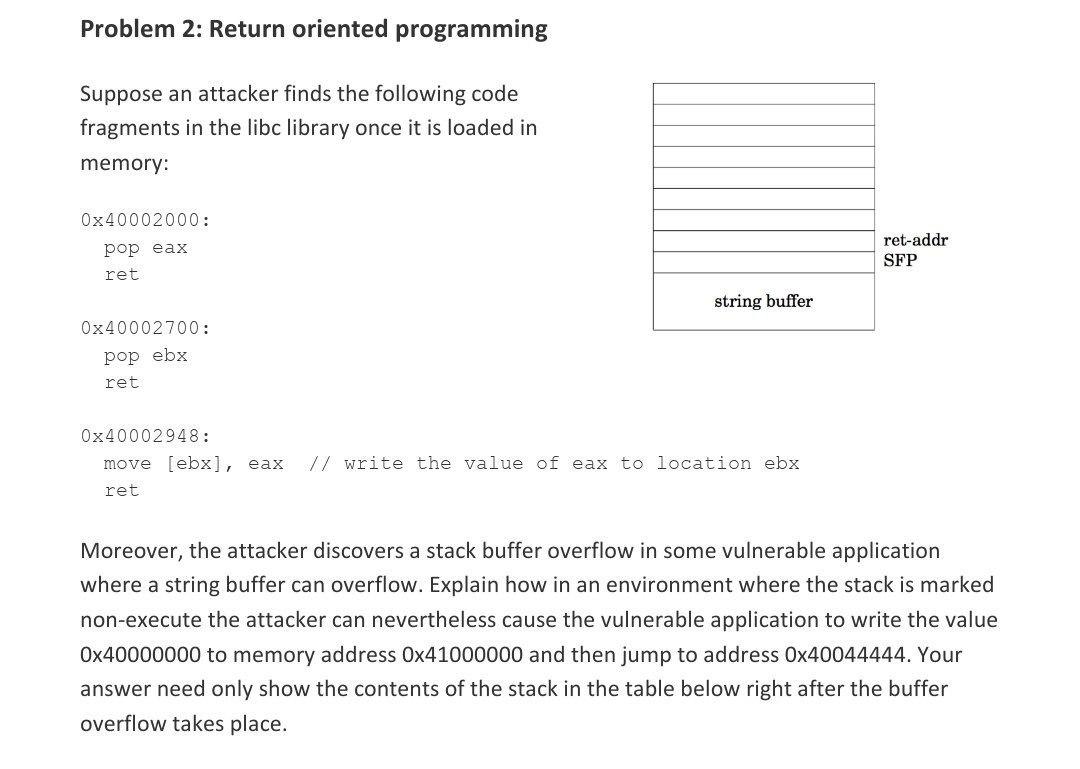
Problem 2: Return oriented programming Suppose an attacker finds the following code fragments in the libc library once it is loaded in memory: Ox40002000: pop eax ret ret-addr SFP string buffer Ox40002700: pop ebx ret Ox40002948: move [ebx], eax ret // rite the value of eax to ocation ebx Moreover, the attacker discovers a stack buffer overflow in some vulnerable application where a string buffer can overflow. Explain how in an environment where the stack is marked non-execute the attacker can nevertheless cause the vulnerable application to write the value 0x40000000 to memory address 0x41000000 and then jump to address 0x40044444. Your answer need only show the contents of the stack in the table below right after the buffer overflow takes place
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


